We at Crack4sure are committed to giving students who are preparing for the Paloalto Networks Practitioner Exam the most current and reliable questions . To help people study, we've made some of our Palo Alto Networks Cybersecurity Practitioner (PCCP) exam materials available for free to everyone. You can take the Free Practitioner Practice Test as many times as you want. The answers to the practice questions are given, and each answer is explained.
Which item accurately describes a security weakness that is caused by implementing a “ports first” data security solution in a traditional data center?
Which pillar of Prisma Cloud application security does vulnerability management fall under?
Which endpoint tool or agent can enact behavior-based protection?
Which Palo Alto Networks tools enable a proactive, prevention-based approach to network automation that accelerates security analysis?
Which two statements apply to the SSL/TLS protocol? (Choose two.)
Which tool's analysis data gives security operations teams insight into their environment's risks from exposed services?
Which type of IDS/IPS uses a baseline of normal network activity to identify unusual patterns or levels of network activity that may be indicative of an intrusion attempt?
Which attacker profile uses the internet to recruit members to an ideology, to train them, and to spread fear and include panic?
Which Palo Alto subscription service identifies unknown malware, zero-day exploits, and advanced persistent threats (APTs) through static and dynamic analysis in a scalable, virtual environment?
What does SIEM stand for?
Organizations that transmit, process, or store payment-card information must comply with what standard?
Which option is a Prisma Access security service?
Which MITRE ATT&CK tactic grants increased permissions to a user account for internal servers of a corporate network?
Under which category does an application that is approved by the IT department, such as Office 365, fall?
In which situation would a dynamic routing protocol be the quickest way to configure routes on a router?
Which Palo Alto Networks product provides playbooks with 300+ multivendor integrations that help solve any security use case?
What are two key characteristics of a Type 1 hypervisor? (Choose two.)
Routing Information Protocol (RIP), uses what metric to determine how network traffic should flow?
Which native Windows application can be used to inspect actions taken at a specific time?
Which statement describes the process of application allow listing?
Based on how much is managed by the vendor, where can CaaS be situated in the spread of cloud computing services?
What type of area network connects end-user devices?
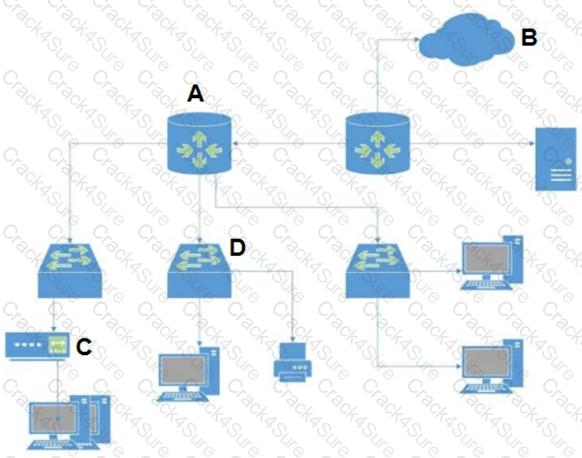
In the attached network diagram, which device is the switch?
What should a security operations engineer do if they are presented with an encoded string during an incident investigation?
Which IPsec feature allows device traffic to go directly to the Internet?
Which NGFW feature is used to provide continuous identification, categorization, and control of known and previously unknown SaaS applications?
Which network firewall operates up to Layer 4 (Transport layer) of the OSI model and maintains information about the communication sessions which have been established between hosts on trusted and untrusted networks?
What are three benefits of SD-WAN infrastructure? (Choose three.)
Which of the following is a Routed Protocol?
Which statement describes a host-based intrusion prevention system (HIPS)?
TCP is the protocol of which layer of the OSI model?
Which classification of IDS/IPS uses a database of known vulnerabilities and attack profiles to identify intrusion attempts?
In addition to integrating the network and endpoint components, what other component does Cortex integrate to speed up IoC investigations?
Which type of Wi-Fi attack depends on the victim initiating the connection?
What is a purpose of workload security on a Cloud Native Security Platform (CNSP)?
Which component of the AAA framework verifies user identities so they may access the network?
What would allow a security team to inspect TLS encapsulated traffic?
Which option describes the “selective network security virtualization” phase of incrementally transforming data centers?
Which protocol is used by both internet service providers (ISPs) and network service providers (NSPs)?
How does adopting a serverless model impact application development?
A high-profile company executive receives an urgent email containing a malicious link. The sender appears to be from the IT department of the company, and the email requests an update of the executive's login credentials for a system update.
Which type of phishing attack does this represent?
Which element of the security operations process is concerned with using external functions to help achieve goals?
What is a key benefit of Cortex XDR?
Which endpoint product from Palo Alto Networks can help with SOC visibility?
Anthem server breaches disclosed Personally Identifiable Information (PII) from a number of its servers. The infiltration by hackers was attributed to which type of vulnerability?
In an IDS/IPS, which type of alarm occurs when legitimate traffic is improperly identified as malicious traffic?
A native hypervisor runs:
On an endpoint, which method is used to protect proprietary data stored on a laptop that has been stolen?
Why have software developers widely embraced the use of containers?
Which next-generation firewall (NGFW) deployment option provides full application visibility into Kubernetes environments?
How does DevSecOps improve the Continuous Integration/Continuous Deployment (CI/CD) pipeline?
Which of the Cloud-Delivered Security Services (CDSS) will detect zero-day malware by using inline cloud machine learning (ML) and sandboxing?
What are two examples of an attacker using social engineering? (Choose two.)
What is a characteristic of the National Institute Standards and Technology (NIST) defined cloud computing model?
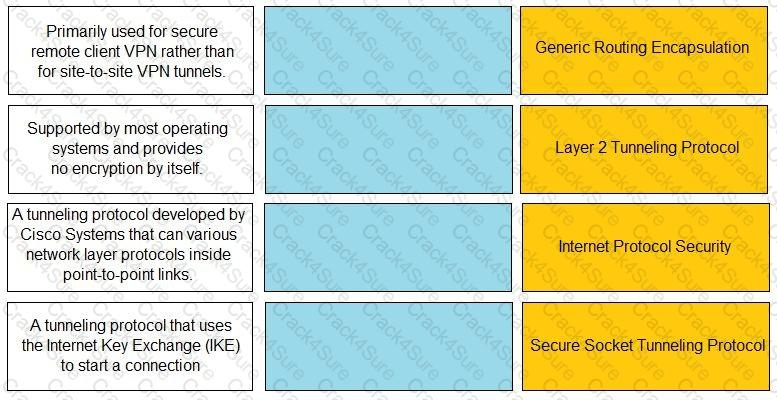
Match the description with the VPN technology.
What differentiates SOAR from SIEM?
What are two advantages of security orchestration, automation, and response (SOAR)? (Choose two.)
What does SOAR technology use to automate and coordinate workflows?
Which technology secures software-as-a-service (SaaS) applications and network data, and also enforces compliance policies for application access?
Which technology helps Security Operations Center (SOC) teams identify heap spray attacks on company-owned laptops?
In which step of the cyber-attack lifecycle do hackers embed intruder code within seemingly innocuous files?
Which scenario highlights how a malicious Portable Executable (PE) file is leveraged as an attack?
A doctor receives an email about her upcoming holiday in France. When she clicks the URL website link in the email, the connection is blocked by her office firewall because it's a known malware website. Which type of attack includes a link to a malware website in an email?
3 Months Free Update
3 Months Free Update
3 Months Free Update