We at Crack4sure are committed to giving students who are preparing for the Proofpoint TPAD01 Exam the most current and reliable questions . To help people study, we've made some of our Threat Protection Administrator Exam exam materials available for free to everyone. You can take the Free TPAD01 Practice Test as many times as you want. The answers to the practice questions are given, and each answer is explained.
You need to generate a report from the Cloud Admin Interface. What file formats are available to export?
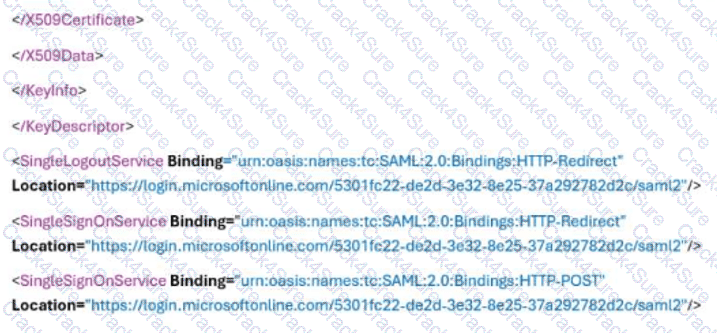
What is the correct SAML Sign-in URL shown in the screenshot?
Smart Search has returned 13 results for a specific recipient address. You click on one of the messages in the Results list. Which of the following information is available for that message?
How does Proofpoint use TLS in email security?
Which of the following is the correct order for SMTP message reception?
You can drag the divider between the question and exhibit to the left to make the image larger.
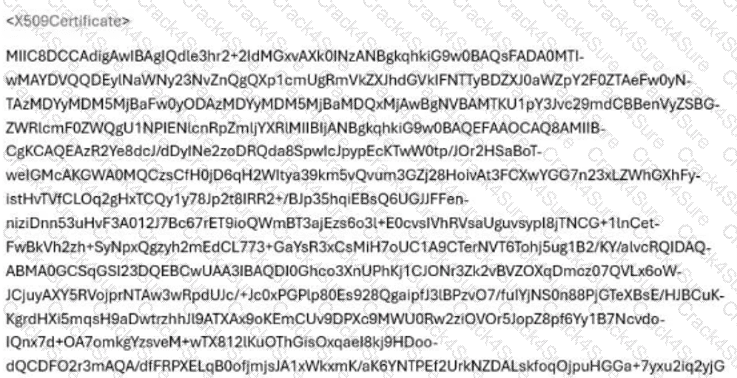
Refer to the exhibit.
You are configuring SSO for Proofpoint Cloud Services, such as Cloud Admin, TAP Dashboard, Cloud Threat Response, CASB, and Identity Threat Response. The Microsoft O365 administrator sends you a portion of the XML file containing the SAML configuration. Which of the following strings should be entered in the “SAML Login Endpoint (required)” field in the Proofpoint Identity Provider Configuration?
You are tasked with configuring outbound mail for an organization where an external domain has multiple MX records. Only one specific host is accepting mail. What is the best way to specify this specific hostname for outbound mail?
During the configuration of an alert profile, which option is specifically required to ensure alerts are delivered to the appropriate individuals?
Which URLs are valid entries for the configuration shown in the screenshot?
When reviewing the Audit Logs in the context of cluster monitoring, what type of information is primarily available?
What is the difference between the Discard and Reject dispositions?
In a scenario where an email is quarantined by both a spam policy (Spam) and an email firewall rule (Dictionary), which folder will the message ultimately be sent to?
The Abuse Mailbox event source was working in Cloud Threat Protection, but is now showing red under status and is no longer processing emails. After editing the source and clicking “Validate Source,” you receive the error “Unable to validate mailbox.” What is the likely cause of this error?
What is the primary purpose of the End User Web Interface in Proofpoint?
What option will release a quarantined message without further filtering?
Which of the following are true regarding Email Warning Tags?
Pick the 2 correct responses below.
3 Months Free Update
3 Months Free Update
3 Months Free Update