We at Crack4sure are committed to giving students who are preparing for the Nutanix NCP-NS-7.5 Exam the most current and reliable questions . To help people study, we've made some of our Nutanix Certified Professional - Network and Security (NCP-NS) 7.5 exam materials available for free to everyone. You can take the Free NCP-NS-7.5 Practice Test as many times as you want. The answers to the practice questions are given, and each answer is explained.
What is the first step in preparing a Nutanix cluster for Flow Virtual Networking?
An administrator has a requirement to capture application flow data for a policy in Monitor mode and export those events to an external SIEM for correlation with other logs. Which two actions are required to achieve this? (Choose two.)
An administrator recently deployed a new set of virtual machines... 3-tier web application... restricted as follows: Only application VMs can talk to database VMs on port 3306 Frontend VMs should only communicate with application VMs on port 8080 Which action will correctly create and configure the Security Policies in Nutanix Flow to satisfy this task?
What does placing a policy in Monitor mode accomplish?
An administrator is deploying a multi-tier (web, app, database) application on a Nutanix cluster using AHV. The administrator needs to allow internal communication between tiers and provide external access to the web tier. How should the administrator satisfy this requirement?
Which step is required before placing the Flow Network Security software bundle on a local web server?
When creating a VPC, enabling the Transit VPC toggle changes the role of the VPC. What does the Transit VPC toggle do?
An administrator needs to delegate the management of security policies to a dedicated SecOps team. To enforce the principle of least privilege, the administrator assigns the predefined Flow Policy Author role to a user on the team. The user confirms they can create, monitor, and enforce security policies. However, when attempting to build a new application security policy for a set of newly deployed VMs, the user reports they are unable to create a new category to group these VMs. The option is not available in the Prism Central UI. Which statement explains this behavior?
An administrator has two user VPCs connected via a Transit VPC. Routing works for most subnets, but one overlay subnet cannot reach external networks. What is the most probable cause?
An administrator creates an Isolation Policy in Prism Central to prevent communication between the Prod and Staging environments. The policy is in Enforce mode... but VMs in the two environments can still communicate. Which configuration issue most likely explains why the Isolation Policy is not blocking the traffic?
An administrator has observed the following message: Which two statements most accurately describe the security hitlog captured above? (Choose two.)
An administrator has configured two VPCs with overlapping externally routable prefixes (ERPs). The two VPCs are associated to separate external networks that are part of the same physical routing domain. What outcome should the administrator expect?
An administrator observes a Network Controller Unreachable alert in Prism Central for a specific AHV cluster. All other management tasks for the cluster from Prism Central are succeeding and the cluster itself reports a healthy status. Which step is the most appropriate to investigate the cause of this specific alert?
The alert details mention a specific external network. Attempts to assign new Floating IPs to VMs fail, but existing Floating IPs continue to work. What is the cause of this alert?
An administrator needs to configure a security policy that controls VM-to-VM communication within a category defined as secured entity. Which configuration action should the administrator take to restrict all intra-tier communication between the VMs within a category defined as secured entity?
An administrator needs to ensure all web traffic (HTTP/HTTPS) from a specific subnet (10.100.20.0/24) is redirected through a third-party virtual firewall inside the VPC for Layer 7 inspection before reaching the internet. The firewall VM has an IP of 10.100.30.5 and is connected to a different subnet. What should be done to enforce this specific traffic path?
When setting up a Network Function VM for Service Insertion, an administrator needs to configure the vNICs that will be used for redirecting traffic. What is the correct configuration for the vNICs on the Network Function VM?
In a Nutanix deployment, when is the Network Controller automatically enabled?
A junior network operator is assigned two predefined roles in Prism Central... Role A: Prism Viewer Role B: VPC Admin The operator reports being able to successfully create, update, and delete Virtual Private Clouds (VPCs). However, the operator is unable to create a VM into the VPC. How does Prism Central determine the operator's effective permissions?
An administrator must delegate management of a single tenant VPC to a junior engineer. The engineer should be able to modify that VPC but must not see or change any other VPCs or networking configurations in Prism Central. The administrator wants to meet this requirement using RBAC. Which action should the administrator take to meet this requirement?
An administrator plans to upgrade a Nutanix cluster running AHV and Prism Central. The current cluster is on AOS 6.10, and the administrator wants to move to AOS 7.3 while ensuring all components remain compatible. What is the correct upgrade order to minimize downtime and maintain cluster functionality?
Refer to Exhibit:
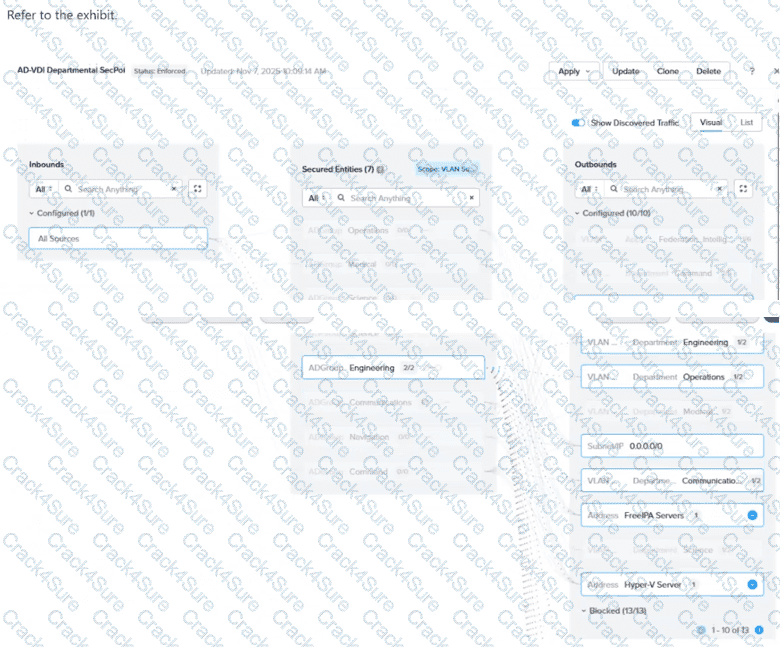
In the AD-VDI Departmental SecPol policy shown in the exhibit, ADGroup: Engineering is configured as a secured entity in a VDI Security Policy. Prism Central shows 2 / 2 active sessions under this group, but the administrator confirms that three Engineering users are currently logged in to persistent VDI desktops. The third user's VM shows no ADGroup assignment in its VM details in Prism Central, even after the user has successfully logged in. All three users are members of the same AD group, and the Domain Controller event logs confirm a successful interactive login for the third user. Which condition explains why the third user's VM is not being assigned the ADGroup: Engineering category?
Which policy is used to isolate a compromised VM in the most efficient way possible?
A customer wants to extend a VLAN subnet to a remote data center using VTEP. The administrator configures a Subnet Extension which shows UP in the Prism Interface, yet traffic fails to pass. Which setting is most likely misconfigured?
Refer to Exhibit:
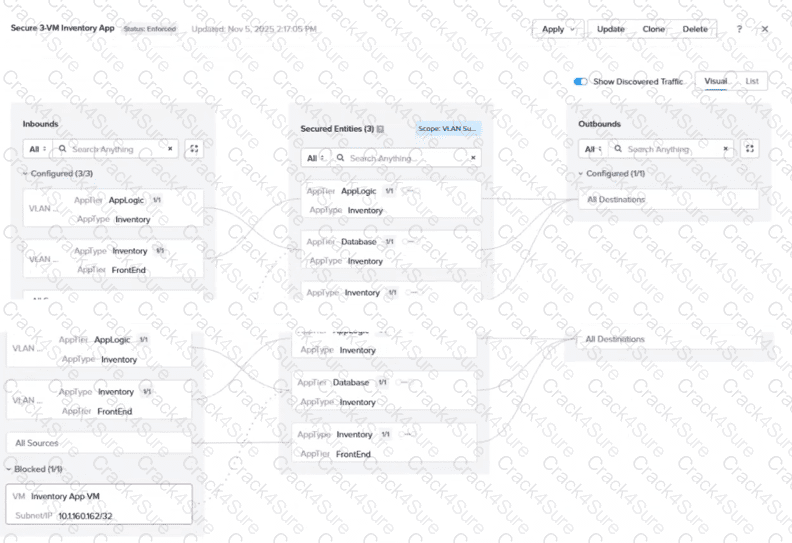
An administrator is reviewing an enforced security policy "Secure 3-VM Inventory App", as shown in the exhibit. The policy's inbound rules are configured to allow traffic from specific sources to each tier of the application. The visualization shows one blocked traffic flow. Based on the information presented in the exhibit, which statement best describes this behavior?
A service-insertion firewall VM protects user VMs access to the internet. The virtual and physical switches, as well as all user VMs, currently use the default MTU size of 1500. Everything functions normally until a user VM is migrated to another host. After the migration, the user reports that some websites fail to load while ping to those same sites still succeeds. Routing and security policies appear normal. Which two configuration changes could resolve the issue? (Choose two.)
3 Months Free Update
3 Months Free Update
3 Months Free Update