We at Crack4sure are committed to giving students who are preparing for the CompTIA FC0-U61 Exam the most current and reliable questions . To help people study, we've made some of our CompTIA IT Fundamentals+ Certification Exam exam materials available for free to everyone. You can take the Free FC0-U61 Practice Test as many times as you want. The answers to the practice questions are given, and each answer is explained.
Which of the following describes the ability to recover access to a specific account if a credential is forgotten?
A user wants to use a laptop outside the house and still remain connected to the Internet. Which of the
following would be the BEST choice to accomplish this task?
A technician is installing a new wireless network and wants to secure the wireless network to prevent
unauthorized access. Which of the following protocols would be the MOST secure?
Given the following pseudocode:
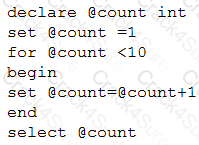
Which of the following is the output of the code?
Which of the following operating systems do not require extensions on files to execute a program? (Select
TWO).
Joe, a developer, is writing a program in which he needs to store a number that changes over the duration of the program’s run. Which of the following would Joe MOST likely use to accomplish this?
Which of the following allows wireless devices to communicate to a wired network?
Which of the following storage devices have a spinning disk? (Choose two.)
Multiple users need to access the same data simultaneously. Which of the following is the best place to store the data?
A user is buying a laptop. The user will have a lot of personal and confidential information on the laptop. The user wants to ensure data cannot be accessed by anyone, even if the laptop is stolen. Which of the following should be set up to accomplish this?
Which of the following is best used to store many integers in one container?
Which of the following software license models allows a developer to modify the original code and release its own version of the application?
Which of the following would most likely be used to verify a user is following an AUP?
Which of the following would be the easiest component to upgrade on a laptop that is experiencing slow performance?
A technician is configuring a new Windows PC and needs to choose a filesystem that supports encryption. Which of the following is the technician most likely to choose?
Consider the following statements:
Given the input (userin) of “analyst”, to which of the following would the clearance variable be set?
A building has two legacy APs. A new AP was recently installed within 30ft (9m) of the legacy APs. Multiple users have been reporting intermittent internet connectivity since the new AP was installed. Which of the following explains what is happening?
A music studio needs to store artist data as text, demos as MP3 files, and sheet music as PDF files in an organized and easily searchable format. Which of the following is best suited to meet this need?
A developer needs to add a table to a database. Which of the following database activities should the user
perform?
In which of the following situations should there be come expectation of privacy?
A technician overhears a systems administrator mention the term “IOPS”. To which of the following operating
system functions would the term BEST apply?
Which of the following is considered a traditional input and output device?
A programmer needs to store output in a place that can be accessed as quickly as possible. The data does not need to remain persistent. Which of the following is the BEST option for storing the data?
A systems administrator wants to return results for a time range within a database. Which of the following
commands should the administrator use?
A company is looking at locations for a new datacenter. The Chief Executive Officer (CEO) has stated that the new datacenter should be at least 500mi (805km) from the existing datacenter so one natural disaster will be unlikely to impact both datacenters. Which of the following is this best an example of?
SQL databases use primary and foreign keys to enable which of the following?
Which of the following is a logical structure for storing files?
A game developer is purchasing a computing device to develop a game and recognizes the game engine
software will require a device with high-end specifications that can be upgraded. Which of the following
devices would be BEST for the developer to buy?
A programmer is generating results by iterating rows that provide values needed for one calculation. Which of the following functions best accomplishes this task?
A company wants an application to be accessed by concurrent users and store company information securely.
Which of the following would be the BEST option for storing the information?
A computer user is downloading software from the Internet and notices the following at the end of the install file: “…x86.exe”. Which of the following statements BEST represents what the “…x86.exe” means in the installation file?
Which of the following requires the MOST frequent updating to remain effective?
Which of the following is a reason why complex passwords are required?
After a user connects a laptop to a newly purchased printer, the user is unable to print. Which of the following is most likely causing the issue?
An employee’s laptop does not connect to the Internet when it is used in a coffee shop. Which of the following
is the MOST likely cause?
A company wants to provide encrypted remote access to its email, file, and application servers to facilitate the ability to work remotely. Which of the following would best fulfill these requirements?
Which of the following would a company consider an asset?
A database administrator would like to create a visual diagram of the layout of a new relational database. Which of the following should the administrator use?
An accounting firm needs to allow users to update records simultaneously without errors. Which of the following best meets the firm's needs?
A company wants to build an application that is available to employees without a client component because some employees do not connect to the corporate network in order to work. Which of the following network types would best deliver this application to all employees?
Which of the following can transmit graphics but not sound?
Which of the following storage types is MOST vulnerable to magnetic damage?
When following the troubleshooting methodology, which of the following should be performed last?
Which of the following would be the most cost-effective method to increase availability?
A user connects a wireless router to a home network and notices another wireless access point uses the same name. Which of the following should the user change?
Ann, a user, is experiencing difficulty getting her IP-based security camera to function at her house after a rain storm that caused a power interruption. The camera has an LED light indicating it has power. Which of the following is MOST likely the problem?
A desktop administrator just connected a printer to a workstation, but the workstation does not recognize the printer. Which of the following does the workstation MOST likely need for the printer to function?
A programmer creates an object to retrieve customer names from a database. Which of the following best describes the object that is retrieving the names?
A program needs to choose apples, oranges, or bananas based on an input. Which of the following
programming constructs is BEST to use?
Which of the following is an example of utilizing a personalized code for continuous personal access to a software product?
A technician reading workstation security logs notices that an unidentified device is plugged into a USB port several hours a day but is never plugged in when the technician goes to check the machine. File audits reveal nothing unexpected. Which of the following devices is most likely causing this message?
Which of the following methods of cooling is most commonly used for desktops?
An IP address is 32 bits long. If converted to bytes, it would be:
NO: 56
A technician needs to install a wireless router for a client that supports speeds up to 11Mbps and operates on the 2.4GHz band. Which of the following should the technician select?
After creating a database, which of the following would a developer most likely use to put data in a table?
A company requires several reports that analyze related information from sales, inventory, marketing, and
compensation data. Which of the following is the BEST place to store this data?
Which of the following BEST describes the physical location of the data in the database?
A business would like to create an employee portal that employees will have access to when they are at work.
The employees will not be able to connect to the portal from home without a VPN connection. Which of the
following types of application does this describe?
A technician wants to reset the boot order on a computer. Which of the following would the technician most likely use?
Which of the following is both an input and output device?
When developing a game, a developer creates a boss object that has the ability to jump. Which of the following
programming concepts does jump represent?
Which of the following is secure?
A product advertising kiosk at a mall is set up using a thin client without a hard drive and is running a web application managed and updated through an internet connection. Which of the following application delivery methods is most likely being used for the kiosk?
Which of the following WiFi security options would create the MOST need for a VPN connection on the client
device?
Which of the following OS features would be best to use to remove unnecessary programs?
A user wants to prevent web history logging. Which of the following features will allow the user to achieve this goal?
Which of the following is the exact number of bytes in a gigabyte?
A user revisits a website and receives a message that the site may not be secure. The user is prompted to click
a link to continue to the site. Which of the following would MOST likely identify the issue?
Which of the following language types most likely controls the way a web page looks?
Which of the following BEST describes a technology that allows multiple users to create and edit reports at the
same time?
Which of the following is a value that uniquely identifies a database record?
Which of the following is required for a cloud network?
Which of the following allows network traffic to pass through it and filters specific packets?
Which of the following is an example of an interpreted language?
Which of the following best practices can be used to mitigate password reuse?
Which of the following is MOST likely used to represent international text data?
Which of the following computer components allows for communication over a computer network?
Which of the following software types is best suited for storing large amounts of data in a way that allows for concurrent, indexed access?
Which of the following security concerns is a threat to confidentiality?
A user is purchasing from an online retailer. The user has entered all the required information and has clicked the "Submit" button, yet the page does not refresh, and the user does not get a confirmation. Which of the following might be the causes of the issue? (Select two).
Which of the following should a technician do to fix stability issues on a workstation?
Which of the following backup types is most likely to allow restoration of a fully bootable computer on new hardware?
A computer technician is assigned a ticket to install a laptop for a new employee. Due to the arrangement of the
workspace, the employee requests that the laptop be installed with the cover closed. Which of the following
would be required to satisfy this request? (Choose two.)
A company has installed an application that only requires a workstation to function. Which of the following
architecture types is this application using?
A database administrator has created a primary table and must ensure the date column in the table only accepts date values. Which of the following does the administrator need to set?
Which of the following defines a reusable value that can be reassigned?
Which of the following describes a unique entry to a data set?
Which of the following is the largest storage capacity?
A remote user, who is working from home, requires significant bandwidth to connect to the corporate systems.
Which of the following types of Internet service connections would BEST meet the user’s needs?
Which of the following types of memory can retain its content after a system reboot?
A network administrator wants to keep track of all system messages and alerts. Which of the following would best allow for the administrator to follow trends?
A programmer uses DML to modify:
Employee information is stored in a database. Which of the following BEST describes where all of an
employee’s information is stored?
The finance department needs software that includes depreciation functionality for asset management. Which of the following types of software would best accomplish this goal?
An application is hosted on a local network. Which of the following descriptions is correct?
A network technician is working on the configuration of a SOHO router. After entering the IP address of the router, the technician uses a GUI to complete the final configuration steps. Which of the following configuration types is this an example of?
Which of the following commands would most likely be used to add data to an existing database table?
A technician is called to replace a display for a workstation. Which of the following would MOST likely be used to connect the display to the workstation?
3 Months Free Update
3 Months Free Update
3 Months Free Update