Study the Rule base and Client Authentication Action properties screen.
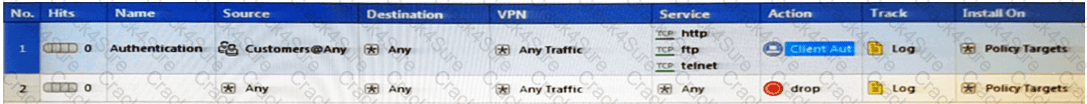

After being authenticated by the Security Gateways, a user starts a HTTP connection to a Web site. What happens when the user tries to FTP to another site using the command line? The:
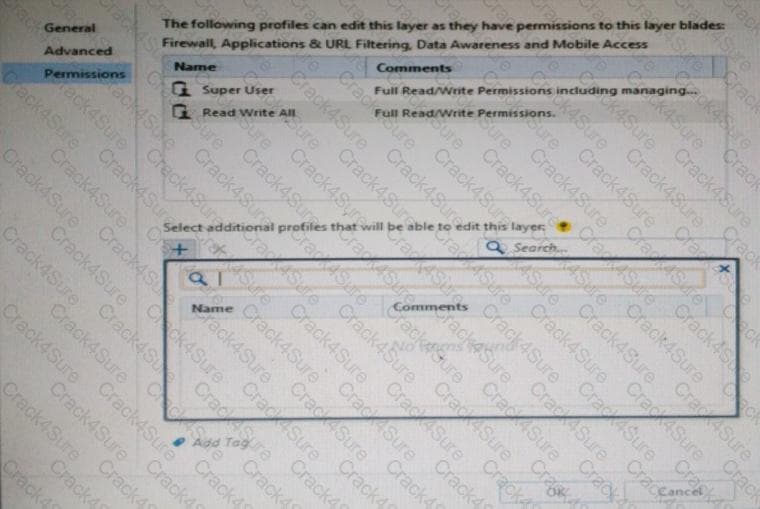
You want to define a selected administrator's permission to edit a layer. However, when you click the + sign in the “Select additional profile that will be able edit this layer” you do not see anything. What is the most likely cause of this problem? Select the BEST answer.
The default method for destination NAT is _____________, where NAT occurs on the Inbound interface closest to the client.
Sally has a Hot Fix Accumulator (HFA) she wants to install on her Security Gateway which operates with GAiA, but she cannot SCP the HFA to the system. She can SSH into the Security Gateway, but she has never been able to SCP files to it. What would be the most likely reason she cannot do so?
The most important part of a site-to-site VPN deployment is the ________ .
Your manager requires you to setup a VPN to a new business partner site. The administrator from the partner site gives you his VPN settings and you notice that he setup AES 128 for IKE phase 1 and AES 256 for IKE phase 2. Why is this a problematic setup?
Which deployment adds a Security Gateway to an existing environment without changing IP routing?
When logging in for the first time to a Security management Server through SmartConsole, a fingerprint is saved to the:
When configuring Spoof Tracking, which tracking actions can an administrator select to be done when spoofed packets are detected?
Can multiple administrators connect to a Security Management Server at the same time?
To view the policy installation history for each gateway, which tool would an administrator use?
Which of the following Windows Security Events will NOT map a username to an IP address in Identity Awareness?
After the initial installation on Check Point appliance, you notice that the Management interface and default gateway are incorrect. Which commands could you use to set the IP to 192.168.80.200/24 and default gateway to 192.168.80.1.
What object type would you use to grant network access to an LDAP user group?
Identify the ports to which the Client Authentication daemon listens on by default?
True or False: In a Distributed Environment, a Central License can be installed via CLI on a Security Gateway
There are 4 ways to use the Management API for creating host object with R80 Management API. Which one is NOT correct?
Which Threat Prevention Software Blade provides protection from malicious software that can infect your network computers?
Vanessa is expecting a very important Security Report. The Document should be sent as an attachment via e-mail. An e-mail with Security_report.pdf file was delivered to her e-mail inbox. When she opened the PDF file, she noticed that the file is basically empty and only few lines of text are in it. The report is missing some graphs, tables and links. Which component of SandBlast protection is her company using on a Gateway?
Which of the following are available SmartConsole clients which can be installed from the R77 Windows CD? Read all answers and select the most complete and valid list.
Which of the following authentication methods can be configured in the Identity Awareness setup wizard?
Which of the following is NOT an option for internal network definition of Anti-spoofing?
Jennifer McHanry is CEO of ACME. She recently bought her own personal iPad. She wants use her iPad to access the internal Finance Web server. Because the iPad is not a member of the Active Directory domain, she cannot identify seamlessly with AD Query. However, she can enter her AD credentials in the Captive Portal and then get the same access as on her office computer. Her access to resources is based on rules in the R77 Firewall Rule Base.
To make this scenario work, the IT administrator must:
1) Enable Identity Awareness on a gateway and select Captive Portal as one of the Identity Sources.
2) In the Portal Settings window in the User Access section, make sure that Name and password login is selected.
3) Create a new rule in the Firewall Rule Base to let Jennifer McHanry access network destinations. Select accept as the Action.
4) Install policy.
Ms McHanry tries to access the resource but is unable. What should she do?
As a Security Administrator, you must refresh the Client Authentication authorized time-out every time a new user connection is authorized. How do you do this? Enable the Refreshable Timeout setting:
Which is the correct order of a log flow processed by SmartEvent components:
A client has created a new Gateway object that will be managed at a remote location. When the client attempts to install the Security Policy to the new Gateway object, the object does not appear in the Install On check box. What should you look for?
Packet acceleration (SecureXL) identifies connections by several attributes. Which of the attributes is NOT used for identifying connection?
An internal router is sending UDP keep-alive packets that are being encapsulated with GRE and sent through your R77 Security Gateway to a partner site. A rule for GRE traffic is configured for ACCEPT/LOG. Although the keep-alive packets are being sent every minute, a search through the SmartView Tracker logs for GRE traffic only shows one entry for the whole day (early in the morning after a Policy install).
Your partner site indicates they are successfully receiving the GRE encapsulated keep-alive packets on the 1-minute interval.
If GRE encapsulation is turned off on the router, SmartView Tracker shows a log entry for the UDP keep-alive packet every minute.
Which of the following is the BEST explanation for this behavior?
You have enabled “Full Log” as a tracking option to a security rule. However, you are still not seeing any data type information. What is the MOST likely reason?
John Adams is an HR partner in the ACME organization. ACME IT wants to limit access to HR servers to designated IP addresses to minimize malware infection and unauthorized access risks. Thus, the gateway policy permits access only from John's desktop which is assigned a static IP address 10.0.0.19.
John received a laptop and wants to access the HR Web Server from anywhere in the organization. The IT department gave the laptop a static IP address, but that limits him to operating it only from his desk. The current Rule Base contains a rule that lets John Adams access the HR Web Server from his desktop with a static IP (10.0.0.19). He wants to move around the organization and continue to have access to the HR Web Server.
To make this scenario work, the IT administrator:
1) Enables Identity Awareness on a gateway, selects AD Query as one of the Identity Sources installs the policy.
2) Adds an access role object to the Firewall Rule Base that lets John Adams PC access the HR Web Server from any machine and from any location.
3) Changes from static IP address to DHCP for the client PC.
What should John request when he cannot access the web server from his laptop?
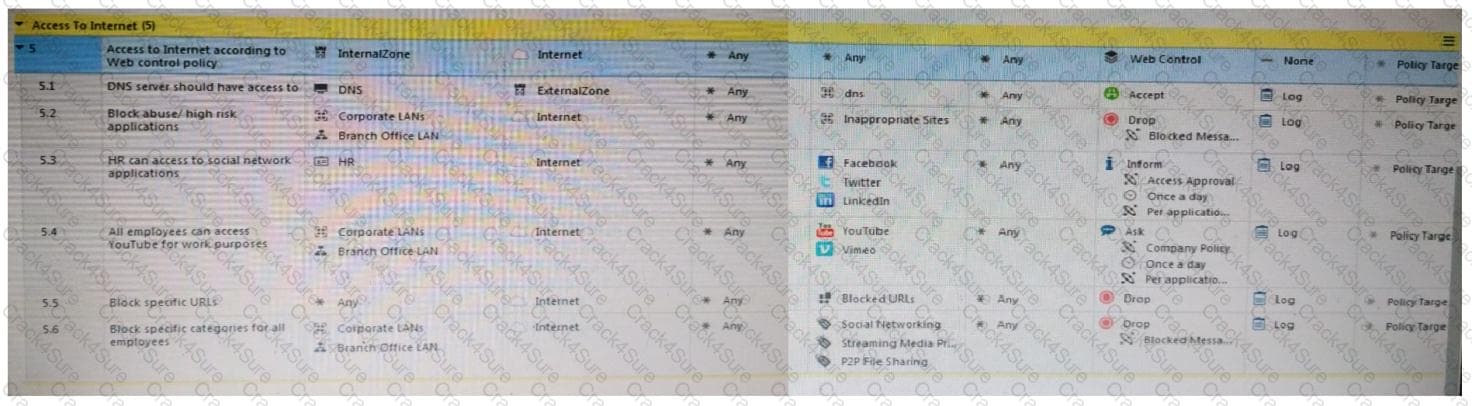
Web Control Layer has been set up using the settings in the following dialogue:
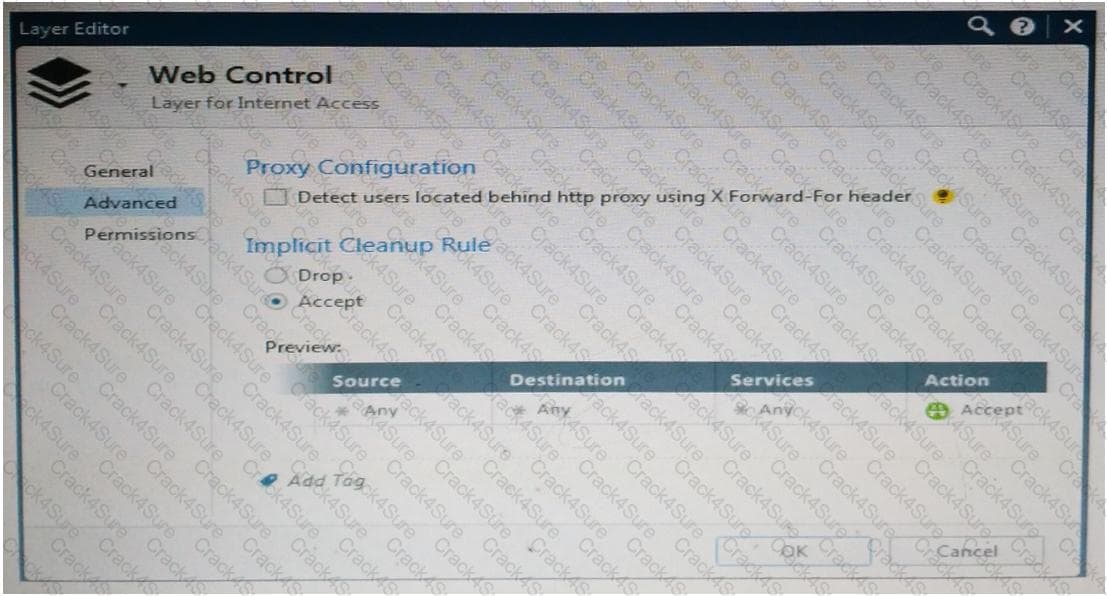
Consider the following policy and select the BEST answer.
Joey wants to configure NTP on R80 Security Management Server. He decided to do this via WebUI. What is the correct address to access the Web UI for Gaia platform via browser?
Which utility shows the security gateway general system information statistics like operating system information and resource usage, and individual software blade statistics of VPN, Identity Awareness and DLP?
Which utility allows you to configure the DHCP service on GAIA from the command line?
When doing a Stand-Alone Installation, you would install the Security Management Server with which other Check Point architecture component?
Fill in the blanks: The _________ collects logs and sends them to the _________ .
Which of the following ClusterXL modes uses a non-unicast MAC address for the cluster IP address?
In which deployment is the security management server and Security Gateway installed on the same appliance?
When a packet arrives at the gateway, the gateway checks it against the rules in the top Policy Layer, sequentially from top to bottom, and enforces the first rule that matches a packet. Which of the following statements about the order of rule enforcement is true?
Which of the following is an identity acquisition method that allows a Security Gateway to identify Active Directory users and computers?
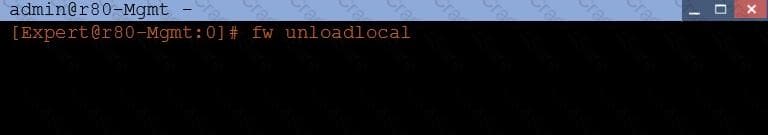
What will be the effect of running the following command on the Security Management Server?
Fill in the blank: The IPS policy for pre-R80 gateways is installed during the _______ .
Joey is using the computer with IP address 192.168.20.13. He wants to access web page “www.CheckPoint.com”, which is hosted on Web server with IP address 203.0.113.111. How many rules on Check Point Firewall are required for this connection?
The fw monitor utility is used to troubleshoot which of the following problems?
Which Check Point software blade provides protection from zero-day and undiscovered threats?