We at Crack4sure are committed to giving students who are preparing for the Paloalto Networks PCCSE Exam the most current and reliable questions . To help people study, we've made some of our Prisma Certified Cloud Security Engineer exam materials available for free to everyone. You can take the Free PCCSE Practice Test as many times as you want. The answers to the practice questions are given, and each answer is explained.
Which alerts are fixed by enablement of automated remediation?
In WAAS Access control file upload controls, which three file types are supported out of the box? (Choose three.)
Which options show the steps required to upgrade Console when using projects?
Which three options for hardening a customer environment against misconfiguration are included in Prisma Cloud Compute compliance enforcement for hosts? (Choose three.)
A business unit has acquired a company that has a very large AWS account footprint. The plan is to immediately start onboarding the new company’s AWS accounts into Prisma Cloud Enterprise tenant immediately. The current company is currently not using AWS Organizations and will require each account to be onboarded individually.
The business unit has decided to cover the scope of this action and determined that a script should be written to onboard each of these accounts with general settings to gain immediate posture visibility across the accounts.
Which API endpoint will specifically add these accounts into the Prisma Cloud Enterprise tenant?
A customer has a requirement to scan serverless functions for vulnerabilities.
Which three settings are required to configure serverless scanning? (Choose three.)
When an alert notification from the alarm center is deleted, how many hours will a similar alarm be suppressed by default?
Which three platforms support the twistcli tool? (Choose three.)
What is the purpose of Incident Explorer in Prisma Cloud Compute under the "Monitor" section?
What are two built-in RBAC permission groups for Prisma Cloud? (Choose two.)
On which cloud service providers can you receive new API release information for Prisma Cloud?
The Unusual protocol activity (Internal) network anomaly is generating too many alerts. An administrator has been asked to tune it to the option that will generate the least number of events without disabling it entirely.
Which strategy should the administrator use to achieve this goal?
When would a policy apply if the policy is set under Defend > Vulnerability > Images > Deployed?
Which two elements are included in the audit trail section of the asset detail view? (Choose two).
Which two statements explain differences between build and run config policies? (Choose two.)
Given the following information, which twistcli command should be run if an administrator were to exec into a running container and scan it from within using an access token for authentication?
• Console is located at https://prisma-console.mydomain.local
• Token is: TOKEN_VALUE
• Report ID is: REPORTJD
• Container image running is: myimage:latest
How are the following categorized?
Backdoor account access Hijacked processes Lateral movement
Port scanning
Which RQL query will help create a custom identity and access management (1AM) policy to alert on Lambda functions that have permission to terminate EC2 instances?
Given the following RQL:
event from cloud.audit_logs where operation IN (‘CreateCryptoKey’, ‘DestroyCryptoKeyVersion’, ‘v1.compute.disks.createSnapshot’)
Which audit event snippet is identified?
A)

B)
C)

D)

Which component of a Kubernetes setup can approve, modify, or reject administrative requests?
Which ROL query is used to detect certain high-risk activities executed by a root user in AWS?
A customer has multiple violations in the environment including:
User namespace is enabled
An LDAP server is enabled
SSH root is enabled
Which section of Console should the administrator use to review these findings?
What is the function of the external ID when onboarding a new Amazon Web Services (AWS) account in Prisma Cloud?
Which two options may be used to upgrade the Defenders with a Console v20.04 and Kubernetes deployment? (Choose two.)
An administrator has added a Cloud account on Prisma Cloud and then deleted it.
What will happen if the deleted account is added back on Prisma Cloud within a 24-hour period?
Which action must be taken to enable a user to interact programmatically with the Prisma Cloud APIs and for a nonhuman entity to be enabled for the access keys?
A customer has serverless functions that are deployed in multiple clouds.
Which serverless cloud provider is covered be “overly permissive service access” compliance check?
In Prisma Cloud for Azure Net Effective Permissions Calculation, the following Azure permission levels are supported by which three permissions? (Choose three).
The security auditors need to ensure that given compliance checks are being run on the host. Which option is a valid host compliance policy?
Which two CI/CD plugins are supported by Prisma Cloud as part of its DevOps Security? (Choose two.).
What are the subtypes of configuration policies in Prisma Cloud?
An administrator has been tasked with creating a custom service that will download any existing compliance report from a Prisma Cloud Enterprise tenant.
In which order will the APIs be executed for this service?
(Drag the steps into the correct order of occurrence, from the first step to the last.)

A customer's Security Operations Center (SOC) team wants to receive alerts from Prisma Cloud via email once a day about all policies that have a violation, rather than receiving an alert every time a new violation occurs.
Which alert rule configuration meets this requirement?
Which role does Prisma Cloud play when configuring SSO?
Which of the below actions would indicate – “The timestamp on the compliance dashboard?
Which three types of buckets exposure are available in the Data Security module? (Choose three.)
Which policy type provides information about connections from suspicious IPs in a customer database?
Which two bot types are part of Web Application and API Security (WAAS) bot protection? (Choose two.)
Prisma Cloud cannot integrate which of the following secrets managers?
An administrator has deployed Console into a Kubernetes cluster running in AWS. The administrator also has configured a load balancer in TCP passthrough mode to listen on the same ports as the default Prisma Compute Console configuration.
In the build pipeline, the administrator wants twistcli to talk to Console over HTTPS. Which port will twistcli need to use to access the Prisma Compute APIs?
Which Defender type performs registry scanning?
You are an existing customer of Prisma Cloud Enterprise. You want to onboard a public cloud account and immediately see all of the alerts associated with this account based off ALL of your tenant’s existing enabled policies. There is no requirement to send alerts from this account to a downstream application at this time.
Which option shows the steps required during the alert rule creation process to achieve this objective?
Which of the following is displayed in the asset inventory?
Given a default deployment of Console, a customer needs to identify the alerted compliance checks that are set by default.
Where should the customer navigate in Console?
Which RQL will trigger the following audit event activity?
Which three actions are required in order to use the automated method within Azure Cloud to streamline the process of using remediation in the identity and access management (IAM) module? (Choose three.)
Which intensity setting for anomaly alerts is used for the measurement of 100 events over 30 days?
Which three OWASP protections are part of Prisma Cloud Web-Application and API Security (WAAS) rule? (Choose three.)
Which three serverless runtimes are supported by Prisma Cloud for vulnerability and compliance scans? (Choose three.)
Which set of steps is the correct process for obtaining Console images for Prisma Cloud Compute Edition?
The administrator wants to review the Console audit logs from within the Console.
Which page in the Console should the administrator use to review this data, if it can be reviewed at all?
Match the correct scanning mode for each given operation.
(Select your answer from the pull-down list. Answers may be used more than once or not at all.)

Which two statements are true about the differences between build and run config policies? (Choose two.)
A customer has a requirement to automatically protect all Lambda functions with runtime protection. What is the process to automatically protect all the Lambda functions?
How is the scope of each rule determined in the Prisma Cloud Compute host runtime policy?
How does assigning an account group to an administrative user on Prisma Cloud help restrict access to resources?
Which two roles have access to view the Prisma Cloud policies? (Choose two.)
A customer wants to monitor its Amazon Web Services (AWS) accounts via Prisma Cloud, but only needs the resource configuration to be monitored at present.
Which two pieces of information are needed to onboard this account? (Choose two.)
Which two attributes are required for a custom config RQL? (Choose two.)
Which three Orchestrator types are supported when deploying Defender? (Choose three.)
Review this admission control policy:
match[{"msg": msg}] { input.request.operation == "CREATE" input.request.kind.kind == "Pod" input.request.resource.resource == "pods"
input.request.object.spec.containers[_].securityContext.privileged msg := "Privileged"
}
Which response to this policy will be achieved when the effect is set to “block”?
Which type of compliance check is available for rules under Defend > Compliance > Containers and Images > CI?
In which two ways can Prisma Cloud images be retrieved in Prisma Cloud Compute Self-Hosted Edition? (Choose two.)
Which statement is true regarding CloudFormation templates?
How often do Defenders share logs with Console?
A customer has a requirement to terminate any Container from image topSecret:latest when a process named ransomWare is executed.
How should the administrator configure Prisma Cloud Compute to satisfy this requirement?
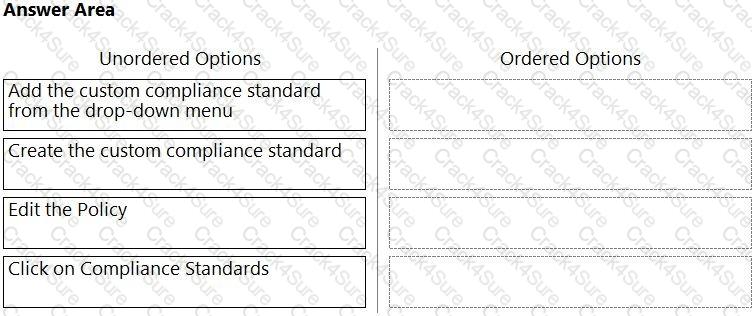
Which order of steps map a policy to a custom compliance standard?
(Drag the steps into the correct order of occurrence, from the first step to the last.)
A customer has a requirement to scan serverless functions for vulnerabilities.
What is the correct option to configure scanning?
Which two offerings will scan container images in Jenkins pipelines? (Choose two.)
Which of the following is not a supported external integration for receiving Prisma Cloud Code Security notifications?
Which of the following are correct statements regarding the use of access keys? (Choose two.)
Under which tactic is “Exploit Public-Facing Application” categorized in the ATT&CK framework?
What happens when a role is deleted in Prisma Cloud?