3 Months Free Update
3 Months Free Update
3 Months Free Update
To provide optimum security while enabling safe/necessary services, blocking known dangerous services, and making employees accountable for their online activity, what Internet Access policy would
Brian, the network administrator, have to choose?
During the recovery process, RTO and RPO should be the main parameters of your disaster
recovery plan. What does RPO refer to?
Which of the following interfaces uses hot plugging technique to replace computer components without the need to shut down the system?
James is a network administrator working at a student loan company in Minnesota. This company processes over 20,000 student loans a year from colleges all over the state. Most communication between the company
schools, and lenders is carried out through emails. Much of the email communication used at his company contains sensitive information such as social security numbers. For this reason, James wants to utilize email
encryption. Since a server-based PKI is not an option for him, he is looking for a low/no cost solution to encrypt emails. What should James use?
Which phase of vulnerability management deals with the actions taken for correcting the discovered vulnerability?
Rosa is working as a network defender at Linda Systems. Recently, the company migrated from Windows to MacOS. Rosa wants to view the security related logs of her system, where con she find these logs?
Your company is planning to use an uninterruptible power supply (UPS) to avoid damage from power fluctuations. As a network administrator, you need to suggest an appropriate UPS solution suitable for specific resources or conditions. Match the type of UPS with the use and advantage:
As a network administrator, you have implemented WPA2 encryption in your corporate wireless network. The WPA2's_________integrity check mechanism provides security against a replay attack
Michael decides to view the-----------------to track employee actions on the organization's network.
James, a network admin in a large US based IT firm, was asked to audit and implement security
controls over all network layers to achieve Defense-in-Depth. While working on this assignment, James
has implemented both blacklisting and whitelisting ACLs. Which layer of defense-in-depth architecture is
Jason working on currently?
Alex is administrating the firewall in the organization's network. What command will he use to check all the remote addresses and ports in numerical form?
John has been working a* a network administrator at an IT company. He wants to prevent misuse of accounts by unauthorized users. He wants to ensure that no accounts have empty passwords. Which of the following commands does John use to list all the accounts with an empty password?
Stephanie is currently setting up email security so all company data is secured when passed through email. Stephanie first sets up encryption to make sure that a specific user's email is protected. Next, she needs to
ensure that the incoming and the outgoing mail has not been modified or altered using digital signatures. What is Stephanie working on?
You are an IT security consultant working on a contract for a large manufacturing company to audit their entire network. After performing all the tests and building your report, you present a number of recommendations
to the company and what they should implement to become more secure. One recommendation is to install a network-based device that notifies IT employees whenever malicious or questionable traffic is found. From
your talks with the company, you know that they do not want a device that actually drops traffic completely, they only want notification. What type of device are you suggesting?
Ryan, a network security engineer, after a recent attack, is trying to get information about the kind
of attack his users were facing. He has decided to put into production one honeypot called Kojoney. He
is interested in emulating the network vulnerability, rather than the real vulnerability system, making
this probe safer and more flexible. Which type of honeypot is he trying to implement?
David, a network and system admin, encrypted all the files in a Windows system that supports NTFS file system using Encrypted File Systems (EFS). He then backed up the same files into another Windows
system that supports FAT file system. Later, he found that the backup files were not encrypted. What could be the reason for this?
Which BC/DR activity includes action taken toward resuming all services that are dependent on business-critical applications?
Identify the type of event that is recorded when an application driver loads successfully in Windows.
Which of the following can be used to disallow a system/user from accessing all applications except a specific folder on a system?
A network administrator is monitoring the network traffic with Wireshark. Which of the following filters will she use to view the packets moving without setting a flag to detect TCP Null Scan attempts?
Harry has sued the company claiming they made his personal information public on a social networking site in the United States. The company denies the allegations and consulted a/an ______for legal advice to defend
them against this allegation.
How can organizations obtain information about threats through human intelligence?
Which type of attack is used to hack an IoT device and direct large amounts of network traffic toward a web server, resulting in overloading the server with connections and preventing any new connections?
Delta IT solutions suffered a substantial data loss translating into a huge monetary loss for them. While investigation, the network admin analyzed all the packets and traffic transmitted across the
network and identified that some user, within the organization, had leaked the data. Which of the following devices could have helped the network admin reach this conclusion?
What should a network administrator perform to execute/test the untrusted or untested programs or code from untrusted or unverified third-parties without risking the host system or OS?
Steven is a Linux system administrator at an IT company. He wants to disable unnecessary services in the system, which can be exploited by the attackers. Which among the following is the correct syntax for
disabling a service?
Ross manages 30 employees and only 25 computers in the organization. The network the company uses is a peer-to-peer. Ross configures access control measures allowing the employees to set their own control
measures for their files and folders. Which access control did Ross implement?
John, who works as a team lead in Zen Technologies, found that his team members were accessing social networking sites, shopping sites and watching movies during office hours. He approached the
network admin to block such websites. What kind of network security device can be used to implement John’s decision?
As a network administrator, you have implemented WPA2 encryption in your corporate wireless network. The WPA2's _________integrity check mechanism provides security against a replay attack
------------is a group of broadband wireless communications standards for Metropolitan Area Networks (MANs)
Fargo, head of network defense at Globadyne Tech, has discovered an undesirable process in several Linux systems, which causes machines to hang every 1 hour. Fargo would like to eliminate it; what
command should he execute?
Blake is working on the company's updated disaster and business continuity plan. The last section of the plan covers computer and data incidence response. Blake is outlining the level of severity for each type of
incident in the plan. Unsuccessful scans and probes are at what severity level?
Riya bought some clothes and a watch from an online shopping site a few days back. Since then,
whenever she accesses any other application (games, browser, etc.) on her mobile, she is spammed with
advertisements for clothes and watches similar to the ones she bought. What can be the underlying
reason for Riya’s situation?
David is working in a mid-sized IT company. Management asks him to suggest a framework that can be used effectively to align the IT goals to the business goals of the company. David suggests the______framework,
as it provides a set of controls over IT and consolidates them to form a framework.
Which of the following data security technology can ensure information protection by obscuring specific areas of information?
Which type of wireless network attack is characterized by an attacker using a high gain amplifier from a nearby location to drown out the legitimate access point signal?
Will is working as a Network Administrator. Management wants to maintain a backup of all the company data as soon as it starts operations. They decided to use a RAID backup storage technology for their data backup
plan. To implement the RAID data backup storage, Will sets up a pair of RAID disks so that all the data written to one disk is copied automatically to the other disk as well. This maintains an additional copy of the data.
Which RAID level is used here?
You are monitoring your network traffic with the Wireshark utility and noticed that your network is experiencing a large amount of traffic from a certain region. You suspect a DoS incident on the network. What will be your
first reaction as a first responder?
Which of the following indicators refers to potential risk exposures that attackers can use to breach the security of an organization?
Which of the following VPN topologies establishes a persistent connection between an organization's main office and its branch offices using a third-party network or the Internet?
Which of the following is a data destruction technique that protects the sensitivity of information against a laboratory attack where an unauthorized individual uses signal processing recovery tools in a laboratory environment to recover the information?
According to standard loT security practice, loT Gateway should be connected to a -------------
Arman transferred some money to his friend’s account using a net banking service. After a few hours, his friend informed him that he hadn’t received the money yet. Arman logged on to the bank’s website to investigate and discovered that the amount had been transferred to an unknown account instead. The bank, upon receiving Arman’s complaint, discovered that someone had established a station between Arman’s and the bank server’s communication system. The station intercepted the communication and inserted another account number replacing his friend’s account number. What is
such an attack called?
Bryson is the IT manager and sole IT employee working for a federal agency in California. The agency was just given a grant and was able to hire on 30 more employees for a new extended project. Because of this,
Bryson has hired on two more IT employees to train up and work. Both of his new hires are straight out of college and do not have any practical IT experience. Bryson has spent the last two weeks teaching the new
employees the basics of computers, networking, troubleshooting techniques etc. To see how these two new hires are doing, he asks them at what layer of the OSI model do Network Interface Cards (NIC) work on. What
should the new employees answer?
John wants to implement a firewall service that works at the session layer of the OSI model. The firewall must also have the ability to hide the private network information. Which type of firewall service is John thinking of
implementing?
An IT company has just been hit with a severe external security breach. To enhance the company’s security posture, the network admin has decided to first block all the services and then individually
enable only the necessary services. What is such an Internet access policy called?
John has planned to update all Linux workstations in his network. The organization is using various Linux distributions including Red hat, Fedora and Debian. Which of following commands will he use to
update each respective Linux distribution?
XX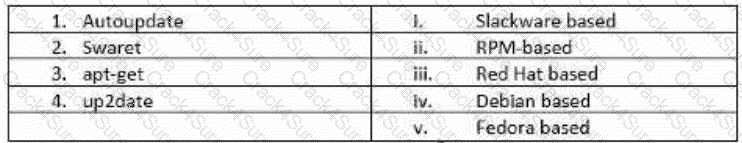
Which firewall can a network administrator use for better bandwidth management, deep packet inspection, and Hateful inspection?
A stateful multilayer inspection firewall combines the aspects of Application level gateway, Circuit level gateway and Packet filtering firewall. On which layers of the OSI model, does the Stateful
multilayer inspection firewall works?
Jeanne is working as a network administrator in an IT company. She wants to control/limit container
access to CPU, memory, swap, block IO (rates), network. Which Linux kernel feature allows Jeanne to
manage, restrict, and audit groups of the process?
Which of the following statements holds true in terms of virtual machines?
Identify the network topology where each computer acts as a repeater and the data passes from one computer to the other in a single direction until it reaches the destination.
Justine has been tasked by her supervisor to ensure that the company's physical security is on the same level as their logical security measures. She installs video cameras at all entrances and exits and installs badge
access points for all doors. The last item she wants to install is a method to prevent unauthorized people piggybacking employees. What should she install to prevent piggybacking?
John has implemented________in the network to restrict the limit of public IP addresses in his organization and to enhance the firewall filtering technique.
On which of the following OSI layers does the Pretty Good Privacy (PGP) work?
What is the IT security team responsible for effectively managing the security of the organization’s IT infrastructure, called?
Which among the following options represents professional hackers with an aim of attacking systems for profit?
Which biometric technique authenticates people by analyzing the layer of blood vessels at the back of their eyes?
Paul is a network security technician working on a contract for a laptop manufacturing company in Chicago. He has focused primarily on securing network devices, firewalls, and traffic traversing in and out of the
network. He just finished setting up a server a gateway between the internal private network and the outside public network. This server will act as a proxy, limited amount of services, and will filter packets. What is this
type of server called?
In ______ method, event logs are arranged in the form of a circular buffer.
Which of the following commands can be used to disable unwanted services on Debian, Ubuntu and other Debian-based Linux distributions?
A CCTV camera, which can be accessed on the smartphone from a remote location, is an example of _____
Stephanie is currently setting up email security so all company data is secured when passed through email. Stephanie first sets up encryption to make sure that a specific user's email is protected. Next, she needs to
ensure that the incoming and the outgoing mail has not been modified or altered using digital signatures. What is Stephanie working on?
What can be the possible number of IP addresses that can be assigned to the hosts present in a subnet having 255.255.255.224 subnet mask?
Which of the following standards does a cloud service provider has to comply with, to protect the privacy of its customer’s personal information?
Which of the following defines the extent to which an interruption affects normal business operations and the amount of revenue lost due to that interruption?
Chris is a senior network administrator. Chris wants to measure the Key Risk Indicator (KRI) to assess the organization. Why is Chris calculating the KRI for his organization? It helps Chris to:
A local bank wants to protect their cardholder data. Which standard should the bark comply with in order to ensure security of this data?
Malone is finishing up his incident handling plan for IT before giving it to his boss for review. He is outlining the incident response methodology and the steps that are involved. What is the last step he should list?
You are responsible for network functions and logical security throughout the corporation. Your company has over 250 servers running Windows Server 2012, 5000workstations running Windows 10, and 200 mobile
users working from laptops on Windows 8. Last week 10 of your company's laptops were stolen from a salesman, while at a conference in Barcelona. These laptops contained proprietary company information. While
doing a damage assessment, a news story leaks about a blog post containing information about the stolen laptops and the sensitive information. What built-in Windows feature could you have implemented to protect the
sensitive information on these laptops?
Larry is responsible for the company's network consisting of 300 workstations and 25 servers. After using a hosted email service for a year, the company wants to control the email internally. Larry likes this idea because
it will give him more control over the email. Larry wants to purchase a server for email but does not want the server to be on the internal network due to the potential to cause security risks. He decides to place the server
outside of the company's internal firewall. There is another firewall connected directly to the Internet that will protect traffic from accessing the email server. The server will be placed between the two firewalls. What
logical area is Larry putting the new email server into?
Liza was told by her network administrator that they will be implementing IPsec VPN tunnels to connect the branch locations to the main office. What layer of the OSI model do IPsec tunnels function on?
An employee of a medical service company clicked a malicious link in an email sent by an attacker. Suddenly, employees of the company are not able to access billing information or client record as it is
encrypted. The attacker asked the company to pay money for gaining access to their data. Which type of malware attack is described above?
Kyle is an IT technician managing 25 workstations and 4 servers. The servers run applications and mostly store confidential data. Kyle must backup the server's data daily to ensure nothing is lost. The power in the
company's office is not always reliable, Kyle needs to make sure the servers do not go down or are without power for too long. Kyle decides to purchase an Uninterruptible Power Supply (UPS) that has a pair of inverters
and converters to charge the battery and provides power when needed. What type of UPS has Kyle purchased?
Identify the password cracking attempt involving precomputed hash values stored as plaintext and using these to crack the password.
Which mobile-use approach allows an organization’s employees to use devices that they are comfortable with and best fits their preferences and work purposes?
Malone is finishing up his incident handling plan for IT before giving it to his boss for review. He is outlining the incident response methodology and the steps that are involved. What is the last step he should list?
Mark is monitoring the network traffic on his organization's network. He wants to detect a TCP and UDP ping sweep on his network. Which type of filter will be used to detect this on the network?
Which of the following information security standards defines security policies, technologies and ongoing processes for organizations that handle cardholder information for debit, credit, prepaid, epurse, ATM, and POS cards?
Albert works as a Windows system administrator at an MNC. He uses PowerShell logging to identify any suspicious scripting activity across the network. He wants to record pipeline execution details as
PowerShell executes, including variable initialization and command invocations. Which PowerShell logging component records pipeline execution details as PowerShell executes?
Katie has implemented the RAID level that split data into blocks and evenly write the data to multiple hard drives but does not provide data redundancy. This type of RAID level requires a minimum of________in order to
setup.
Which of the following RAID storage techniques divides the data into multiple blocks, which are further written across the RAID system?
Which of the following systems includes an independent NAS Head and multiple storage arrays?
John, a network administrator, is configuring Amazon EC2 cloud service for his organization. Identify the type of cloud service modules his organization adopted.
Identify the firewall technology that monitors the TCP handshake between the packets to determine whether a requested session is legitimate.