We at Crack4sure are committed to giving students who are preparing for the CompTIA 220-1202 Exam the most current and reliable questions . To help people study, we've made some of our CompTIA A+ Core 2 (2026 Exam Update) exam materials available for free to everyone. You can take the Free 220-1202 Practice Test as many times as you want. The answers to the practice questions are given, and each answer is explained.
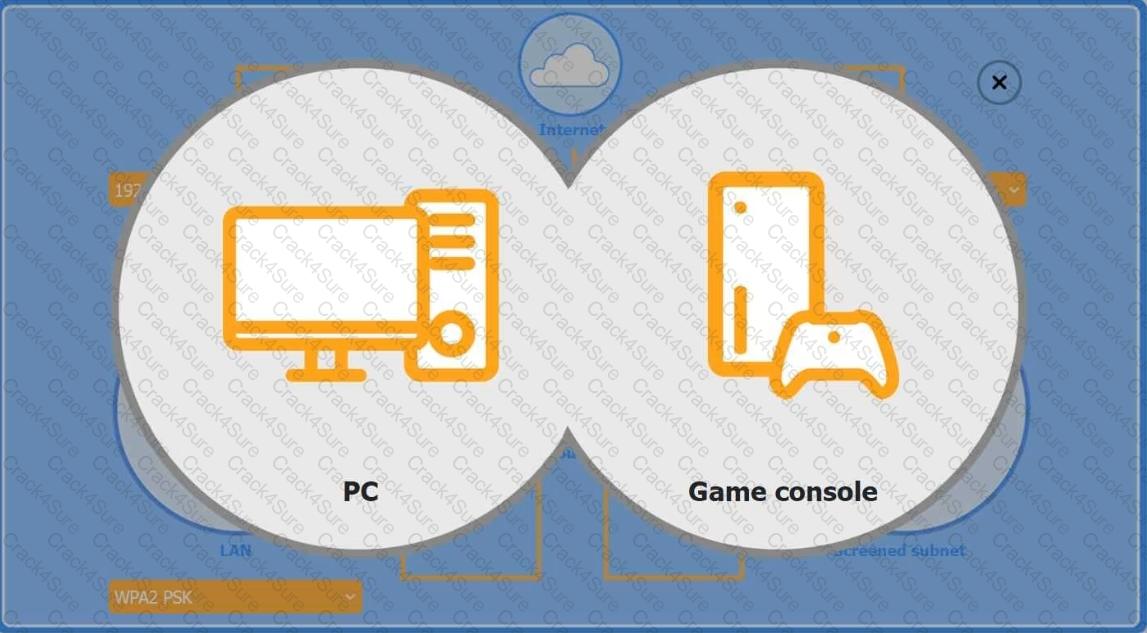
You are configuring a home network for a customer. The customer has requested the ability to access a Windows PC remotely, and needs all chat and optional functions to work in their game console.
INSTRUCTIONS
Use the drop-down menus to complete the network configuration for the customer. Each option may only be used once, and not all options will be used.
Then, click the + sign to place each device in its appropriate location.
If at any time you would like to bring back the initial state of the simulation, please click the Reset All button.
Wireless AP LAN
Firewall Screened Subnet
Technicians are failing to document user contact information, device asset tags, and a clear description of each issue in the ticketing system. Which of the following should a help desk management team implement for technicians to use on every call?
A user calls the help desk to report an issue with their smartphone. After the user returns from a business trip, the user is no longer able to access email or visit websites without a Wi-Fi connection on the smartphone. Which of the following would the user do to most likely resolve the issue?
A technician needs to map a shared drive from a command-line interface. Which of the following commands should the technician use?
A customer’s laptop will not turn on. The customer is distraught and panicking because the laptop contains family pictures that can never be replaced. Which of the following communication techniques is most important for the technician to demonstrate in this situation?
A technician is troubleshooting an issue in which a service runs momentarily and stops at certain points in the process. The technician needs to determine the root cause of this issue. Which of the following tools should the technician use?
An administrator is investigating a zero-day vulnerability. If left unpatched, it could severely impact business. The patch requires downtime. What should the administrator do?
A high percentage of users at an office store documents on their local computers. The office needs to migrate to the next version of Windows. Which of the following methods should a technician use?
A security administrator teaches all of an organization ' s staff members to use BitLocker To Go. Which of the following best describes the reason for this training?
A user has been adding data to the same spreadsheet for several years. After adding a significant amount of data, they are now unable to open the file. Which of the following should a technician do to resolve the issue?
A secretary receives an email from the CEO requesting immediate vendor payment. Later, the CEO says they never sent it. Which social engineering tactic is this?
An end user is unable to print to a network printer but can access everything else on the network. Other users have no issues printing. A technician opens the print queue on the user’s computer and sees the job has failed. What is the next step to troubleshoot the issue?
A technician is selecting a remote access method so users can securely access Linux and Windows servers when working from home. Which of the following should the technician choose to best meet this requirement?
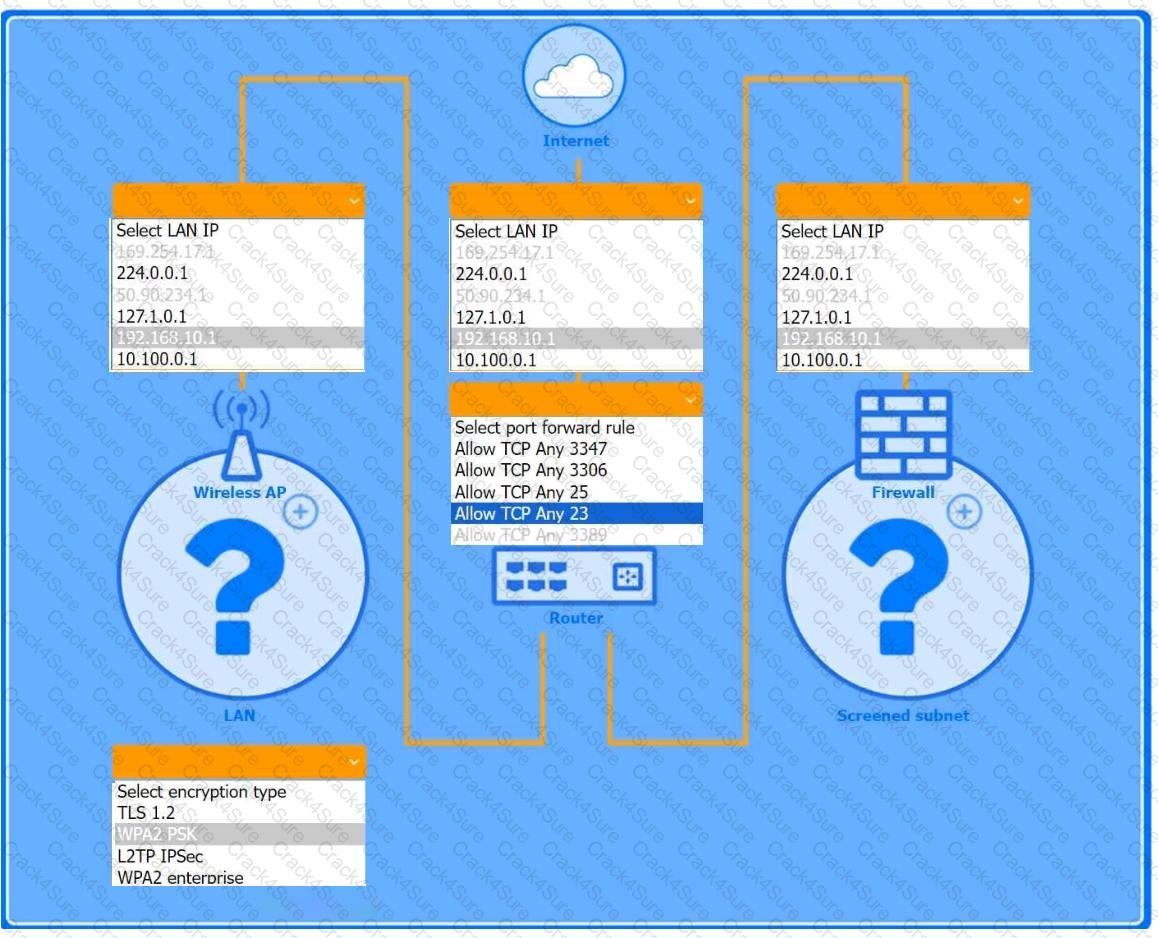
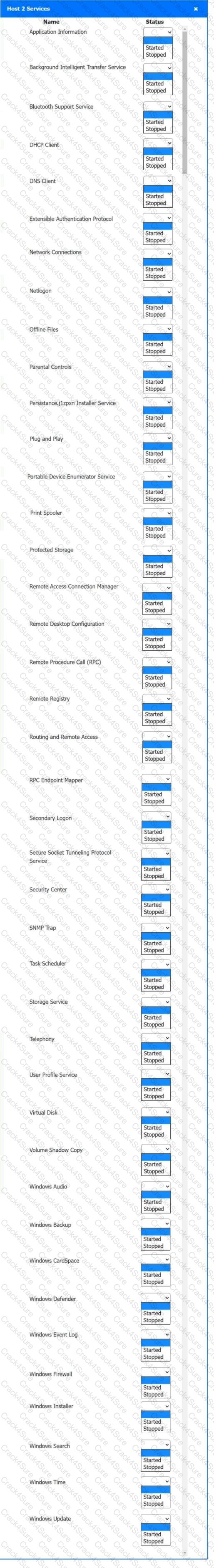
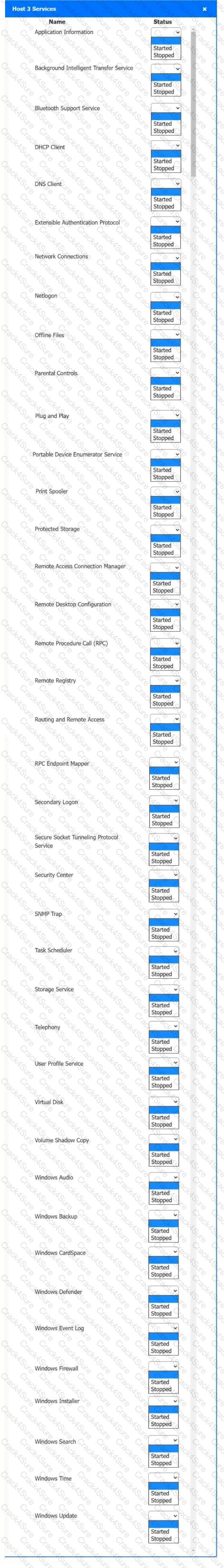
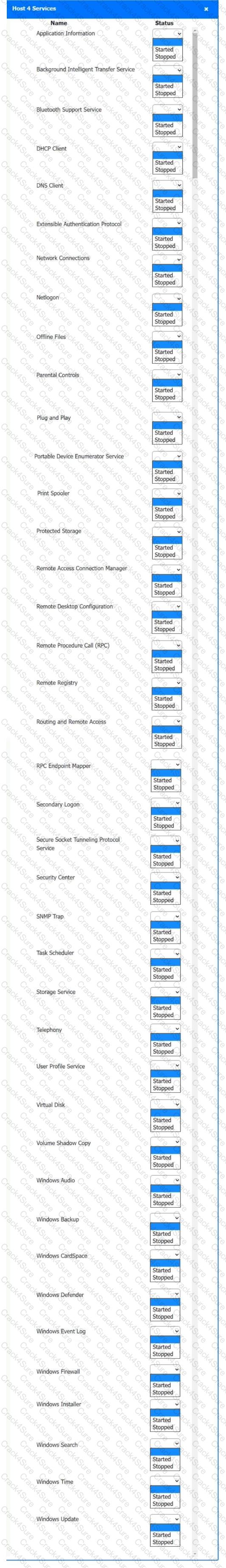
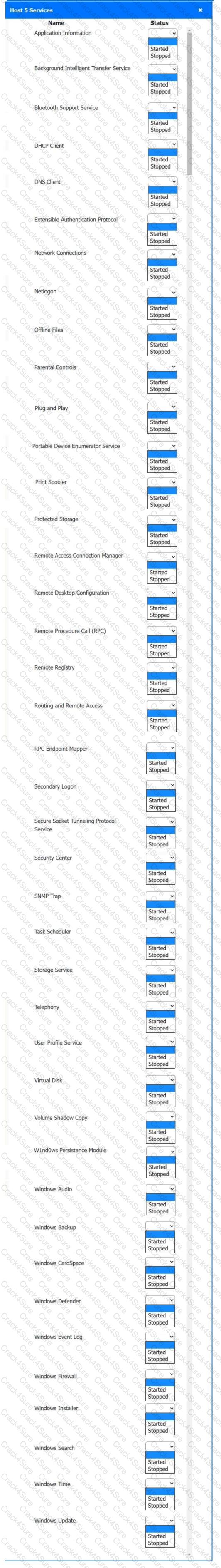
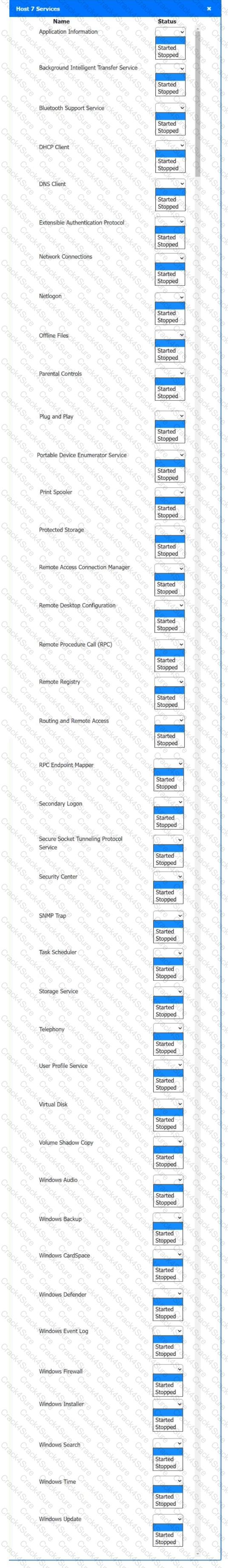
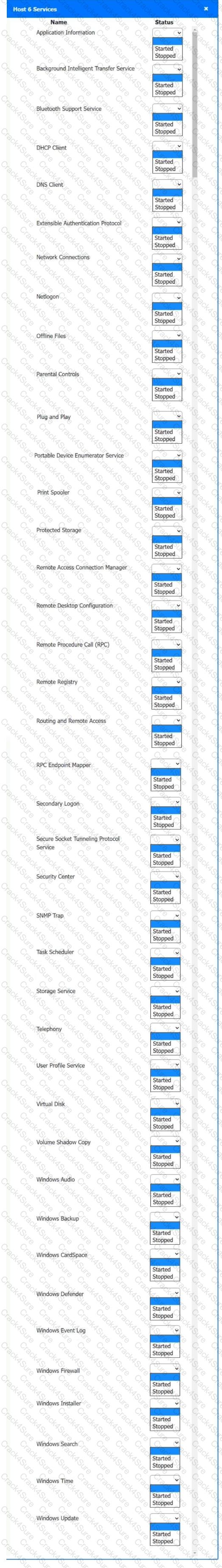
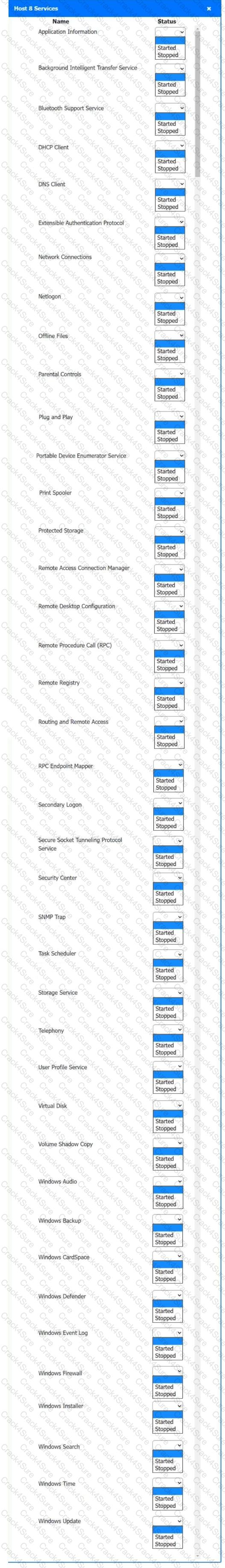
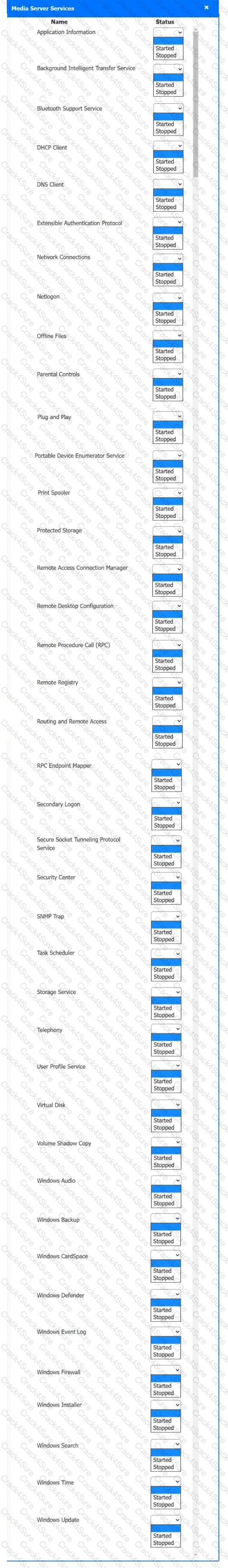
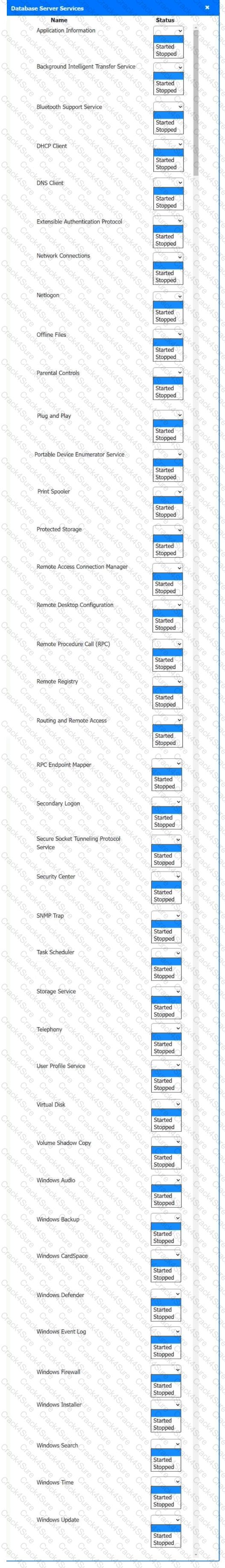
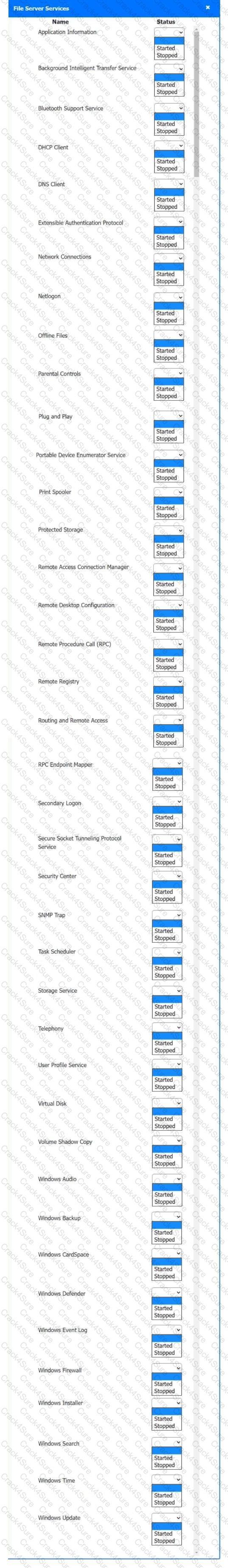
Multiple users are reporting audio issues as well as performance issues after downloading unauthorized software. You have been dispatched to identify and resolve any issues on the network using best practice procedures.
INSTRUCTIONS
Quarantine and configure the appropriate device(s) so that the users’ audio issues are resolved using best practice procedures.
Multiple devices may be selected for quarantine.
Click on a host or server to configure services.
If at any time you would like to bring back the initial state of the simulation, please click the Reset All button.
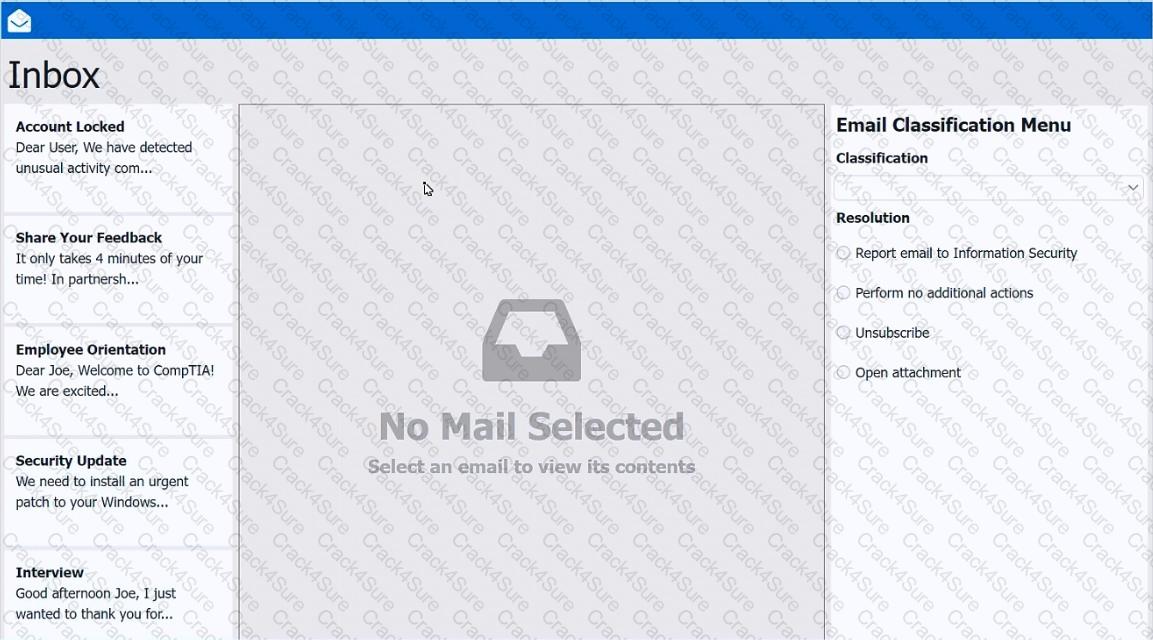
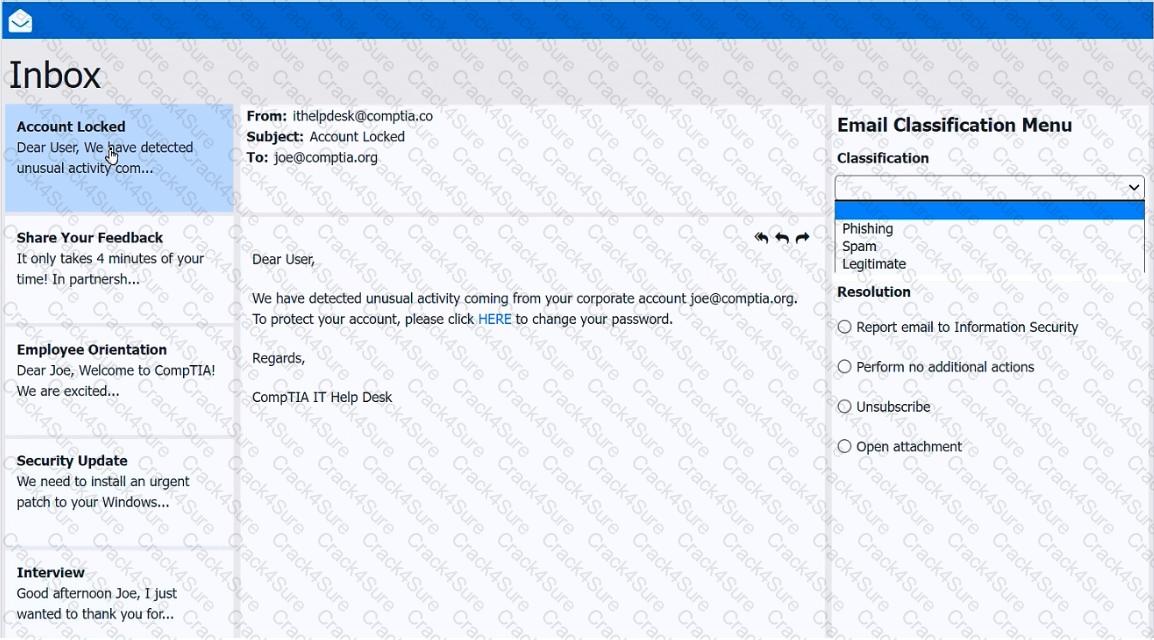
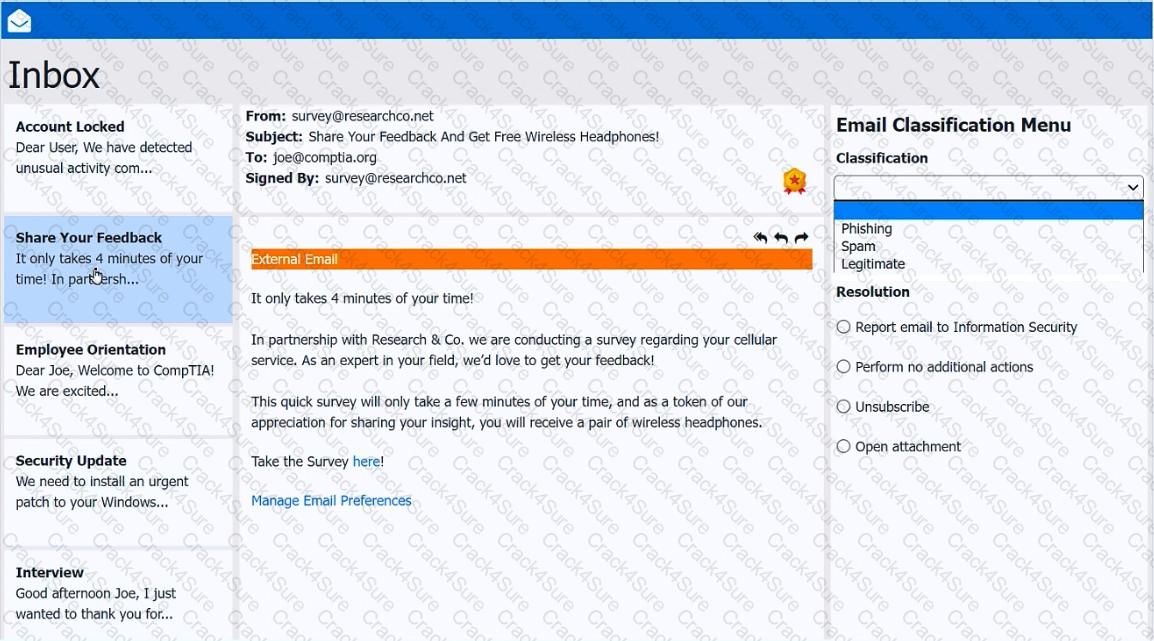
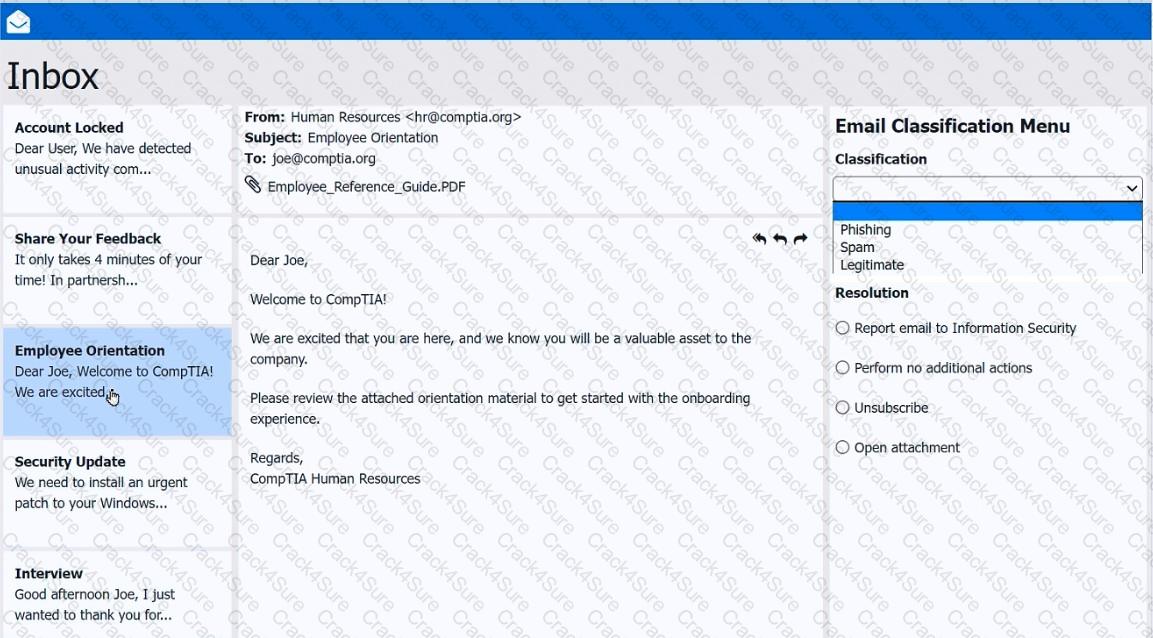
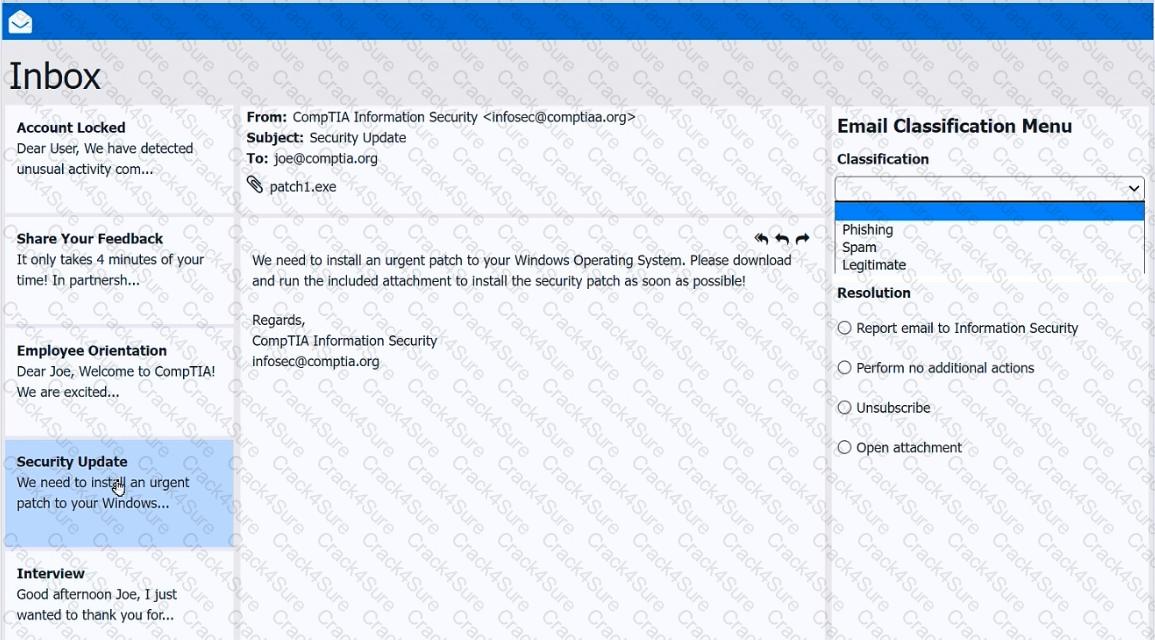
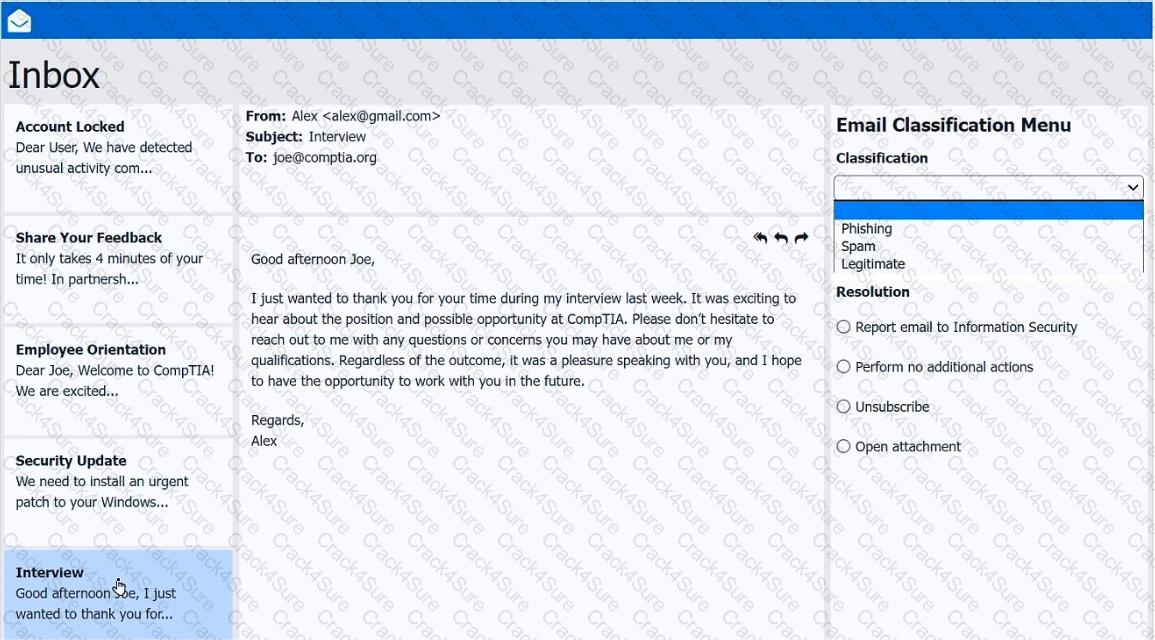
As a corporate technician, you are asked to evaluate several suspect email messages on a client ' s computer. Corporate policy requires the following:
> All phishing attempts must be reported.
> Future spam emails to users must be prevented.
INSTRUCTIONS
Review each email and perform the following within the email:
> Classify the emails
> Identify suspicious items, if applicable, in each email
> Select the appropriate resolution
If at any time you would like to bring back the initial state of the simulation, please click the Reset All button.
Which of the following must be followed during incident response to ensure the collected evidence is properly handled and accounted for?
Every time a user loads a specific spreadsheet, their computer is temporarily unresponsive. The user also notices that the title bar indicates the application is not responding. Which of the following would a technician most likely inspect?
A customer laptop has been shutting down unexpectedly. The customer explains that a blue screen appears just before the laptop turns off, but the screen disappears too quickly to see anything. Which of the following tools should a technician use to find details about the error?
A user is installing a third-party application on the latest macOS. The user receives a security warning that states the application is unsigned and cannot be installed. Which of the following settings should the user adjust to allow the installation?
Which of the following operating systems is used to join a domain?
A user ' s machine is infected with malware that the user ' s existing security software did not detect. Which of the following best explains the reason the infection was undetected?
A user reports that the time on their computer does not match the time on their VoIP phone. What should a technician do?
A technician is working on multiple remote machines using a command line. Which of the following commands should the technician use to verify which SMB shares are currently mapped?
A network technician notices that most of the company ' s network switches are now end-of-life and need to be upgraded. What should the technician do first?
Which of the following is typically associated with a Linux filesystem?
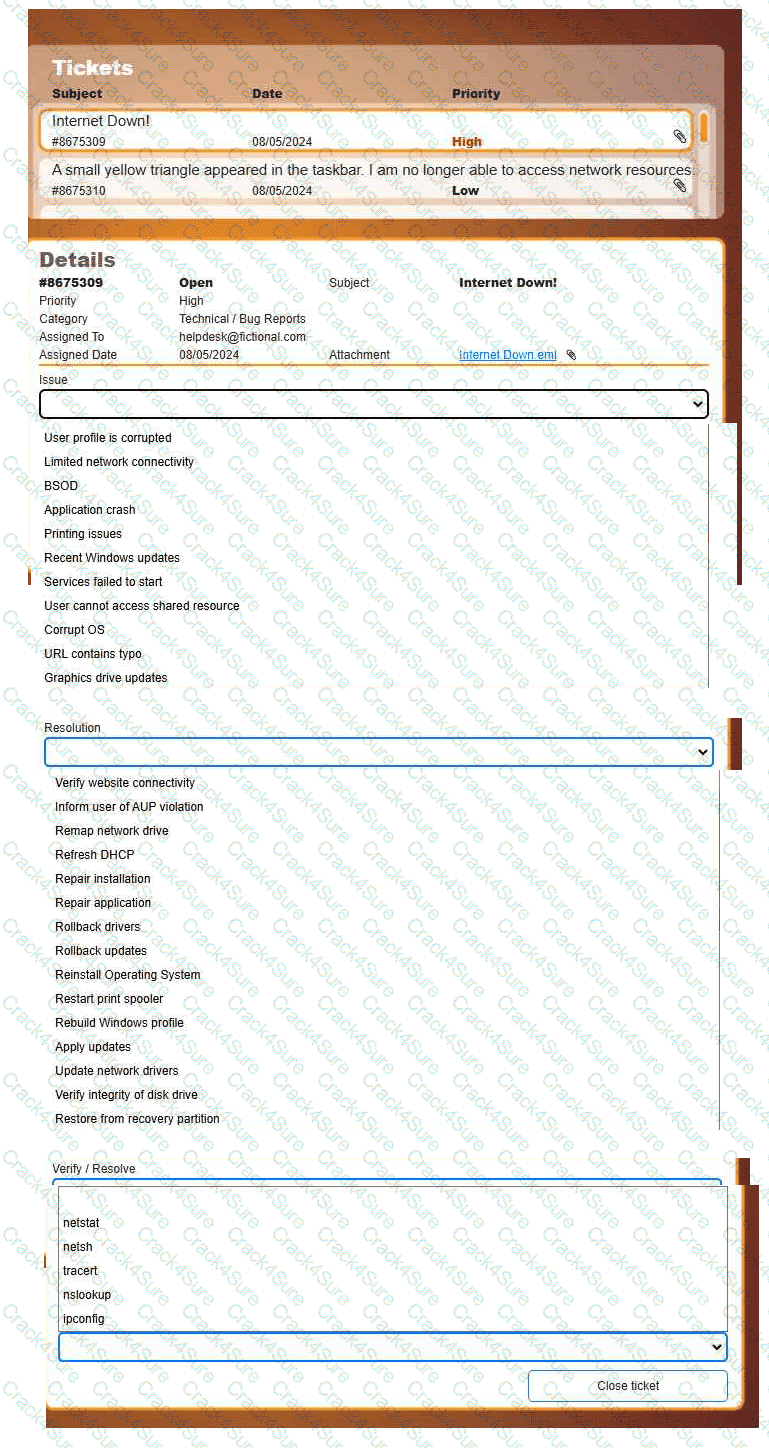
Welcome to your first day as a Fictional Company, LLC helpdesk employee. Please work the tickets in your helpdesk ticket queue.
INSTRUCTIONS
Click on individual tickets to see the ticket details, and view applicable attachments to
determine the problem.
Select the appropriate issue from the ' Issue ' drop-down menu. Then, select the most
efficient resolution from the ' Resolution ' drop-down menu. Finally, select the proper
command or verification to remediate or confirm your fix of the issue from the
' Verify/Resolve ' drop-down menu.
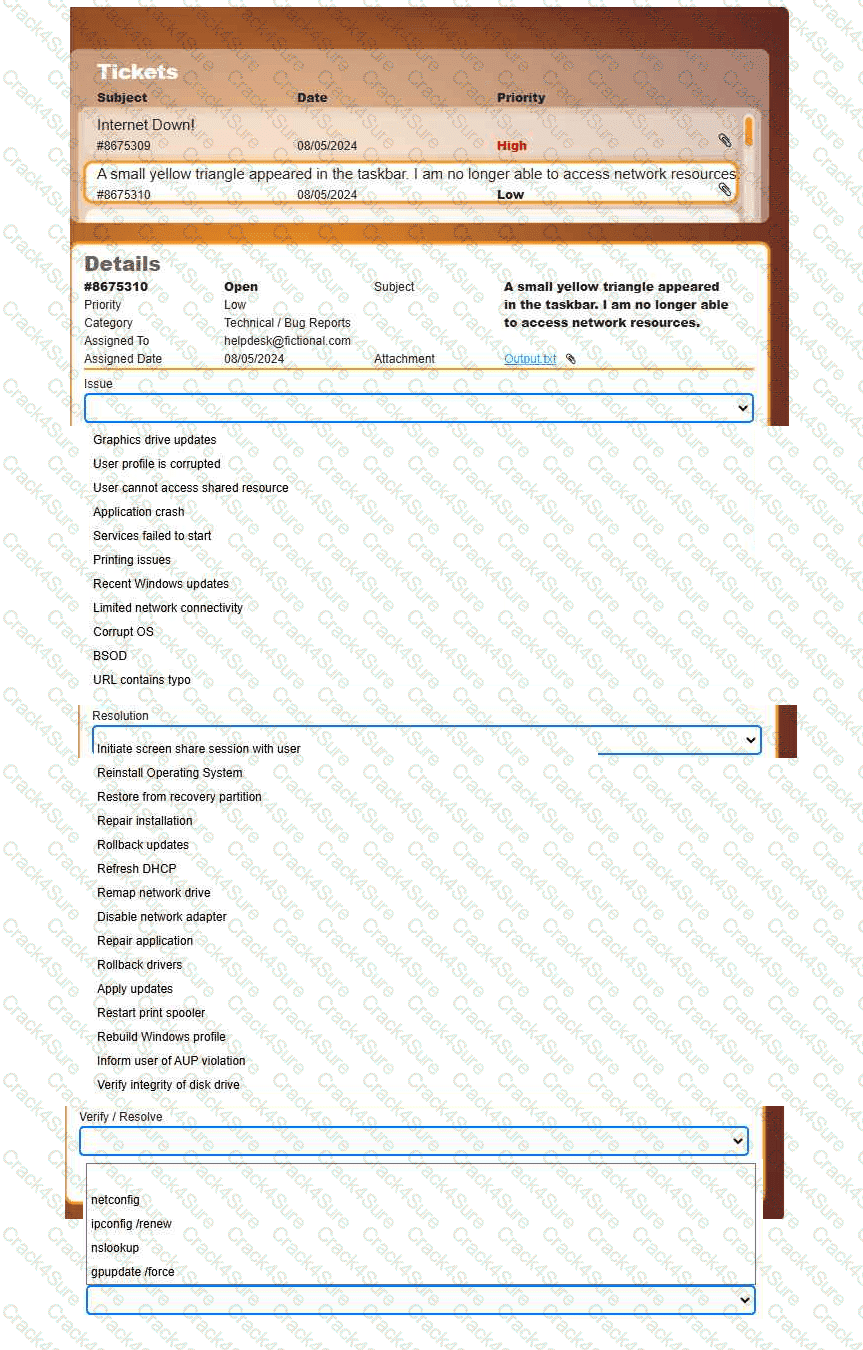
Welcome to your first day as a Fictional Company, LLC helpdesk employee. Please work the tickets in your helpdesk ticket queue.
INSTRUCTIONS
Click on individual tickets to see the ticket details, and view applicable attachments to
determine the problem.
Select the appropriate issue from the ' Issue ' drop-down menu. Then, select the most
efficient resolution from the ' Resolution ' drop-down menu. Finally, select the proper
command or verification to remediate or confirm your fix of the issue from the
' Verify/Resolve ' drop-down menu.
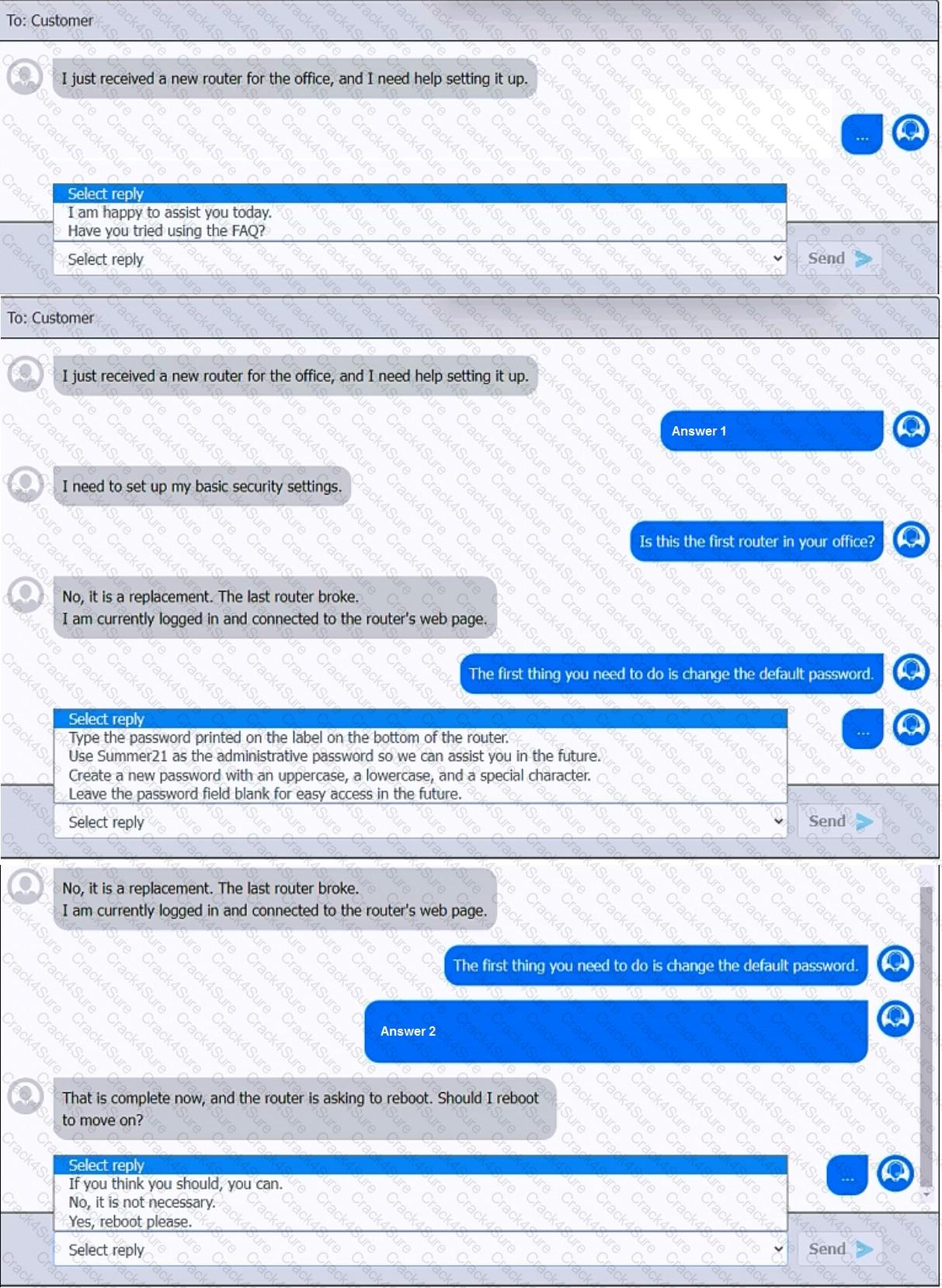
You have been contacted through the help desk chat application. A user is setting up a replacement SOHO router. Assist the user with setting up the router.
INSTRUCTIONS
Select the most appropriate statement for each response. Click the send button after each response to continue the chat.
If at any time you would like to bring back the initial state of the simulation, please click the Reset All button.
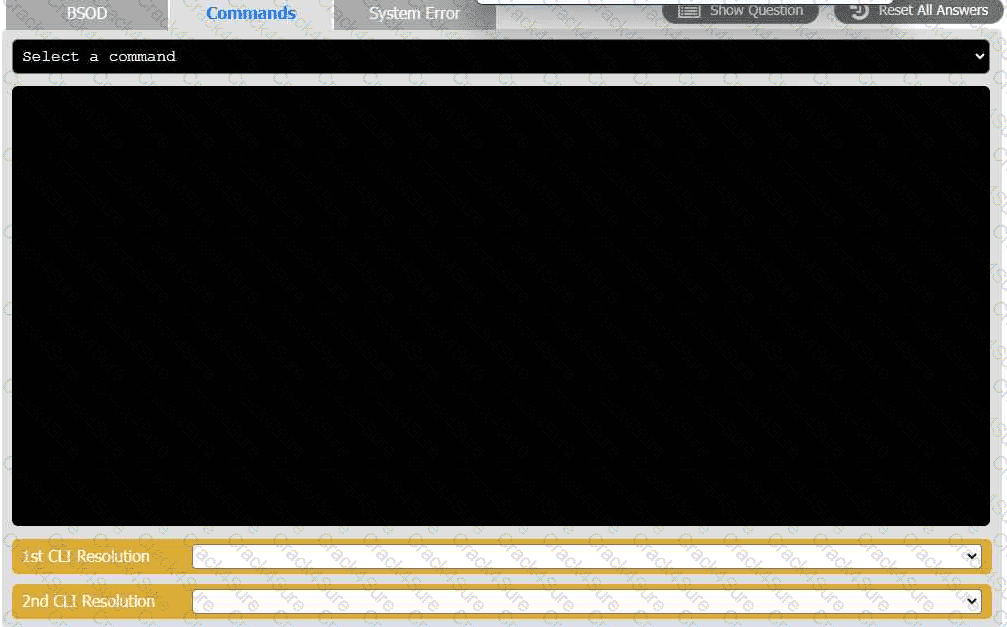
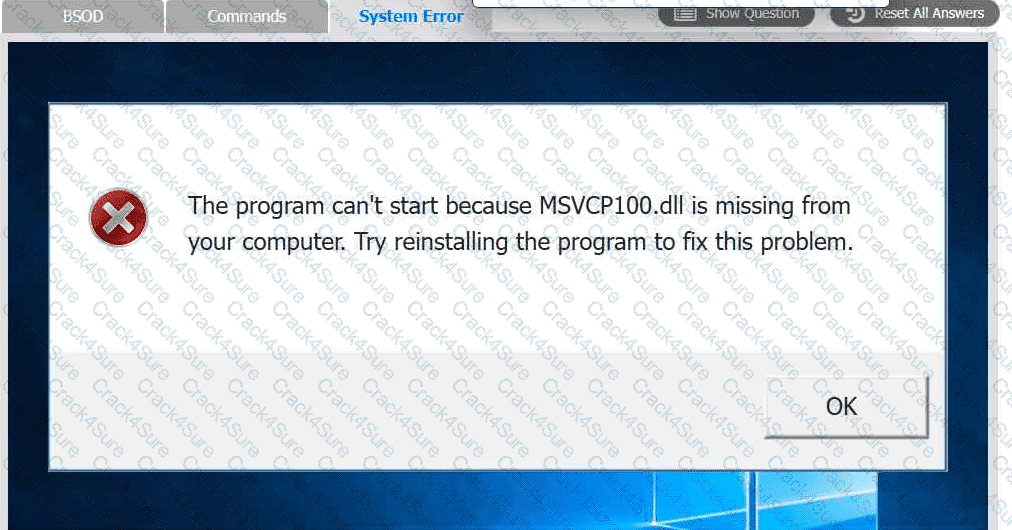
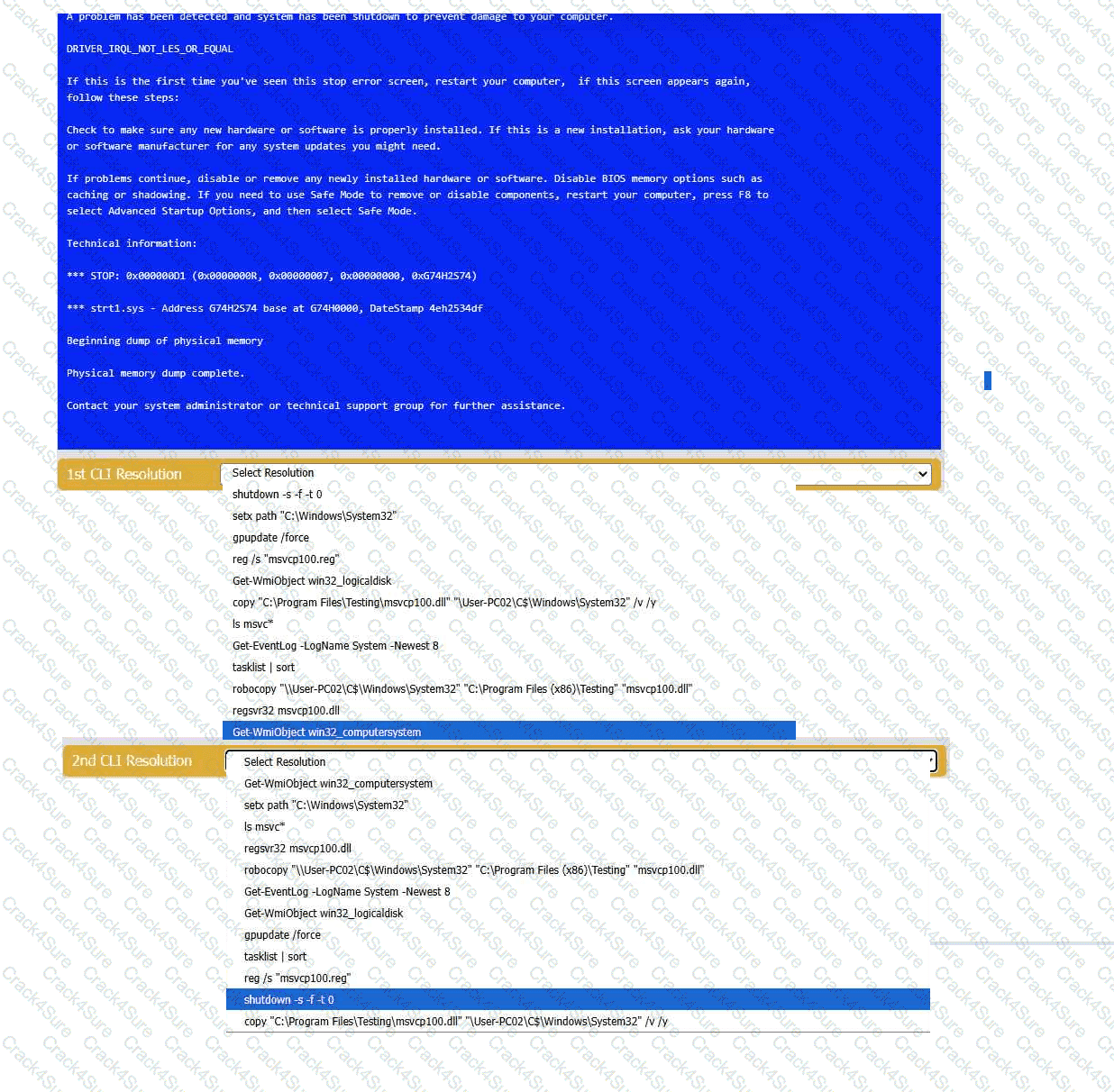
A user reports that after a recent software deployment to upgrade the Testing application, they can no longer use it. However, other employees can successfully
use the Testing program.
INSTRUCTIONS
Review the information in each tab to verify the results of the deployment and resolve
any issues discovered by selecting the:
· First command to resolve the issue
· Second command to resolve the issue
A technician is troubleshooting a print spooler that fails to start on a Windows 11 desktop computer. The technician determines the root cause is that required dependencies are failing to run. Which of the following tools is the technician using?
Which of the following security technologies is designed to enable security visibility and respond to traffic outside of the host and at the network level?
Performance on a user’s smartphone is degrading. Applications take a long time to start, and switching between apps is slow. Which of the following diagnostic steps should a mobile technician take first?
A company wants to use a single operating system for its workstations and servers and avoid licensing fees. Which of the following operating systems would the company most likely select?
A user is trying to install new software. The application downloads successfully, but when the user attempts to install it, the user receives a prompt for credentials. Which of the following would the technician most likely do to resolve this issue?
A secretary receives an email from the company ' s chief executive officer with a request to pay a vendor immediately. After the payment is made, the CEO informs the secretary that they never sent that email. Which of the following social engineering tactics best describes this type of attack?
A company wants to prevent unauthorized physical access to its mobile devices. Which of the following should the company do? (Select two).
A support technician must install software that allows a user to deliver a project status presentation to external stakeholders. Which of the following software types should the technician install?
Which of the following depends on system time accuracy to function properly?
3 Months Free Update
3 Months Free Update
3 Months Free Update