We at Crack4sure are committed to giving students who are preparing for the Paloalto Networks PCNSA Exam the most current and reliable questions . To help people study, we've made some of our Palo Alto Networks Certified Network Security Administrator (PAN-OS 10.0) exam materials available for free to everyone. You can take the Free PCNSA Practice Test as many times as you want. The answers to the practice questions are given, and each answer is explained.
What is a recommended consideration when deploying content updates to the firewall from Panorama?
Access to which feature requires the PAN-OS Filtering license?
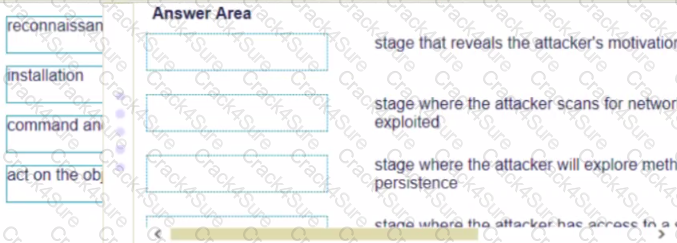
Match the cyber-attack lifecycle stage to its correct description.
What can be achieved by selecting a policy target prior to pushing policy rules from Panorama?
Match the Cyber-Attack Lifecycle stage to its correct description.
Prior to a maintenance-window activity, the administrator would like to make a backup of only the running configuration to an external location.
What command in Device > Setup > Operations would provide the most operationally efficient way to achieve this outcome?
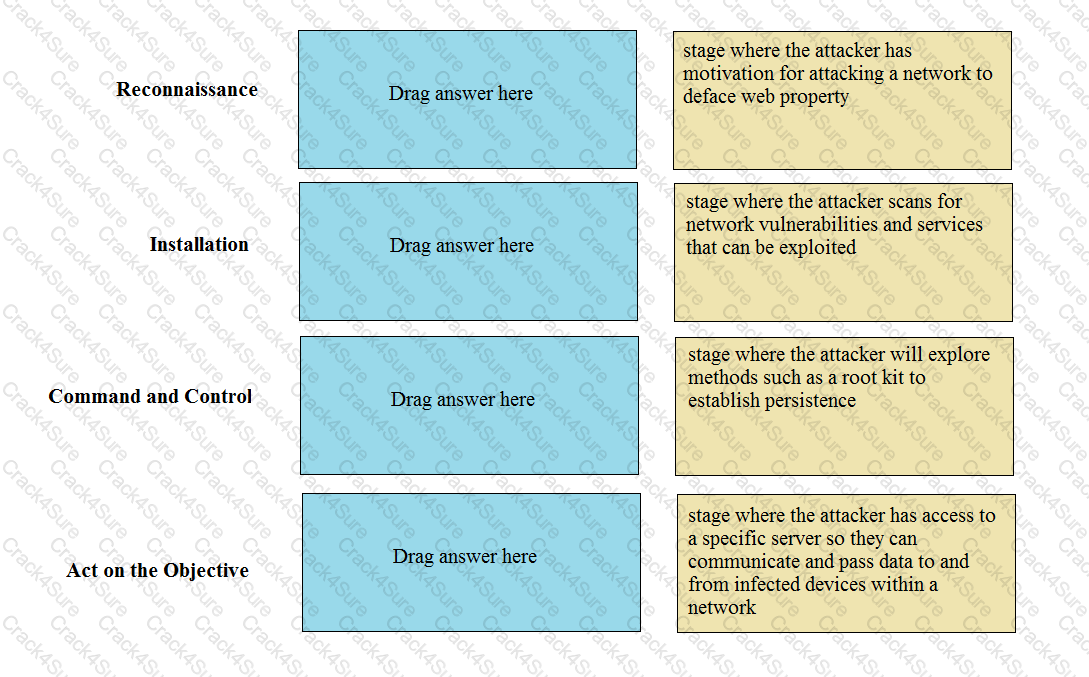
When creating a Source NAT policy, which entry in the Translated Packet tab will display the options Dynamic IP and Port, Dynamic, Static IP, and None?
Which interface type is part of a Layer 3 zone with a Palo Alto Networks firewall?
Which policy set should be used to ensure that a policy is applied just before the default security rules?
Which type of administrative role must you assign to a firewall administrator account, if the account must include a custom set of firewall permissions?
Which type of address object is "10 5 1 1/0 127 248 2"?
Which prevention technique will prevent attacks based on packet count?
Which object would an administrator create to enable access to all applications in the office-programs subcategory?
How frequently can wildfire updates be made available to firewalls?
What is an advantage for using application tags?
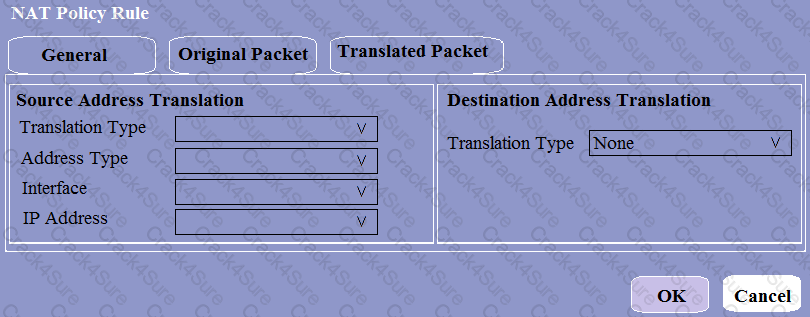
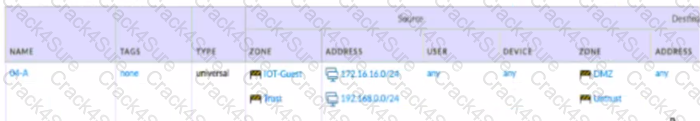
View the diagram. What is the most restrictive, yet fully functional rule, to allow general Internet and SSH traffic into both the DMZ and Untrust/lnternet zones from each of the lOT/Guest and Trust Zones?
A)

B)
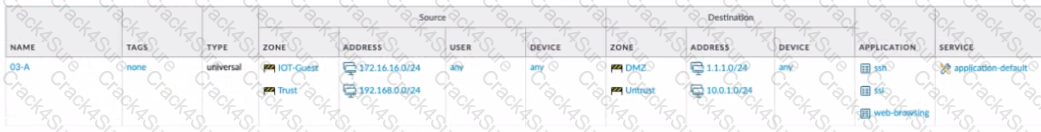
C)

D)

Which option lists the attributes that are selectable when setting up an Application filters?
Why does a company need an Antivirus profile?
What does an administrator use to validate whether a session is matching an expected NAT policy?
What allows a security administrator to preview the Security policy rules that match new application signatures?
Which three filter columns are available when setting up an Application Filter? (Choose three.)
To what must an interface be assigned before it can process traffic?
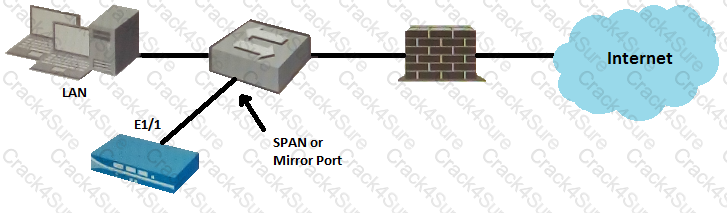
Given the topology, which zone type should interface E1/1 be configured with?
Which three types of entries can be excluded from an external dynamic list (EDL)? (Choose three.)
Which Security policy match condition would an administrator use to block traffic from IP addresses on the Palo Alto Networks EDL of Known Malicious IP Addresses list?
Which Security profile would you apply to identify infected hosts on the protected network uwall user database?
Based on the screenshot what is the purpose of the group in User labelled ''it"?

Which two Palo Alto Networks security management tools provide a consolidated creation of policies, centralized management and centralized threat intelligence. (Choose two.)
Which path is used to save and load a configuration with a Palo Alto Networks firewall?
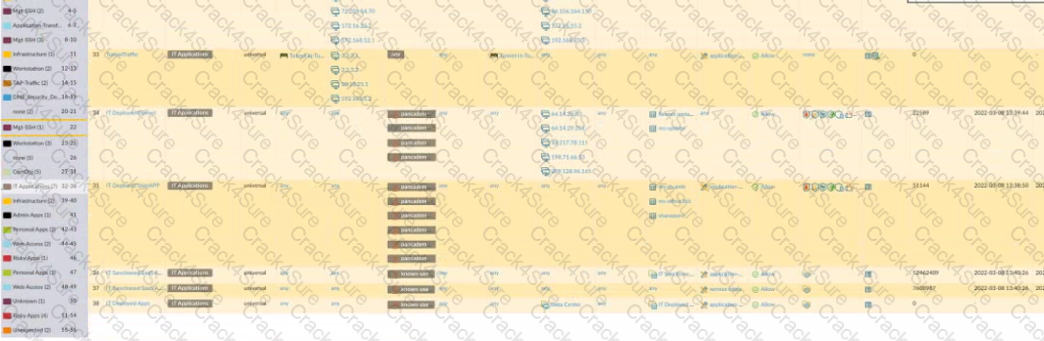
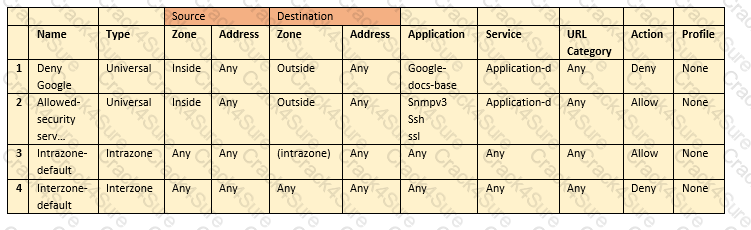
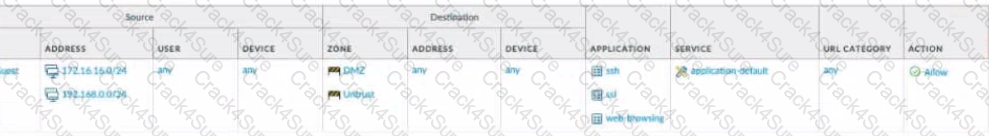
An administrator is reviewing the Security policy rules shown in the screenshot below.
Which statement is correct about the information displayed?
Which firewall plane provides configuration, logging, and reporting functions on a separate processor?
Which two features implement one-to-one translation of a source IP address while allowing the source port to change? (Choose two.)
Which license must an administrator acquire prior to downloading Antivirus updates for use with the firewall?
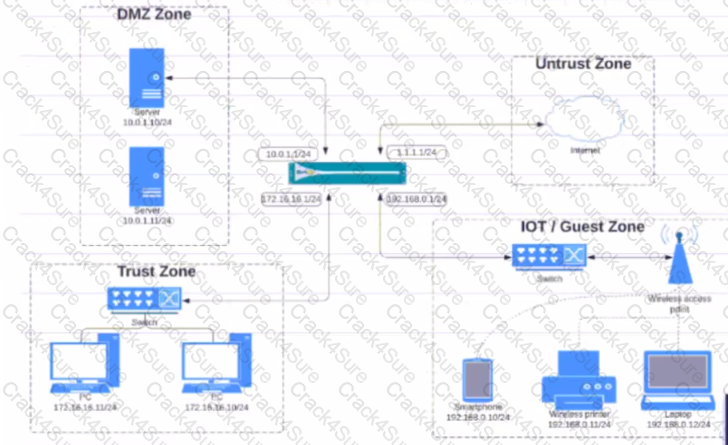
Given the network diagram, traffic should be permitted for both Trusted and Guest users to access general Internet and DMZ servers using SSH. web-browsing and SSL applications
Which policy achieves the desired results?
A)
B)
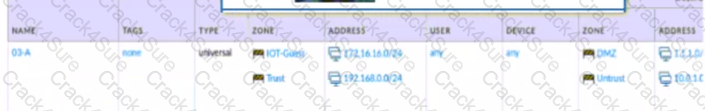
C)

D)

Which two matching criteria are used when creating a Security policy involving NAT? (Choose two.)
Which statements is true regarding a Heatmap report?
Given the screenshot, what are two correct statements about the logged traffic? (Choose two.)

The PowerBall Lottery has reached a high payout amount and a company has decided to help employee morale by allowing employees to check the number, but doesn’t want to unblock the gambling URL category.
Which two methods will allow the employees to get to the PowerBall Lottery site without the company unlocking the gambling URL category? (Choose two.)
Which three statement describe the operation of Security Policy rules or Security Profiles? (Choose three)
A network administrator is required to use a dynamic routing protocol for network connectivity.
Which three dynamic routing protocols are supported by the NGFW Virtual Router for this purpose? (Choose three.)
An administrator is trying to enforce policy on some (but not all) of the entries in an external dynamic list. What is the maximum number of entries that they can be exclude?
What action will inform end users when their access to Internet content is being restricted?
Which action can be set in a URL Filtering Security profile to provide users temporary access to all websites in a given category using a provided password?
Which statement best describes the use of Policy Optimizer?
An administrator has an IP address range in the external dynamic list and wants to create an exception for one specific IP address in this address range.
Which steps should the administrator take?
Why should a company have a File Blocking profile that is attached to a Security policy?
What is the purpose of the automated commit recovery feature?
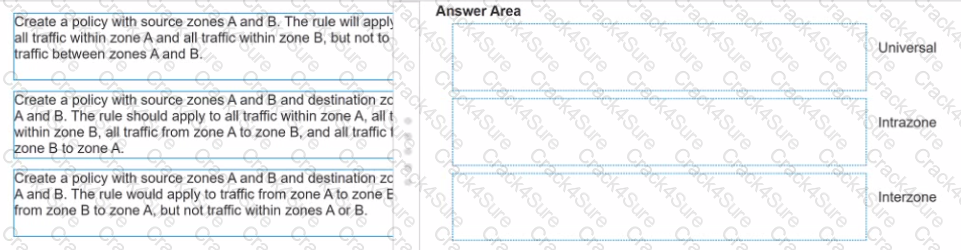
Match each rule type with its example
Which administrator receives a global notification for a new malware that infects hosts. The infection will result in the infected host attempting to contact and command-and-control (C2) server.
Which security profile components will detect and prevent this threat after the firewall`s signature database has been updated?
What is the minimum timeframe that can be set on the firewall to check for new WildFire signatures?
An administrator should filter NGFW traffic logs by which attribute column to determine if the entry is for the start or end of the session?
Which file is used to save the running configuration with a Palo Alto Networks firewall?
The firewall sends employees an application block page when they try to access Youtube.
Which Security policy rule is blocking the youtube application?
What is the best-practice approach to logging traffic that traverses the firewall?
Which type of security rule will match traffic between the Inside zone and Outside zone, within the Inside zone, and within the Outside zone?
Which two features can be used to tag a user name so that it is included in a dynamic user group? (Choose two)
How many zones can an interface be assigned with a Palo Alto Networks firewall?
Which three types of authentication services can be used to authenticate user traffic flowing through the firewalls data plane? (Choose three )
What are three valid source or D=destination conditions available as Security policy qualifiers? (Choose three.)
An administrator manages a network with 300 addresses that require translation. The administrator configured NAT with an address pool of 240 addresses and found that connections from addresses that needed new translations were being dropped.
Which type of NAT was configured?
Which security profile will provide the best protection against ICMP floods, based on individual combinations of a packet`s source and destination IP address?
What are the two main reasons a custom application is created? (Choose two.)
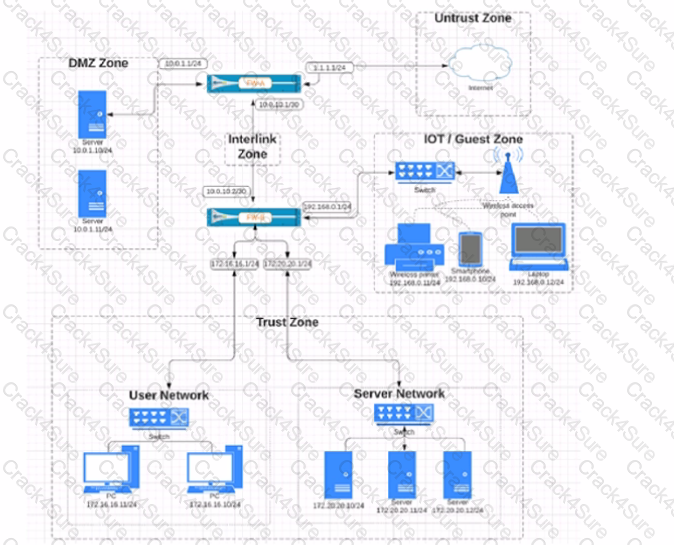
Based on the network diagram provided, which two statements apply to traffic between the User and Server networks? (Choose two.)
Which rule type is appropriate for matching traffic occurring within a specified zone?
A systems administrator momentarily loses track of which is the test environment firewall and which is the production firewall. The administrator makes changes to the candidate configuration of the production firewall, but does not commit the changes. In addition, the configuration was not saved prior to
making the changes.
Which action will allow the administrator to undo the changes?
An administrator would like to see the traffic that matches the interzone-default rule in the traffic logs.
What is the correct process to enable this logging1?
What is considered best practice with regards to committing configuration changes?
How can a complete overview of the logs be displayed to an administrator who has permission in the system to view them?
A network administrator creates an intrazone security policy rule on a NGFW. The source zones are set to IT. Finance, and HR.
To which two types of traffic will the rule apply? (Choose two.)
What are two differences between an implicit dependency and an explicit dependency in App-ID? (Choose two.)
Where in Panorama Would Zone Protection profiles be configured?
View the diagram.
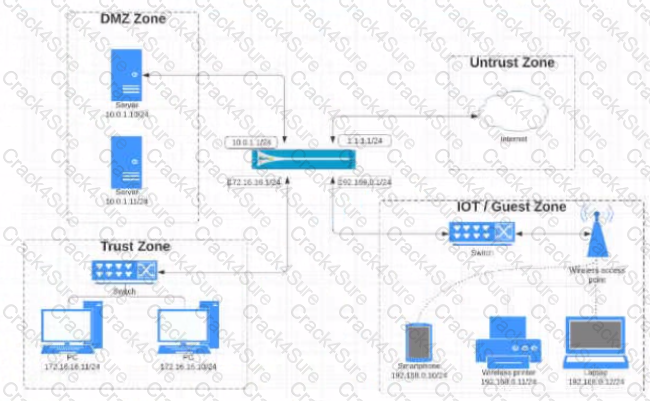
What is the most restrictive yet fully functional rule to allow general Internet and SSH traffic into both the DMZ and Untrust/lnternet zones from each of the lOT/Guest and Trust Zones?
A)
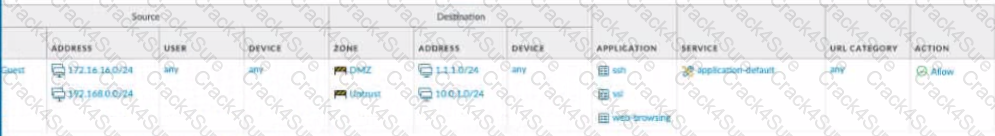
B)
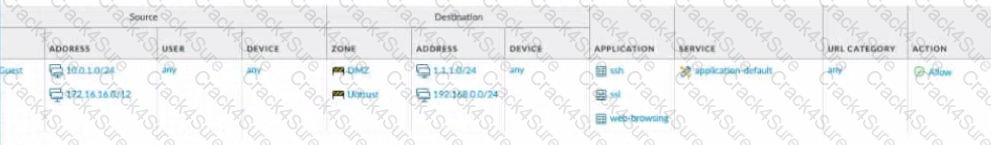
C)

D)
Which System log severity level would be displayed as a result of a user password change?
Which protocol used to map username to user groups when user-ID is configured?
The administrator profile "SYS01 Admin" is configured with authentication profile "Authentication Sequence SYS01," and the authentication sequence SYS01 has a profile list with four authentication profiles:
• Auth Profile LDAP
• Auth Profile Radius
• Auth Profile Local
• Auth Profile TACACS
After a network outage, the LDAP server is no longer reachable. The RADIUS server is still reachable but has lost the "SYS01 Admin" username and password.
What is the "SYS01 Admin" login capability after the outage?
Which Security profile can you apply to protect against malware such as worms and Trojans?
Which dynamic update type includes updated anti-spyware signatures?
Which three Ethernet interface types are configurable on the Palo Alto Networks firewall? (Choose three.)
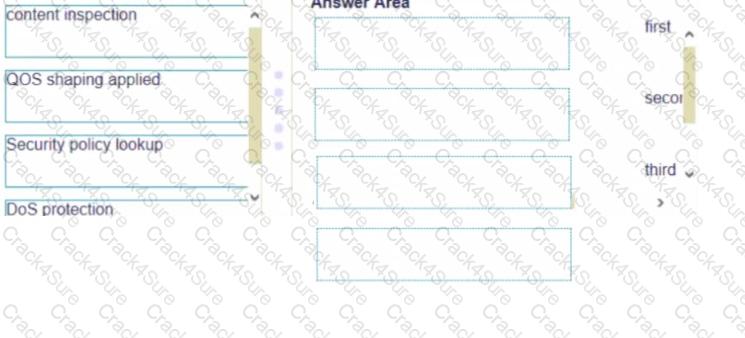
Place the following steps in the packet processing order of operations from first to last.
Which two statements are correct about App-ID content updates? (Choose two.)
Which statement best describes a common use of Policy Optimizer?
Which DNS Query action is recommended for traffic that is allowed by Security policy and matches Palo Alto Networks Content DNS Signatures?
Which Palo Alto Networks firewall security platform provides network security for mobile endpoints by inspecting traffic deployed as internet gateways?
Users from the internal zone need to be allowed to Telnet into a server in the DMZ zone.
Complete the security policy to ensure only Telnet is allowed.
Security Policy: Source Zone: Internal to DMZ Zone __________services “Application defaults”, and action = Allow
What is a default setting for NAT Translated Packets when the destination NAT translation is selected as Dynamic IP (with session distribution)?
Which two actions are needed for an administrator to get real-time WildFire signatures? (Choose two.)
Which feature enables an administrator to review the Security policy rule base for unused rules?
Which URL profiling action does not generate a log entry when a user attempts to access that URL?
An administrator would like to override the default deny action for a given application and instead would like to block the traffic and send the ICMP code "communication with the destination is administratively prohibited"
Which security policy action causes this?
Which Security policy set should be used to ensure that a policy is applied first?
A network has 10 domain controllers, multiple WAN links, and a network infrastructure with bandwidth needed to support mission-critical applications. Given the scenario, which type of User-ID agent is considered a best practice by Palo Alto Networks?
What do dynamic user groups you to do?
When creating a custom URL category object, which is a valid type?
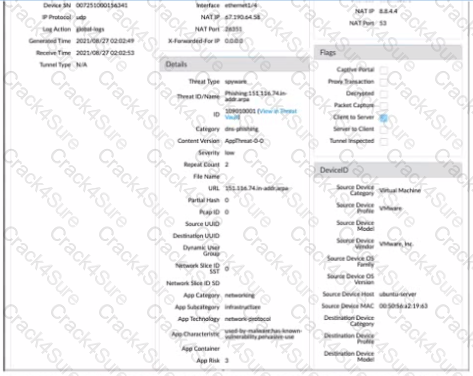
Given the detailed log information above, what was the result of the firewall traffic inspection?
Which type security policy rule would match traffic flowing between the inside zone and outside zone within the inside zone and within the outside zone?
If using group mapping with Active Directory Universal Groups, what must you do when configuring the User-ID?
An organization has some applications that are restricted for access by the Human Resources Department only, and other applications that are available for any known user in the organization.
What object is best suited for this configuration?
Which the app-ID application will you need to allow in your security policy to use facebook-chat?
Which license must an Administrator acquire prior to downloading Antivirus Updates for use with the firewall?
Based on the screenshot presented which column contains the link that when clicked opens a window to display all applications matched to the policy rule?

The NetSec Manager asked to create a new firewall Local Administrator profile with customized privileges named NewAdmin. This new administrator has to authenticate without inserting any username or password to access the WebUI.
What steps should the administrator follow to create the New_Admin Administrator profile?
An administrator would like to use App-ID's deny action for an application and would like that action updated with dynamic updates as new content becomes available.
Which security policy action causes this?
Which two rule types allow the administrator to modify the destination zone? (Choose two )