3 Months Free Update
3 Months Free Update
3 Months Free Update
Which of the following CIS Controls is used to manage the security lifecycle by validating that the documented controls are in place?
Executive management approved the storage of sensitive data on smartphones and tablets as long as they were encrypted. Later a vulnerability was announced at an information security conference that allowed attackers to bypass the device’s authentication process, making the data accessible. The smartphone manufacturer said it would take six months for the vulnerability to be fixed and distributed through the cellular carriers. Four months after the vulnerability was announced, an employee lost his tablet and the sensitive information became public.
What was the failure that led to the information being lost?
What is a recommended defense for the CIS Control for Application Software Security?
Which of the options below will do the most to reduce an organization’s attack surface on the internet?
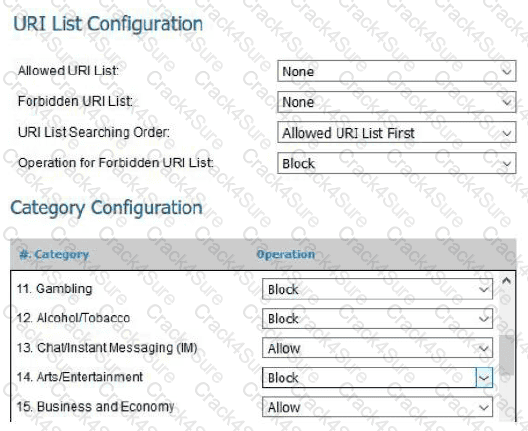
Below is a screenshot from a deployed next-generation firewall. These configuration settings would be a defensive measure for which CIS Control?