We at Crack4sure are committed to giving students who are preparing for the Microsoft MS-203 Exam the most current and reliable questions . To help people study, we've made some of our Microsoft 365 Messaging exam materials available for free to everyone. You can take the Free MS-203 Practice Test as many times as you want. The answers to the practice questions are given, and each answer is explained.
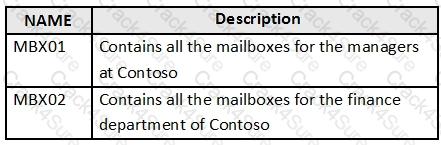
Your company named Contoso, Ltd. has a Microsoft Exchange Server 2019 organization that contains the mailbox databases shown in the following table.
You need to assign an offline address book (OAB) named Managers to all the users in a group named Managers.
How should you complete the PowerShell script? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.
You need to configure the required objects for the branch office administrators.
What should you create for each administrator?
You have a Microsoft Exchange Online tenant that contains 1,000 users.
You need to prevent 100 users in the finance department at your company from using Direct file access when using Outlook on the web. The solution must ensure that all the other users in the company can continue to use Direct file access when using Outlook on the web.
What should you do?
NO: 27
Your network contains an Active Directory domain named corp.contoso.com. The domain contains client computers that have Microsoft Office 36S Apps installed. You have a hybrid deployment that contains a Microsoft Exchange Online tenant and an on-premises Exchange Server 2019 server named Server1. All recipients use an email address suffix of Contoso.com.
You migrate all the Exchange Server recipients to Exchange Online, and then decommission Server1.
Users connected to the internal network report that they receive an Autodiscover error when they open Microsoft Outlook.
You need to ensure that all users can connect successfully to their mailbox by using Outlook.
Which two actions should you perform? Each correct answer presents a complete solution.
NOTE: Each correct selection is worth one point.
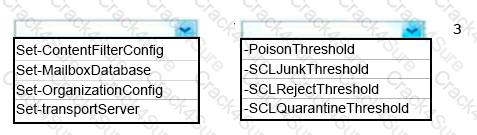
You need to implement a solution to meet the technical requirements for the SCL.
How should you complete the command? To answer, select the appropriate options in the answer area.
You need to resolve the issue for the transport department users.
What is the best way to achieve the goal? More than one answer choice may achieve the goal. Select the
BEST answer.
You need to implement a solution to support the planned changes for the branch office administrators.
What should you do?
You need to implement a solution to support the planned changes for the helpdesk users.
What should you do?
Your company has a Microsoft 365 subscription for a domain named contoso.com.
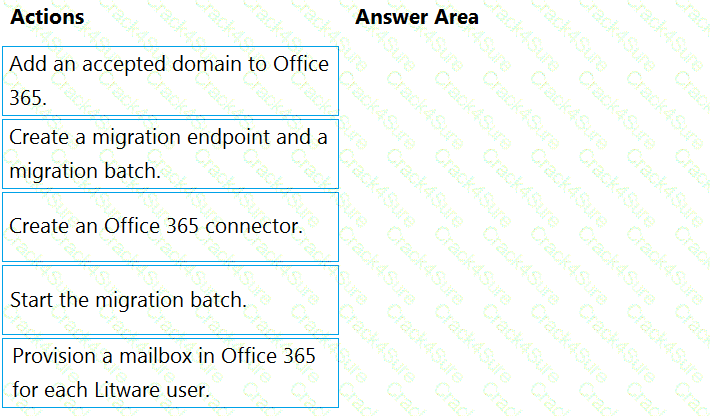
The company acquires a company named Litware, Inc. that uses an IMAP-based messaging system. The SMTP domain of Litware is named litwareinc.com.
You need to migrate the mailboxes of Litware to Microsoft Office 365. The solution must ensure that users from Litware can receive email by using their current email address.
Which four actions should you perform in sequence? To answer, move the appropriate actions from the list of actions to the answer area and arrange them in the correct order.
Your company has a Microsoft Exchange Server 2019 organization.
You are auditing the Litigation Hold on the mailboxes of the company’s research and development
department.
You discover that the mailbox of a user named User1 has a Litigation Hold enabled.
You need to discover who placed the Litigation Hold on the mailbox of User1, and when the Litigation Hold was enabled.
Which two actions should you perform? Each correct answer presents part of the solution.
NOTE: Each correct selection is worth one point.
You have a Microsoft Exchange Online tenant that contains a user named User1.
You need to ensure that User1 can create, manage, and remove Exchange recipient objects.
What should you assign to User1?
You have a Microsoft Exchange Online tenant.
You need to identify any changes made to the Recipient Management role group during the past month.
What should you do?
You have a hybrid deployment between a Microsoft Exchange Online tenant and an on-premises Exchange Server 2019 organization.
Users report that emails sent from Exchange Online mailboxes to the on-premises Exchange Server mailboxes are undelivered.
You need to review the non-delivery report (NDR) for each undelivered email.
What should you use?
You have a Microsoft Exchange Online tenant that contains a public folder named PF1.
You need to ensure that email sent to pf1@contoso.com is posted to PF1.
What should you do?
You have a hybrid deployment that contains a Microsoft Exchange Online tenant and an on-premises Exchange Server 2019 server named Server1.
Server1 uses a certificate from a third-party certification authority (CA). The certificate is enabled for the SMTP service.
You replace the certificate with a new certificate.
You discover that delivery fails for all email messages sent from Server1 to your Microsoft 365 tenant.
You receive the following error message for all the queued email messages: “450 4.4.101 Proxy session setup failed on Frontend with 451 4.4.0 Primary target IP address responded with 451 5.7.3 STARTTLS is required to send mail.”
You need to ensure that the messages are delivered successfully from Server1 to the Microsoft 365 tenant.
What should you do?
You need to recommend a solution for the public folders that supports the planned changes and meets the technical requirements.
What should you recommend?
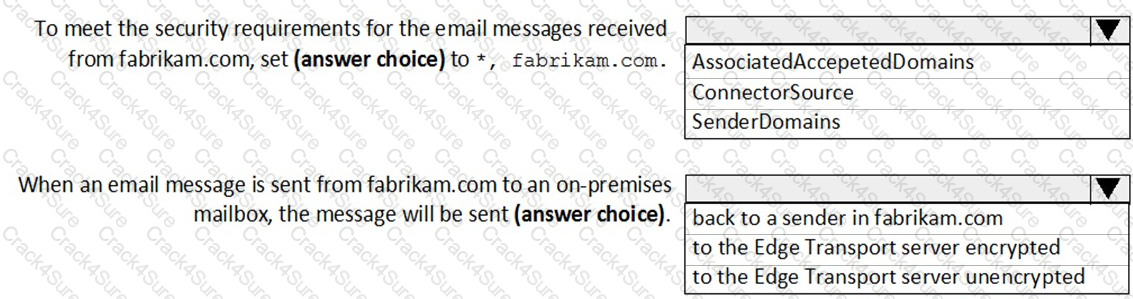
Use the drop-down menus to select the answer choice that complete each statement based on the information presented in the Exchange Online Connector exhibit.
NOTE: Each correct selection is worth one point.
You need to recommend a solution that meets the security requirements for protecting users.
What should you recommend?
You have an Exchange Online tenant that contains several hundred mailboxes.
Several users report that email messages from an SMTP domain named @fabrikam.com often fail to be delivered to their mailbox.
You need to increase the likelihood that the email messages from the @fabrikam.com are delivered successfully to the users in the tenant.
Which contacts can sign in to and access resources in the adatum.com tenant?
You need to recommend an Office 365 solution that meets the technical requirements for email from adatum.com.
Which two components should you recommend configuring from the Exchange admin center in Exchange Online? Each correct presents a complete solution.
NOTE: Each correct selection is worth one point.
Joni Sherman reports that the Microsoft Outlook client on her Windows 10 device fails to start.
You need to troubleshoot the issue.
From the device, you start the Microsoft Remote Connectivity Analyzer.
What should you run next?
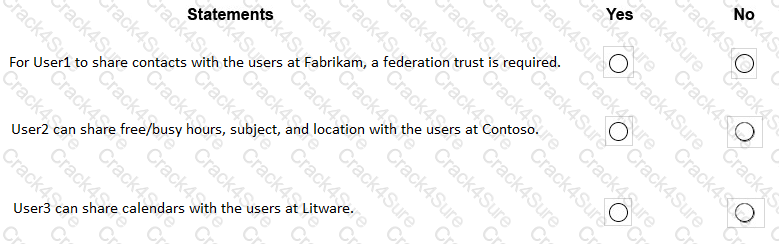
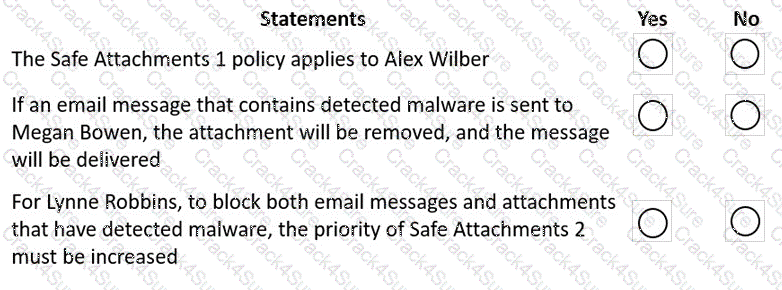
For each of the following statements, select Yes if the statement is true. Otherwise, select No.
NOTE: Each correct selection is worth one point.
You need to email a list of configuration changes to the Exchange Online environment that were recently performed by Allan Deyoung.
What should you do?
Allan Deyoung must perform a message trace of the email messages sent by Isaiah Langer and provide a report that contains all the messages sent during the last 30 days.
You need to ensure that Allan Deyoung can perform the message trace.
What should you do?
You need to ensure that Allan Deyoung can create a new public folder for the sales department.
Which two actions should you perform first? Each correct answer presents part of the solution.
NOTE: Each correct selection is worth one point.
Lynne Robbins and the users in the sales department plan to collaborate on a project with a partner company named Contoso, Ltd. that has an email domain named contoso.com.
You need to ensure that only the sales department users can share all their calendar free/busy
information with the users in contoso.com.
How should you configure the organization relationship?
You need to ensure that Alex Wilber can recover deleted items when using Outlook on the web.
Which two actions should you perform? Each correct answer presents a complete solution.
NOTE: Each correct selection is worth one point.
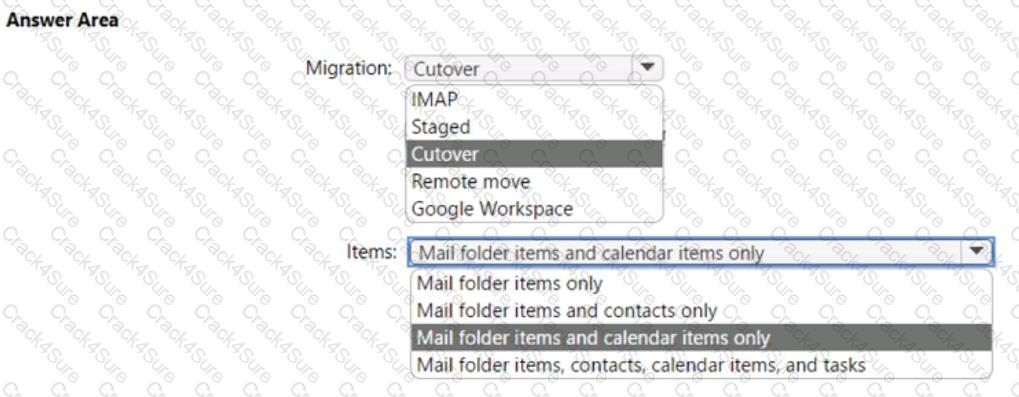
You need to migrate 10 Microsoft Outlook.com users to the adatum.com tenant.
Which type of migration should you perform, and which items can be migrated? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.
You discover that email messages sent to contoso.com are NOT delivered through Contoso Connector.
You need to ensure that all email sent to contoso.com is delivered through Contoso Connector.
Which connector setting should you modify?
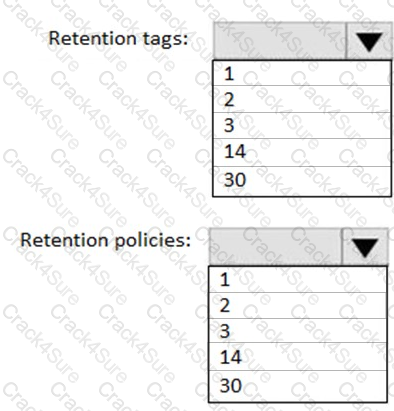
You need to implement a solution that meets the technical requirements for the retention of junk email, sent items, and deleted items.
What is the minimum number of retention policies and retention tags you should use? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.
You need to recommend a solution to retain the items in the public folders. The solution must support the
planned changes.
What should you recommend?
You need to resolve the issue for the customer service department users.
What should you modify?
You need to recommend a procedure for closing the Brussels office that meets the technical requirements.
What should you recommend?
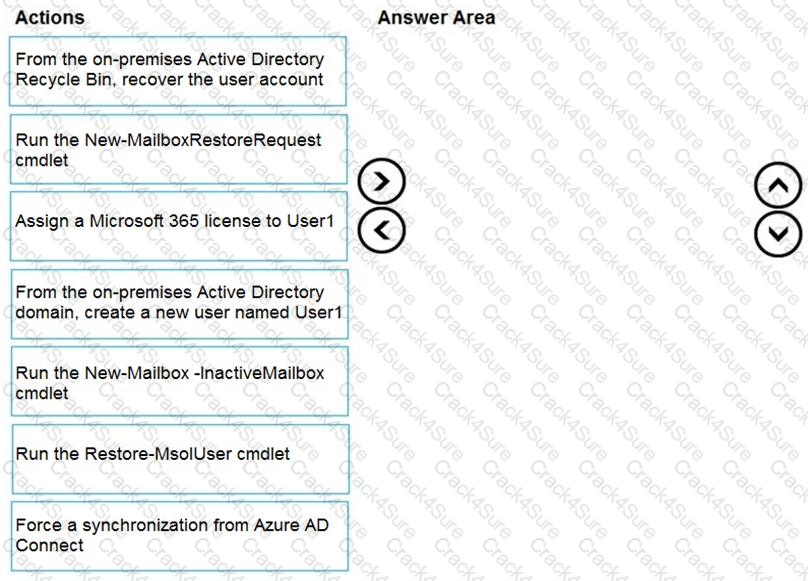
You have a hybrid deployment between Microsoft Exchange Online and on-premises Exchange Server 2019.
All user mailboxes are in Microsoft 365.
A user named User1 leaves your company.
You delete the user account of User1 from the on-premises Active Directory domain.
Two weeks later, User1 returns to the company.
You need to ensure that User1 can connect to his mailbox and access all his old email messages.
Which three actions should you perform in sequence? To answer, move the appropriate actions from the list of actions to the answer area and arrange them in the correct order.
Note: This question is part of a series of questions that present the same scenario. Each question in the series contains a unique solution that might meet the stated goals. Some question sets might have more than one correct solution, while others might not have a correct solution.
After you answer a question in this section, you will NOT be able to return to it. As a result, these questions will not appear in the review screen.
You have a Microsoft Exchange Online tenant that contains the following email domains:
When external recipients receive email messages from the users in the tenant, all the messages are delivered by using the @contoso.com email domain.
You need to ensure that the users send email by using the @fabrikam.com email domain.
Solution: You modify the properties of the fabrikam.com accepted domain.
Does this meet the goal?
Your network contains an Active Directory domain named fabrikam.com.
You have a Microsoft Exchange Server 2019 organization that contains two Mailbox servers in a database availability group (DAG).
You plan to implement a hybrid deployment by using the Exchange Modern Hybrid connection option.
Which three configurations will be transferred automatically from the on-premises organization to Exchange Online? Each correct answer presents part of the solution.
NOTE: Each correct selection is worth one point.
You have a Microsoft 365 subscription that contains a user named User1.
You need to ensure that User1 can only manage eDiscovery cases that she creates and export the search results. The solution must use the principle of least privilege.
To which role should you add User1?
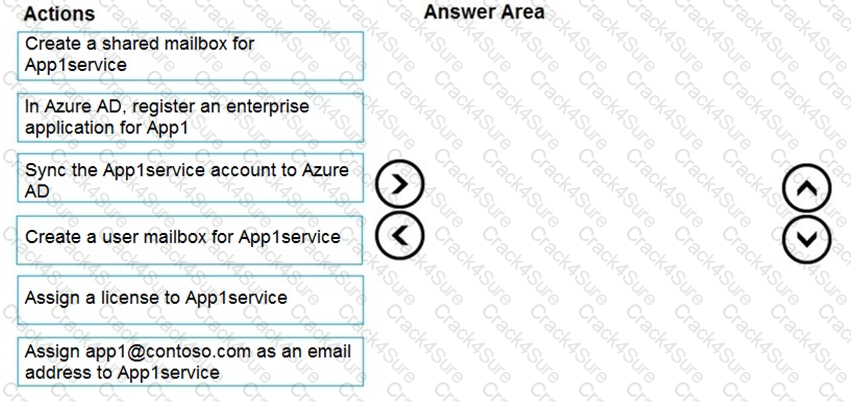
Your network contains an Active Directory domain and an Azure Active Directory (Azure AD) tenant in a hybrid deployment.
You implement a Microsoft Exchange Online tenant.
You plan to deploy a new on-premises app named App1 to a Windows server. The solution must meet the following requirements:
In the domain, you create App1service.
Which three actions should you perform in sequence? To answer, move the appropriate actions from the list of actions to the answer area and arrange them in the correct order.
Note: This question is part of a series of questions that present the same scenario. Each question in the series contains a unique solution that might meet the stated goals. Some question sets might have more than one correct solution, while others might not have a correct solution.
After you answer a question in this section, you will NOT be able to return to it. As a result, these questions will not appear in the review screen.
You have a Microsoft Exchange Server 2019 organization that contains 200 mailboxes.
You need to add a second email address to each mailbox. The address must have a syntax that uses the first letter of each user’s last name, followed by the user’s first name, and then @fabrikam.com.
Solution: You create an email address policy that uses the %1g%s@fabrikam.com email address format.
Does this meet the goal?
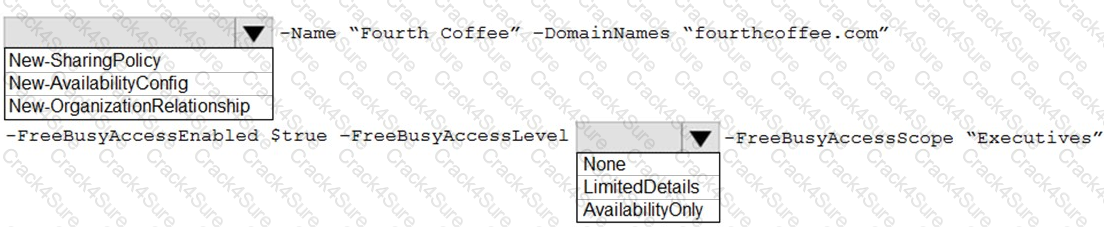
Your company has an Exchange Online tenant.
A partner company named Fourth Coffee also uses Exchange Online.
You need to ensure that the users at your company share free busy information with the users at Fourth Coffee. The solution must ensure that the meeting details included in the calendars of your company users remain hidden from the Fourth Coffee users.
How should you complete the command? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.
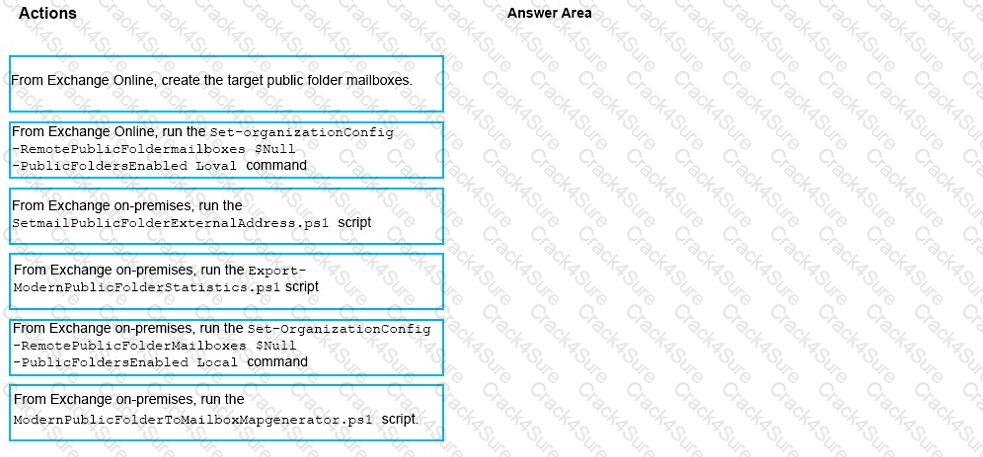
You have a Microsoft Exchange Server 2019 hybrid deployment.
All user mailboxes are migrated to Exchange Online.
You need to migrate the public folders from the on-premises organizations to Exchange Online.
Which three actions should you perform in sequence before you create the migration batch? To answer, move the appropriate actions from the list of actions to the answer area and arrange them in the correct order.
You have a Microsoft Exchange Online tenant that contains a user named User1.
You need to ensure that User1 can perform the following tasks from the Microsoft Purview compliance portal:
• Create, edit, delete, and control access to Core eDiscovery cases.
• Use Content search to bulk delete email messages.
The solution must follow the principle of least privilege. To which role group should you add User1?
User3 leaves the company.
You need to ensure that Admin1 and Admin2 can access the mailbox of User3. The solution must meet the technical requirements.
What should you do?
You need to identify which users clicked the links in the phishing emails.
What should you do?
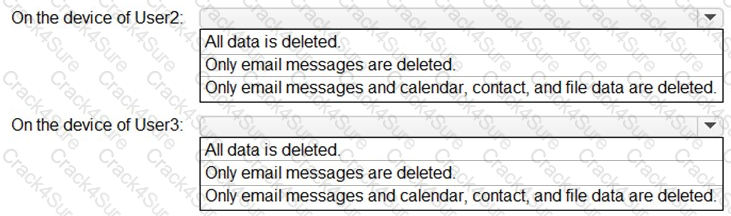
You need to perform a remote wipe of the devices of User2 and User3.
You run the following commands.
Clear-MobileDevice -id User2-Device
-NotificationEmailAddress "admin@Fabrikam.com"
Clear-MobileDevice -id User3-Device
-NotificationEmailAddress "admin@Fabrikam.com"
What occurs on each device? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.
You need to generate a report for the mobile devices that meets the technical requirements.
Which PowerShell cmdlet should you use?
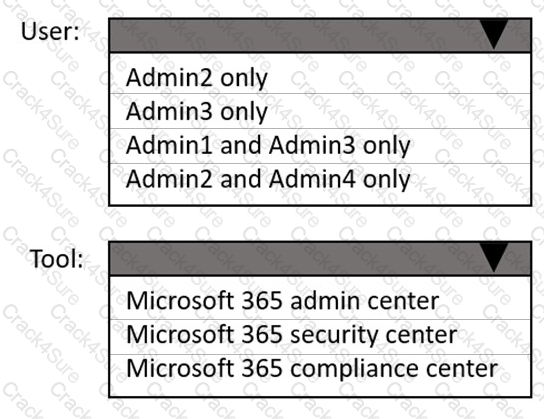
You need to ensure that In-Place Archiving is enabled for the marketing department users.
Which user should perform the change, and which tool should the user use? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.
You need to identify the contents of the FabrikamProject public folder to meet the technical requirements.
Which PowerShell cmdlet should you run?
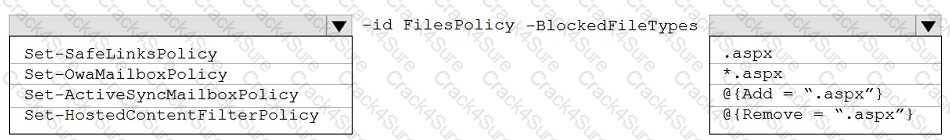
You need to modify FilesPolicy to prevent users from downloading ASPX files. The solution must meet the technical requirements.
How should you complete the command? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.
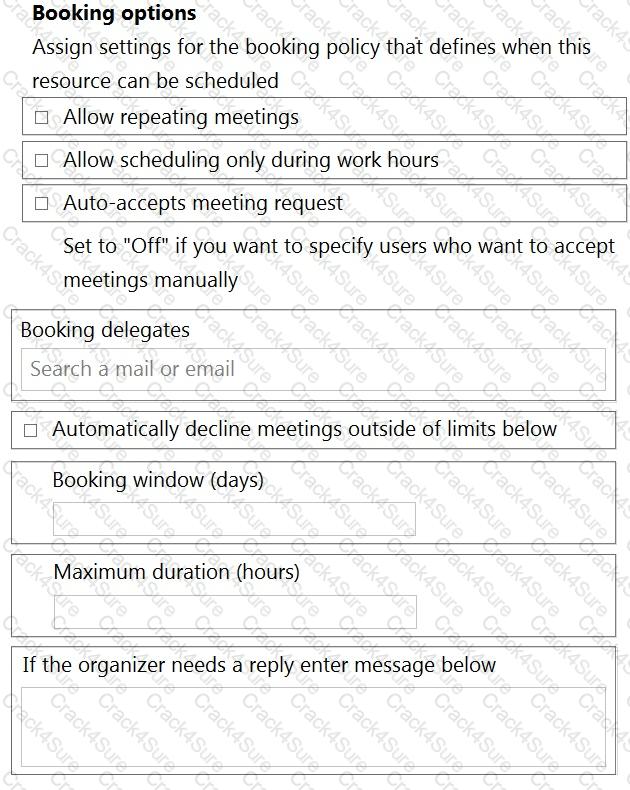
You need to configure the new smartboard to support the planned changes.
Which three settings should you configure? To answer, select the appropriate settings in the answer area.
NOTE: Each correct selection is worth one point.
You need to encrypt email between Fabrikam and Litware to support the planned changes.
What should you configure in the Exchange admin center?
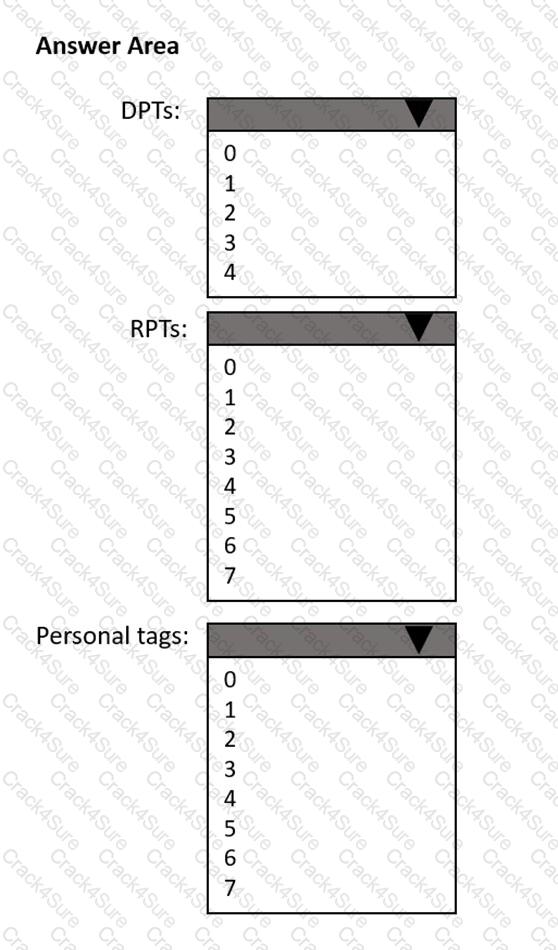
How many default policy tags (DPTs), retention policy tags (RPTs), and personal tags should you create to meet the retention requirements? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.
3 Months Free Update
3 Months Free Update
3 Months Free Update