We at Crack4sure are committed to giving students who are preparing for the CompTIA N10-009 Exam the most current and reliable questions . To help people study, we've made some of our CompTIA Network+ Certification Exam exam materials available for free to everyone. You can take the Free N10-009 Practice Test as many times as you want. The answers to the practice questions are given, and each answer is explained.
A technician is troubleshooting a computer issue for a user who works in a new annex of an office building. The user is reporting slow speeds and intermittent connectivity. The computer is connected via a Cat 6 cable to a distribution switch that is 492ft (150m) away. Which of the following should the technician implement to correct the issue?
Which of the following protocols provides remote access utilizing port 22?
Which of the following is enforced through legislation?
A network technician is attempting to harden a commercial switch that was recently purchased. Which of the following hardening techniques best mitigates the use of publicly available information?
A government entity wants to implement technology that can block websites based on country code. Which of the following will best enable this requirement?
Which of the following ports creates a secure connection to a directory service?
A company is implementing a wireless solution in a high-density environment. Which of the following 802.11 standards is used when a company is concerned about device saturation and converage?
A network engineer added more APs to improve wireless coverage. However, users now report that the connectivity disconnects and reconnects repeatedly. Which of the following is causing the issue?
Which of the following routing technologies allows all users to access the internet using only two public IPs?
Which of the following is most closely associated with having a leased line to a public cloud provider?
A customer calls the help desk to report that resources are no longer reachable. The resources were available before network changes were made. The technician verifies the report, investigates, and discovers that a new logical layout is segmenting the network using tagging. Which of the following appliances most likely needs to be reviewed to restore the connections?
Which of the following is the best way to securely access a network appliance from an external location?
A network administrator needs to connect a multimode fiber cable from the MDF to the server room. The administrator connects the cable to Switch 2, but there is no link light. The administrator tests the fiber and finds it does not have any issues. Swapping the connection to Switch 1 in a working port is successful, but the swapped connection does not work on Switch 2. Which of the following should the administrator verify next?
A network administrator is configuring a network for a new site that will have 150 users. Within the next year, the site is expected to grow by ten users. Each user will have two IP addresses, one for a computer and one for a phone connected to the network. Which of the following classful IPv4 address ranges will be best-suited for the network?
A company experiences an incident involving a user who connects an unmanaged switch to the network. Which of the following technologies should the company implement to help avoid similar incidents without conducting an asset inventory?
Which of the following is the correct order of components in a bottom-up approach for the three-tier hierarchical model?
Which of the following best explains the role of confidentiality with regard to data at rest?
A network engineer configures an application server so that it automatically adjusts resource allocation as demand changes. This server will host a new application and demand is not predictable. Which of the following concepts does this scenario demonstrate?
A network administrator has been monitoring the company ' s servers to ensure that they are available. Which of the following should the administrator use for this task?
A network administrator is planning to host a company application in the cloud, making the application available for all internal and third-party users. Which of the following concepts describes this arrangement?
A network administrator receives complaints of intermittent network connectivity issues. The administrator investigates and finds that the network design contains potential loop scenarios. Which of the following should the administrator do?
Which of the following connection methods allows a network engineer to automate configuration deployment for network devices across the environment?
Which of the following routing protocols uses an autonomous system number?
A network technician is terminating a cable to a fiber patch panel in the MDF. Which of the following connector types is most likely in use?
A user ' s VoIP phone and workstation are connected through an inline cable. The user reports that the VoIP phone intermittently reboots, but the workstation is not having any network-related issues Which of the following is the most likely cause?
A company reports that their facsimile machine no longer has a dial tone when trying to send a fax. The phone cable is damaged on one end. Which of the following types of connectors should a technician replace?
Users usually use RDP to connect to a terminal server with hostname TS19 that points to 10.0.100.19. However, users recently have been unable to connect to TS19. The technician pings 10.0.100.19 and gets an unreachable error. Which of the following is the most likely cause?
A customer wants to separate the finance department from the marketing department. The network administrator suggests segmenting the existing Class C network into two sections and readdressing all devices appropriately. Which of the following subnet masks should the network administrator use?
A network administrator installs a node that requires a media converter to connect Ethernet to fiber but sees no link light on the node. The administrator notices the following:
Both terminating points are properly seated.
Both the fiber and Ethernet cables have been successfully tested.
The media converter is turned on.
The switchport is configured as half duplex.
Which of the following is the reason the link light is not on?
Which of the following panels would be best to facilitate a central termination point for all network cables on the floor of a company building?
A critical infrastructure switch is identified as end-of-support. Which of the following is the best next step to ensure security?
Which of the following connection methods allows a network engineer to automate the configuration deployment for network devices across the environment?
A network administrator is in the process of installing 35 PoE security cameras. After the administrator installed and tested the new cables, the administrator installed the cameras. However, a small number of the cameras do not work. Which of the following is the most reason?
Which of the following technologies is most appropriate for a business that requires high-speed access to frequently used web content, such as images and videos?
A laptop user gets an error when trying to access the company’s intranet site. A technician runs ipconfig /all with the following results:
Autoconfiguration IPv4 Address: 169.254.0.5 (Preferred)
Subnet Mask: 255.255.0.0
Default Gateway:
DHCP Server:
Which of the following is most likely causing the issue?
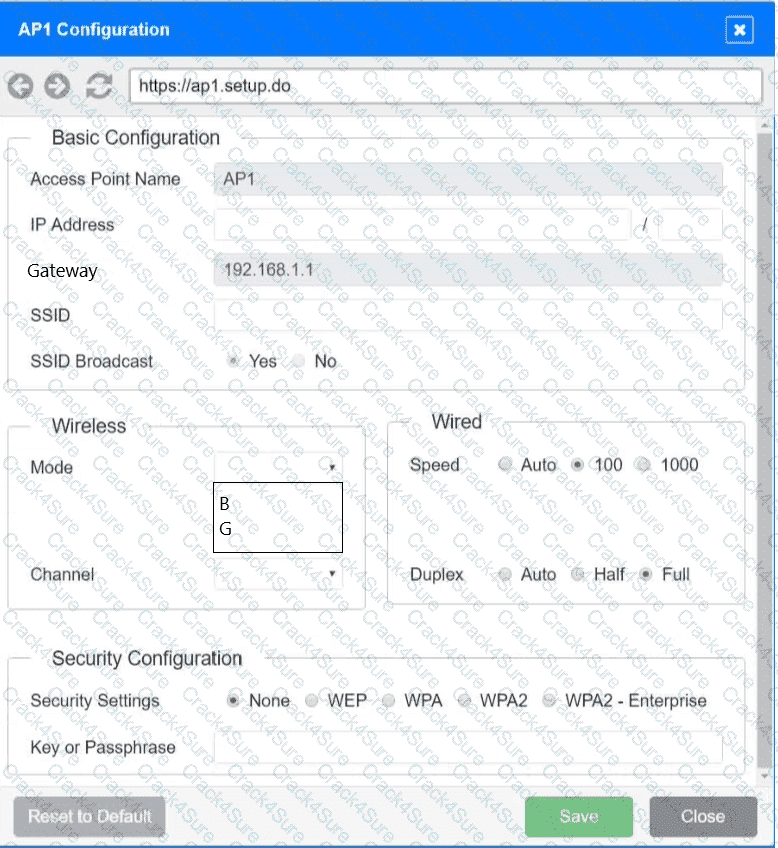
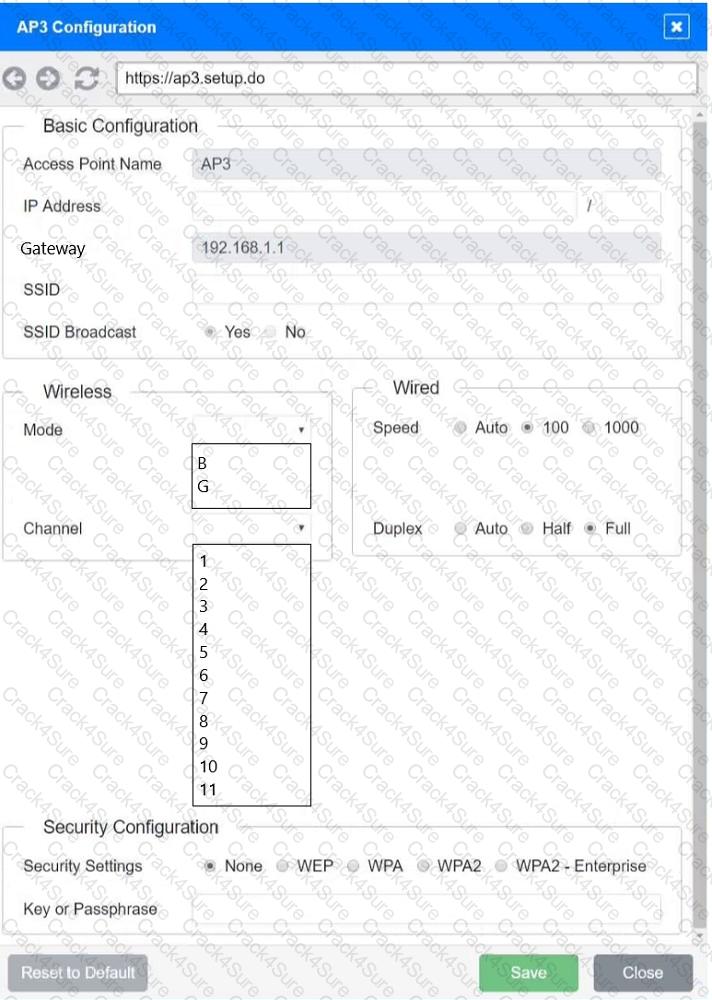
SIMULATION
You have been tasked with setting up a wireless network in an office. The network will consist of 3 Access Points and a single switch. The network must meet the following parameters:
The SSIDs need to be configured as CorpNet with a key of S3cr3t!
The wireless signals should not interfere with each other
The subnet the Access Points and switch are on should only support 30 devices maximum
The Access Points should be configured to only support TKIP clients at a maximum speed
INSTRUCTONS
Click on the wireless devices and review their information and adjust the settings of the access points to meet the given requirements.
If at any time you would like to bring back the initial state of the simulation, please click the Reset All button.
Which of the following layers of the OSI model is responsible for end-to-end encryption?
A detective is investigating an identity theft case in which the target had an RFID-protected payment card issued and compromised in the same day. The only place the target claims to have used the card was at a local convenience store. The detective notices a video camera at the store is placed in such a way that customers ' credentials can be seen when they pay. Which of the following best explains this social engineering technique?
Which of the following ports is used for secure email?
A junior network administrator is auditing the company network and notices incrementing input errors on a long-range microwave interface. Which of the following is the most likely reason for the errors?
Which of the following is the best VPN to use for reducing data bandwidth requirements of the corporate network?
A network technician installs a new 19.7ft (6m), Cat 6, UTP cable for the connection between a server and a switch. Communication to the server is degraded, and the NIC statistics show dropped packets and CRC errors. Which of the following cables would the technician most likely use instead to reduce the errors?
A network administrator wants to update a geofencing policy to limit remote access to the corporate network based on country location. Which of the following would the administrator most likely leverage?
To reduce costs and increase mobility, a Chief Technology Officer (CTO) wants to adopt cloud services for the organization and its affiliates. To reduce the impact for users, the CTO wants key services to run from the on-site data center and enterprise services to run in the cloud. Which of the following deployment models is the best choice for the organization?
Which of the following should a company implement in order to share a single IP address among all the employees in the office?
A customer recently moved into a new office and notices that some wall plates are not working and are not properly labeled Which of the following tools would be best to identify the proper wiring in the IDF?
Which of the following is the most likely reason an insurance brokerage would enforce VPN usage?
A new staff member is unable to connect to the network. An IT support staff member finds the following:
The IP configuration is correct.
The TCP/IP stack is working on the workstation.
The gateway is unreachable.
Which of the following would the IT support staff member most likely check next?
A client wants to increase overall security after a recent breach. Which of the following would be best to implement? (Select two.)
Which of the following cloud platform technology characteristics would a quantum computing host most likely prioritize?
A network engineer is configuring network ports in a public office. To increase security, the engineer wants the ports to allow network connections only after authentication. Which of the following security features should the engineer use?
Which of the following are environmental factors that should be considered when installing equipment in a building? (Select two).
Which of the following allows a remote user to connect to the network?
A systems administrator is configuring a new device to be added to the network. The administrator is planning to perform device hardening prior to connecting the device. Which of the following should the administrator do first?
After installing a new 6E wireless router in a small office, a technician notices that some wireless devices are not able to achieve the rated speeds.
Which of the following should the technician check to troubleshoot the issue? (Select two)
A company wants to implement data loss prevention by restricting user access to social media platforms and personal cloud storage on workstations. Which of the following types of filtering should the company deploy to achieve these goals?
An administrator wants to find the top destination for traffic across the infrastructure on a specific day. Which of the following should the administrator use?
A company is hosting a secure that requires all connections to the server to be encrypted. A junior administrator needs to harded the web server. The following ports on the web server. The following ports on the web server are open:

Which of the following ports should be disabled?
A network administrator is implementing security zones for each department. Which of the following should the administrator use to accomplish this task?
A customer needs six usable IP addresses. Which of the following best meets this requirement?
A group of users cannot connect to network resources. The technician runs ipconfig from one user ' s device and is able to ping the gateway shown from the command. Which of the following is most likely preventing the users from accessing network resources?
A network administrator installs new cabling to connect new computers and access points. After deploying the equipment, the administrator notices a few of the devices are not connecting properly. The administrator moves the devices to a different port, but it does not resolve the issue. Which of the following should the administrator verify next?
While troubleshooting connectivity issues, a junior network administrator is given explicit instructions to test the host ' s TCP/IP stack first. Which of the following commands should the network administrator run?
A network administrator is troubleshooting a connection issue and needs to determine the path that a packet will take. Which of the following commands accomplishes this task?
After installing a new wireless access point, an engineer tests the device and sees that it is not performing at the rated speeds. Which of the following should the engineer do to troubleshoot the issue? (Select two.)
Which of the following attacks would most likely cause duplicate IP addresses in a network?
A customer calls the help desk to report issues connection to the internet. The customer can reach a local database server. A technician goes to the site and examines the configuration:
Which of the following is causing the user ' s issue?
Which of the following allows the fastest recovery during a catastrophe event?
A media company is implementing a global streaming service. Which of the following should the company apply to each regional point of presence in order to comply with local laws?
An ISP provided a company with a pre-configured modem and five public static IP addresses. Which of the following does the company ' s firewall require to access the internet? (Select TWO).
An organization requires the ability to send encrypted email messages to a partner from an email server that is hosted on premises. The organization prefers to use the standard default ports when creating firewall rules. Which of the following ports should be open to satisfy the requirements?
Users are reporting latency on the network. The network engineer notes the following:
Confirms the only change was a new network switch
Confirms all users are experiencing latency
Thinks the issue is a network loop caused by the lower bridge ID of the new switch
Which of the following describes the next step in the troubleshooting methodology?
A network administrator needs to locate a specific AP using a spectrum analyzer to complete an 802.11ax device migration. Which of the following should display on the analyzer to locate the AP?
Due to concerns around single points of failure, a company decided to add an additional WAN to the network. The company added a second MPLS vendor to the current MPLS WAN and deployed an additional WAN router at each site. Both MPLS providers use OSPF on the WAN network, and EIGRP is run internally. The first site to go live with the new WAN is successful, but when the second site is activated, significant network issues occur. Which of the following is the most likely cause for the WAN instability?
A network administrator wants to increase network security by preventing client devices from communicating directly with each other on the same subnet. Which of the following technologies should be implemented?
A technician needs to quickly set up a network with five wireless devices. Which of the following network types should the technician configure to accomplish this task?
A user cannot access an external server for a client after connecting to a VPN. Which of the following commands would a support agent most likely use to examine the issue? (Select two).
Which of the following would be violated if an employee accidentally deleted a customer ' s data?
Which of the following is a use case for a PaaS environment?
A network administrator upgraded the wireless access points and wants to implement a configuration that will give users higher speed and less channel overlap based on device compatibility. Which of the following will accomplish this goal?
A network engineer receives a vendor alert regarding a vulnerability in a router CPU. Which of the following should the engineer do to resolve the issue?
After a security incident, a technician reveals that company data was stolen. During the investigation, it is discovered that a host disguised itself as a switch. Which of the following best describes the attack that occurred?
A network administrator upgrades the wireless access points and wants to implement a configuration that gives users higher speed and less channel overlap based on device compatibility. Which of the following accomplishes this goal?
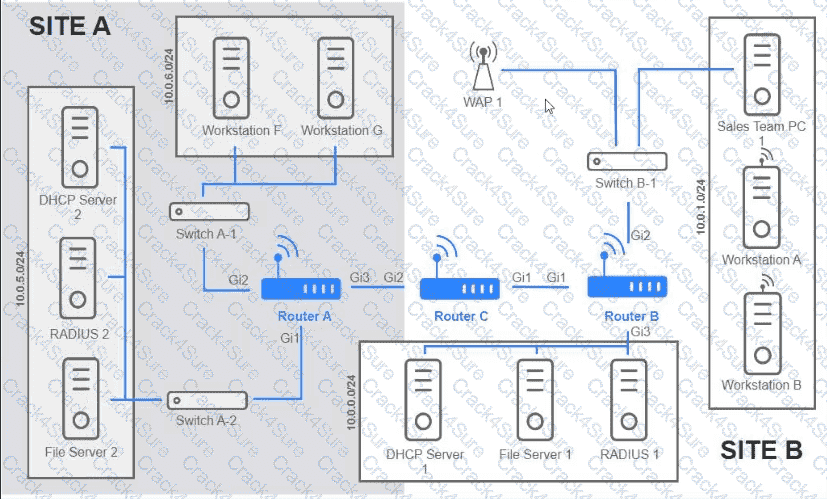
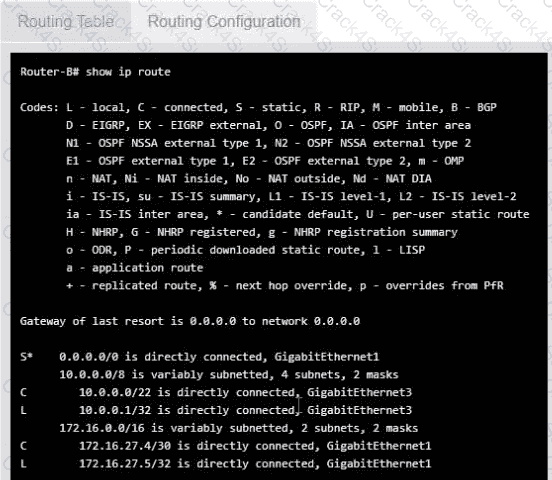
Users are unable to access files on their department share located on flle_server 2. The network administrator has been tasked with validating routing between networks hosting workstation A and file server 2.
INSTRUCTIONS
Click on each router to review output, identity any Issues, and configure the appropriate solution
If at any time you would like to bring back the initial state of trie simulation, please click the reset All button;
A network rack has four servers and four switches with dual power supplies. Only one intelligent PDU is installed in the rack. Which of the following is the reason to add a second PDU?
A network administrator performed upgrades on a server and installed a new NIC to improve performance. Following the upgrades, usera are unable to reach the server. Which of the following is the most likely reason.
Which of the following connector types would most likely be used to connect to an external antenna?
A network engineer is designing an internal network that needs to support both IPv4 and IPv6 routing. Which of the following routing protocols is capable of supporting both IPv4 and IPv6?
Which of the following cable types allows the use of QSFP ports without requiring transceivers?
A network engineer is completing a wireless installation in a new building. A requirement is that all clients be able to automatically connect to the fastest supported network. Which of the following best supports this requirement?
A company is expanding to another floor in the same building. The network engineer configures a new switch with the same VLANs as the existing stack. When the network engineer connects the new switch to the existing stack, all users lose connectivity. Which of the following is the MOST likely reason?
Which of the following steps in the troubleshooting methodology comes after using a top-to-top buttom examination of the OSI model to determine cause?
A network administrator wants to implement security zones in the corporate network to control access to only individuals inside of the corporation. Which of the following security zones is the best solution?
Which of the following recovery strategies should a company implement to ensure data center services are quickly restored and accessible after a disaster occurs?
Which of the following allows a network administrator to analyze attacks coming from the internet without affecting latency?
Which of the following does a full-tunnel VPN provide?
An IT department asks a newly hired employee to use a personal laptop until the company can provide one. Which of the following policies is most applicable to this situation?
A company is concerned that the public can use network wall jacks in publicly available conference rooms to access company servers. Which of the following is the best way to mitigate the vulnerability?
Two companies successfully merged. Following the merger, a network administrator identified a connection bottleneck. The newly formed company plans to acquire a high-end 40GB switch and redesign the network from a three-tier model to a collapsed core. Which of the following should the administrator do until the new devices are acquired?
A newtwork administrator needs to create an SVI on a Layer 3-capable device to separate voice and data traffic. Which of the following best explains this use case?
Which of the following is used to estimate the average life span of a device?
Which of the following is a cost-effective advantage of a split-tunnel VPN?
Which of the following offers the ability to manage access at the cloud VM instance?
Which of the following terms describes the capability in a public cloud to add or remove compute resources based on need?
A network administrator needs to implement a solution to filter access to the internet. Which of the following should the administrator most likely implement?
Which of the following protocol ports should be used to securely transfer a file?
Which of the following can also provide a security feature when implemented?
Which of the following is a type of NAC that uses a set of policies to allow or deny access to the network based on the user’s identity?
A network engineer queries a hostname using dig, and a valid IP address is returned. However, when the engineer queries that same IP address using dig, no hostname is returned. Which of the following DNS records is missing?
A network administrator is notified that a user cannot access resources on the network. The network administrator checks the physical connections to the workstation labeled User 3 and sees the Ethernet is properly connected. However, the network interface’s indicator lights are not blinking on either the computer or the switch. Which of the following Is the most likely cause?
A user tries to visit a website, but instead of the intended site, the page displays vmw.cba.com. Which of the following should be done to reach the correct website?
A network manager connects two switches together and uses two connecting links. Which of the following configurations will prevent Layer 2 loops?
A network technician is troubleshooting the connection to the company website. The traceroute command produces the following output:
Traceroute towww.mysite.com(8.8.8.8) over a maximum of 30 hops
10.1.1.1 < 1 ms 2. * < 1 ms < 1 ms
k k
k kTraceroute completeWhich of the following should the technician do to identify the path to the server?
Which of the following is created to illustrate the effectiveness of wireless networking coverage in a building?
Which of the following is used to redistribute traffic between one source and multiple servers that run the same service?
Which of the following VPN configurations forces a remote user to access internet resources through the corporate network?
A systems administrator is investigating why users cannot reach a Linux web server with a browser but can ping the server IP. The server is online, the web server process is running, and the link to the switch is up. Which of the following commands should the administrator run on the server first?
Which of the following network access methods is used to securely access resources, such as a corporate cloud or network, as if they were directly connected?
A network administrator deploys several new desk phones and workstation cubicles. Each cubicle has one assigned switchport. The administrator runs the following commands:
nginx
CopyEdit
switchport mode access
switchport voice vlan 69
With which of the following VLANs will the workstation traffic be tagged?
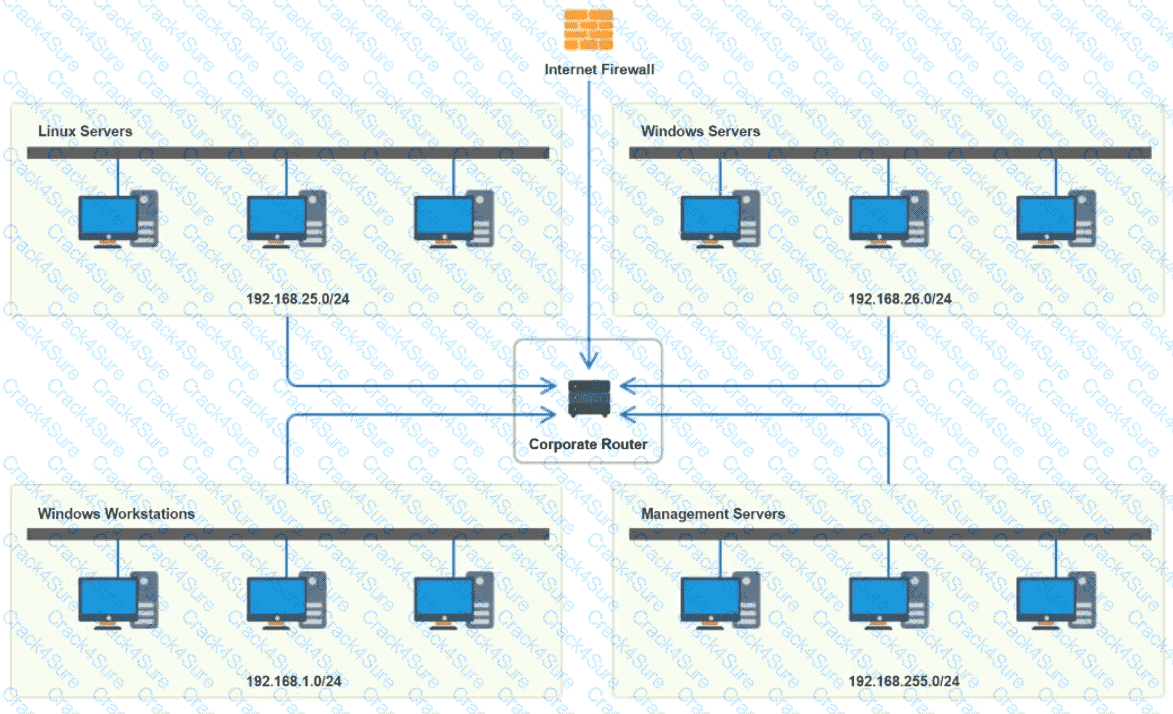
You have been tasked with implementing an ACL on the router that will:
1. Permit the most commonly used secure remote access technologies from the management network to all other local network segments
2. Ensure the user subnet cannot use the most commonly used remote access technologies in the Linux and Windows Server segments.
3. Prohibit any traffic that has not been specifically allowed.
INSTRUCTIONS
Use the drop-downs to complete the ACL
If at any time you would like to bring back the initial state of the simulation, please click the Reset All button.
A network administrator needs to limit devices that can connect to a small wireless network. The network consists of less than ten unique laptops, and no network changes are anticipated. Which of the following is the simplest way to accomplish this task?
A network engineer is completing a new VoIP installation, but the phones cannot find the TFTP server to download the configuration files. Which of the following DHCP features would help the phone reach the TFTP server?
A network engineer needs to virtualize network services, including a router at a remote branch location. Which of the following solutions meets the requirements?
A network architect of a stock exchange broker is implementing a disaster recovery (DR), high-availability plan. Which of the following approaches would be the best fit?
Which of the following steps of the troubleshooting methodology would most likely involve comparing current throughput tests to a baseline?
Which of the following source control features allows an administrator to test a new configuration without changing the primary configuration?
A client with a 2.4GHz wireless network has stated that the entire office is experiencing intermittent issues with laptops after the WAP was moved. Which of the following is the most likely reason for these issues?
A network engineer performed a migration to a new mail server. The engineer changed the MX record, verified the change was accurate, and confirmed the new mail server was reachable via the IP address in the A record. However, users are not receiving email. Which of the following should the engineer have done to prevent the issue from occurring?
A network administrator notices interference with industrial equipment in the 2.4GHz range. Which of the following technologies would most likely mitigate this issue? (Select two).
Which of the following network ports is used when a client accesses an SFTP server?
Which of the following allows a user to authenticate to multiple resources without requiring additional passwords?
A network technician needs to configure IP addressing in a Class C network with eight subnets total:
Three subnets for 60 hosts
Three subnets for 15 hosts
Two subnets for seven hosts
Which of the following solutions should the technician use to accomplish this task?
Which of the following should a network administrator configure when adding OT devices to an organization’s architecture?
The leadership team is updated on the results of an approved change request after a breach. Which of the following troubleshooting methodology steps is described in this example?
A network administrator for a small office is adding a passive IDS to its network switch for the purpose of inspecting network traffic. Which of the following should the administrator use?
A network engineer needs to add a boundary network to isolate and separate the internal network from the public-facing internet. Which of the following security defense solutions would best accomplish this task?
A network administrator recently upgraded a wireless infrastructure with new APs. Users report that when stationary, the wireless connection drops and reconnects every 20 to 30 seconds. While reviewing logs, the administrator notices the APs are changing channels.
Which of the following is the most likely reason for the service interruptions?
Network administrators are using the Telnet protocol to administer network devices that are on the 192.168.1.0/24 subnet. Which of the following tools should the administrator use to best identify the devices?
A network administrator needs to connect two routers in a point-to-point configuration and conserve IP space. Which of the following subnets should the administrator use?
A company is implementing a new internal network in which all devices use IPv6 addresses. Which of the following routing protocols will be best for this setup?
A technician is troubleshooting wireless connectivity near a break room. Whenever a user turns on the microwave, connectivity to the user ' s laptop is lost. Which of the following frequency bands is the laptop most likely using?
Which of the following must be implemented to securely connect a company ' s headquarters with a branch location?
Which of the following allows for the interception of traffic between the source and destination?
A network administrator wants to restrict inbound traffic to allow only HTTPS to the company website, denying all other inbound traffic from the internet. Which of the following would best accomplish this goal?
A network technician is troubleshooting a faulty NIC and tests the theory. Which of the following should the technician do next?
After providing a username and password, a user must input a passcode from a phone application. Which of the following authentication technologies is used in this example?
A company is migrating a data center from on premises to the cloud. Which of the following tools will help maintain consistency, reliability, and efficiency of provisioning and management?
A small company has the following IP addressing strategy:
A user is unable to connect to the company fileshare server located at 192.168.10.1. The user’s networking configuration is:
Which of the following will most likely correct the issue?
Which of the following allows a standard user to log in to multiple resources with one account?
A company has been added to an unapproved list because of spam. The network administrator confirmed that a workstation was infected by malware. Which of the following processes did the administrator use to identify the root cause?
Which of the following most likely requires the use of subinterfaces?
A firewall administrator is mapping a server ' s internal IP address to an external IP address for public use. Which of the following is the name of this function?
A network engineer connects a business to a new ISP. A simple ping test to 8.8.8.8 is successful. However, users complain of extreme slowness to any website and periods of no connectivity. Which of the following is the most likely cause?
A network technician receives a new ticket while working on another issue. The new ticket is critical to business operations. Which of the following documents should the technician reference to determine which ticket to complete first?
Which of the following is the best way to reduce the likelihood of electrostatic discharge?
Three new employees report that they are unable to access company resources, but they can connect to each other’s devices. Which of the following would most likely need to be modified to resolve the issue?
Which of the following connectors provides console access to a switch?
Which of the following is used to store and deliver content to clients in a geographically distributed manner using edge servers?
A network administrator is looking for a solution to extend Layer 2 capabilities and replicate backups between sites. Which of the following is the best solution?
A network administrator changed an external DNS to point customers to a new server. Which of the following tools should the administrator use to test the new server ' s configuration?
3 Months Free Update
3 Months Free Update
3 Months Free Update