We at Crack4sure are committed to giving students who are preparing for the Nutanix NCP-MCI-7.5 Exam the most current and reliable questions . To help people study, we've made some of our Nutanix Certified Professional - Multicloud Infrastructure (NCP-MCI) 7.5 exam materials available for free to everyone. You can take the Free NCP-MCI-7.5 Practice Test as many times as you want. The answers to the practice questions are given, and each answer is explained.
The administrator expanded a Nutanix cluster repurposed nodes from a decommissioned cluster. The administrator has validated the following:
Same number of cores, amount of memory and storage
The nodes are on the same subnet
The nodes are running the same version of AOS and AHV
After the nodes were added the administrator discovered that VMs cannot be migrated to the recently added nodes.
What would be the reason for this issue?
An administrator needs to enable Marketplace in Prism Central before deploying Nutanix apps.
Which prerequisite must be met on the Prism Element cluster hosting Prism Central to enable Marketplace?
An administrator reverts a VM to a recovery point using Prism Central. What is the expected behavior for the VM ' s categories and ownership after the revert?
An administrator needs to be able to use remaining capacity for storage and memory.
What settings should the administrator set to accomplish this?
An administrator supports multiple AHV clusters under Prism Central and uses Intelligent Operations playbooks for remediation.
The organization recently standardized alert policies, but the alert policy names and IDs change between environments due to automated deployments and periodic updates.
The requirement is to trigger a remediation playbook for any alert that matches a defined performance pattern (for example, impact type and severity plus a keyword pattern), regardless of which specific alert policy generated it, while avoiding unrelated non-performance alerts.
Which playbook trigger best meets the requirement?
A Windows VM will be cloned repeatedly and each clone needs OS-level customization during deployment.
What is the most efficient method to accomplish this task?
An administrator decided to simplify volume group management by automatically enabling vDisk load balancing for better performance.
How can the administrator enabled vDisk load balancing by default for volume groups?
An administrator needs to move a running VM to another host in the same cluster without shutting it down.
Which is the best way to achive this task?
How many S3 targets are supported for Prism Central point-in-time backups?
An administrator is tasked with configuring asynchronous replication between two Availability Zones (AZs) using a Protection Policy.
Which requirement must be met to successfully configure asynchronous replication?
How many storage pools and storage containers are created during cluster creation?
Which storage-optimization method is recommended for full clone VDI workloads?
An administrator manages a shared AHV environment where Dev workloads must not exceed 2,000 IOPS per VM during business hours to prevent noisy-neighbor impact on Prod.
The administrator already uses categories to group VMs (for example, category Env=Dev) and wants a scalable approach that applies consistent throttling to all current and future Dev VMs without configuring each VM individually.
Which approach best meets the requirement?
While configuring a remote site for PD-Based DR, an administrator elects to skip vStore mapping. Assuming the same container names don ' t exist on the two sites, what is the expected behavior of data placement at the remote site for replications?
A VM is protected by a protection policy and the volume group is configured with CHAP authentication. An administrator rotates the VM’s password as part of the monthly routine. What action must the administrator perform to ensure the password is retained in the event of a failover?
Refer to Exhibit:
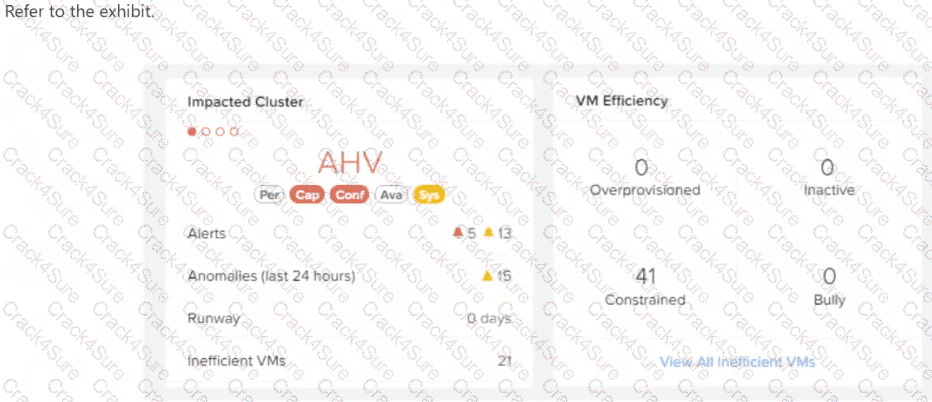
After logging into Prism Central, an administrator observes that there are a large number of constrained VMs.
What does this indicate about those VMs?
When the administrator attempts to configure a Volume Group and connect an external iSCSI initiator, the connection fails. Which cluster configuration step did the administrator most likely miss?
An administrator is troubleshooting intermittent VM I/O stalls that appear across hosts and clusters.
The issue is sporadic, and the administrator needs to rapidly collect the correct platform logs for deeper analysis and possible escalation. The administrator wants to use a supported mechanism designed for efficient log collection, and must ensure the environment prerequisites are met so the tool can be used successfully.
Which option correctly describes the supported approach and a key prerequisite?
A corporate security policy mandates strict protection against boot-level rootkits and requires the isolation of NTLM password hashes from the running operating system to prevent " pass-the-hash " attacks.
During the initial testing phase, the administrator deploys a test VM using the standard AHV creation workflow. While configuring the guest operating system, administrator attempts to enable Windows Defender Credential Guard via Group Policy. However, the feature fails to start, and the system logs indicate that the underlying virtualization platform does not meet the necessary hardware security requirements.
Which specific configuration change must the administrator apply to the VM to satisfy the security policy requirements?
Due to user complaints of slow VM performance, an administrator is reviewing performance metrics on their Nutanix cluster and executes iostat on a Controller VM (CVM).
The following output is captured:
#TIMESTAMP 1768953673 : 01/21/2026 12:01:13 AM
avg-cpu: %user %nice %system %iowait %steal %idle
2.32 0.09 7.53 83.20 0.00 6.86
Based on this output, which statement most accurately describes the current state of the CVM?
An administrator would like to upgrade LCM (Life Cycle Management) to the latest version on an AHV cluster. Which step should the administrator take to guarantee LCM is upgraded to the latest version?
Which setting will ensure a specific storage container maintains a minimum amount of available storage, even if other containers in the same storage pool are consuming space?
A company has recently purchased five new Nutanix clusters. The lab manager has been tasked with remotely deploying the Nutanix infrastructure in the most efficient way possible. Which tool would best help to accomplish this task?
An administrator is configuring Runway Analysis settings in Prism Central and selects Auto Detect under Reserve Capacity For Failure.
How will runway capacity be calculated in this configuration?
What is the RPO time, in hours, for Prism Central backups?
An administrator needs to protect a group of mission-critical virtual machines.
The business requirements are:
Recovery Point Objective (RPO) must be set to 5 minutes.
New mission critical VMs should be automatically protected.
Which data protection type supports this configuration?
An administrator is deploying a new cluster with dense storage. Each node will have 100TB of storage. How many logical cores will be assigned to each CVM?
During an LCM upgrade, the pre-check test_ahv_entering_mm_pinned_vms pre-check fails on an AHV host. The administrator reviews the listed VMs and finds that:
One VM is configured as an Agent VM
Two VMs are running Windows Defender Credential Guard
One VM has a vGPU-enabled
Based on the behavior of this pre-check, which action is required to allow the host to enter maintenance mode and proceed with the LCM upgrade?
3 Months Free Update
3 Months Free Update
3 Months Free Update